The attackers could create a new agent for the company and insert malicious links in the description
B) Attacker can remotely access the device and perform malicious tasks
Fraudulent or malicious websites can be created by the attackers, which can in turn lead to the installation of malware on a computer. This malware would monitor employee activity and report stolen data back to the attacker.
Trusted HTTPS Certificate By Mistake
An example of a security risk that could occur when using an HTTPS certificate is if the company uses a trusted certificate for their website, but the attackers can create a new agent for the company and insert malicious links in the description. This would allow the attacker to redirect users to a fake website where they could steal login information or perform other nefarious activities.
An example of a security risk that could occur when using an HTTPS certificate is if the company uses an HTTPS certificate for their website, but the attackers can create a new agent for the company and insert malicious links into their description. This would allow them to redirect people to a fake website where they could steal login information or perform other nefarious activities.
Summary
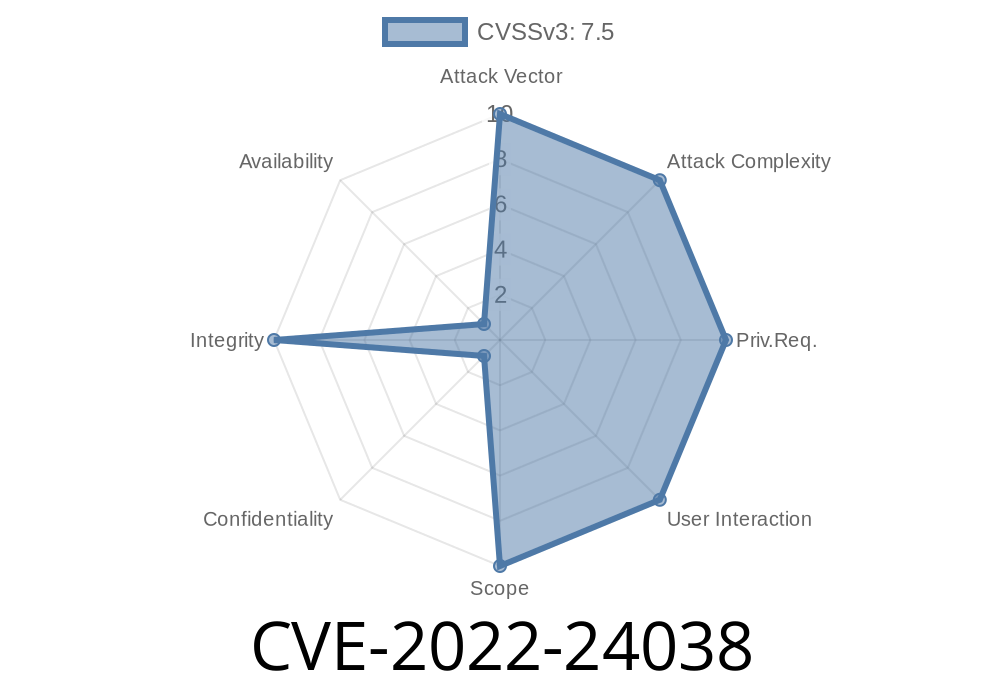
CVE-2022-24038 is a vulnerability in the web interface of the company's website. If an attacker creates a new agent for the company, they could insert malicious links into the description. This would allow attackers to redirect users to another site that looks legitimate, but actually contains malicious links.
Even if you don't see a vulnerability in the website of your business, it's important to check with your technical support team regularly to ensure that no vulnerabilities have been overlooked.
Why is this important?
The attackers could create a new agent for the company and insert malicious links in the description to infect the new agent with malware. To protect your company against this kind of attack, you should use a URL whitelist. This will help prevent the attacker from creating a new agent that could create malicious links in the description.
To protect your company against this kind of attack, you should use a URL whitelist.
Timeline
Published on: 11/18/2022 09:15:00 UTC
Last modified on: 11/22/2022 20:01:00 UTC