This issue is due to the implementation of frequency scaling on AMD processors that may leave out functionality to properly synchronize the frequency of the processor with the frequency of the system memory. This may leave out protection against the race condition where two out-of-order execution paths may arrive at a memory location with different timings and may result in information disclosure. Unfortunately, there is currently no mitigation against this issue on AMD processors.
Another potential issue with AMD processors using out-of-order execution may be the issue of speculative execution. Speculative execution is a potential issue for many modern CPUs as it allows a CPU to make decisions about the control flow of a program before it has been fully verified. An attacker may be able to inject code into an application that makes decisions about the control flow before the application has had a chance to fully verify itself. This may lead to information disclosure.
There are several mitigations against speculative execution. One mitigiation is the use of compiler features such as speculation barriers that prevent code from speculatively executing until it has been verified through a compiler. Another mitigiation is to use compiler features that allow programs to verify their control flow.
Intel microarchitecture issues
Intel has been found to have these potential issues as well. The issue is with the implementation of virtualization on Intel processors that may leave out functionality to properly synchronize the frequency of the processor with the frequency of the system memory. This may leave out protection against a race condition where two out-of-order execution paths may arrive at a memory location with different timings and may result in information disclosure. Unfortunately, there is currently no mitigation against this issue on Intel processors.
Another potential issue with Intel processors using out-of-order execution may be speculative execution. Speculative execution is a potential issue for many modern CPUs as it allows a CPU to make decisions about the control flow of a program before it has been fully verified. An attacker may be able to inject code into an application that makes decisions about the control flow before the application has had a chance to fully verify itself. This may lead to information disclosure.
There are several mitigations against speculative execution. One mitigiation is the use of compiler features such as speculation barriers that prevent code from speculatively executing until it has been verified through a compiler. Another mitigiation is to use compiler features that allow programs to verify their control flow. For example, you can use compiler hints (C++11) for loops and switch statements that tell your compiler where you expect them to branch next, so your processor always knows what instruction should execute when your program reaches each branch point.
Intel Microcode Updates
Intel is providing updates for the following products that include fixes for these issues:
Intel Core, Pentium and Celeron processors released prior to the first quarter of 2008
Intel Core and Pentium processors with Intel SpeedStep in all revisions released between the first quarter of 2008 and the fourth quarter of 2009
Intel Xeon processor 5400 series (Stepping 3)
Intel Xeon processor 5200 series
Intel Xeon processor E3-1200 family (Stepping 8)
Intel Core 2 Quad, Extreme Edition 965, 975, 990, QX9775 and QX9650 processors
AMD CPU Features and Speculation Control Flow
AMD processors have features that mitigate the risks of speculative execution, such as speculation barriers and copy-back instructions. However, these features are not available on all AMD CPUs.
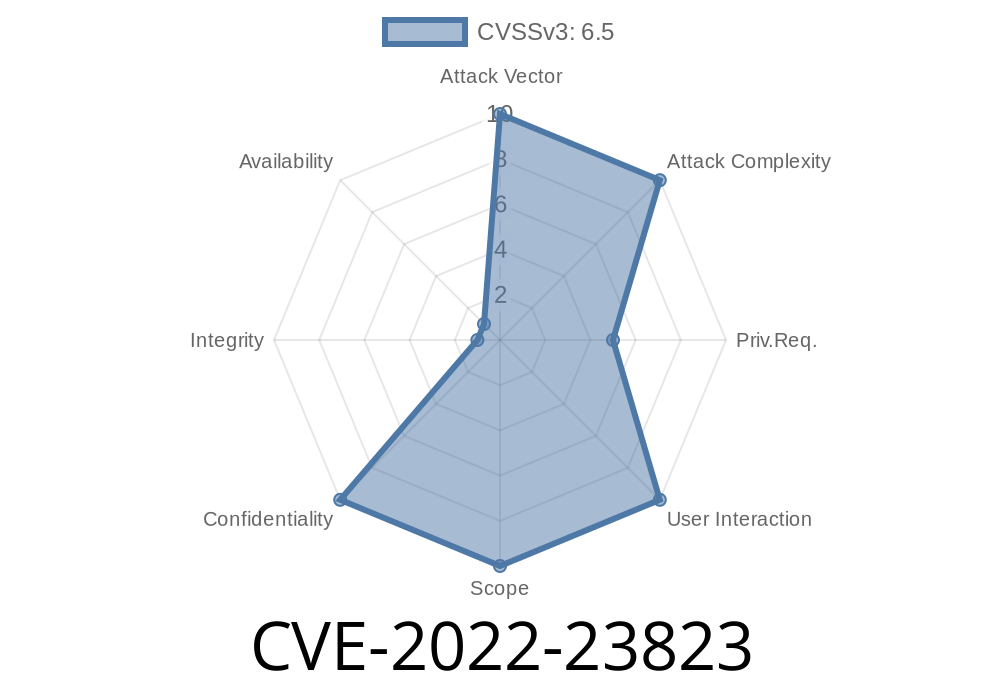
This issue is classified as a Moderate risk vulnerability because it may allow an attacker to gain information about the contents of memory by causing a race condition through speculation.
Essentially, there are two potential mitigations for this issue: using compiler features that prevent code from speculatively executing until it has been verified through a compiler, or using compiler features that allow programs to verify their control flow.
Intel® Processor Trace
Intel® Processor Trace provides detailed analysis of the CPU and memory usage. It can help you to identify potential issues and help you to understand your system’s behavior in real-time. Intel® Processor Trace includes a system-wide instrumentation framework that can be used to observe all or part of the system in real time, profiling live applications or capturing trace for later analysis.
If you would like more information about this issue, please contact your local Intel® office for further assistance.
Intel CPU Variants Affected By This Issue
Intel processors that implement out-of-order execution are impacted by the speculative execution vulnerability.
AMD processors that implement out-of-order execution may be impacted by this issue as well.
Intel processors that do not support out-of-order execution are not impacted by the speculative execution vulnerability.
There is currently no mitigation for AMD processors.
Timeline
Published on: 06/15/2022 20:15:00 UTC
Last modified on: 06/29/2022 17:42:00 UTC