An attacker can send an email with a long message body to an unsuspecting victim. After the email is received, it can be pasted into a channel, where the attacker can send a request to the Slack import endpoint to import the email, potentially resulting in a crash of the Slack server.
Impeding Server Performance
In Mattermost version 6.7.1 and later, an authenticated user can track the amount of data processed by the server by creating a custom message filter to monitor the server-wide total data size.
This server-wide data size is not a metric for the amount of data processed by a single user. This server-wide data size does not provide a useful indication of server load or performance.
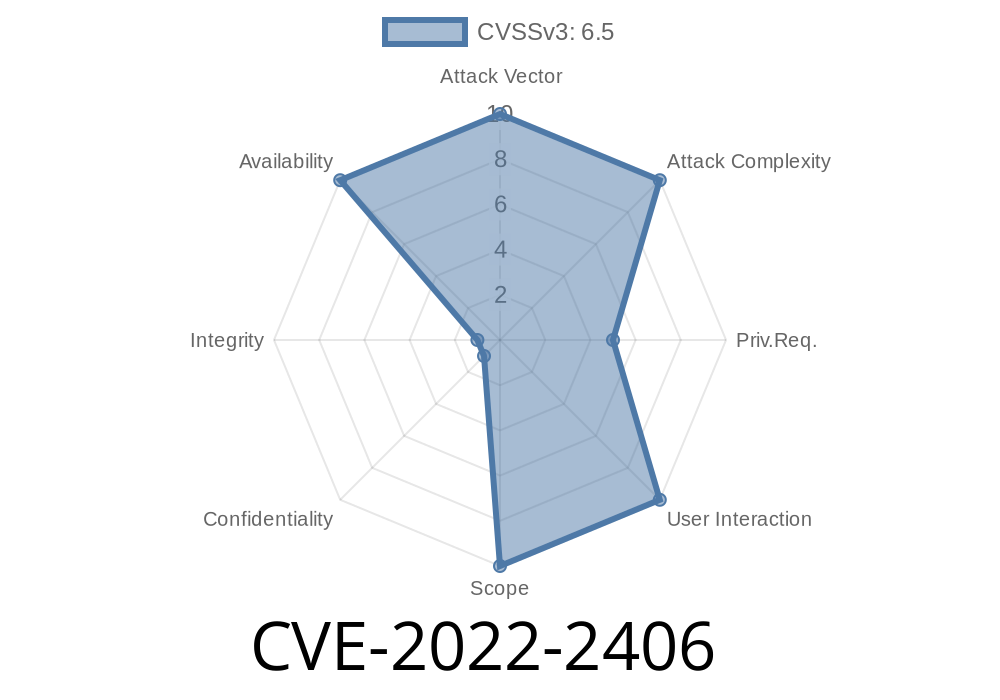
Vulnerability Summary
A vulnerability in the Slack import endpoint allows an attacker to overflow the buffer of a message body by sending a long message body to an unsuspecting victim. This can result in a crash of the Slack server.
How do I track server performance?
To monitor the server-wide total data size, follow these steps:
1. Navigate to "Settings"
2. Click on "Message Filters"
3. Scroll down and click on "Custom Message Filter"
4. Type the following string into the message filter input field:
system_info(processed_data)
How to track server performance
Mattermost does not provide any way for administrators to track this server-wide data size.
Instead, an administrator can create a custom message filter to monitor the server-wide total data size, which is available in version 6.7.1 and later of Mattermost. The administrator will also be able to view the average and maximum values for that metric as well as when it has changed.
Slack Impersonation Attack
An attacker could send an email with a long message body to an unsuspecting victim. After the email is received, it can be pasted into a channel, where the attacker can send a request to the Slack import endpoint to import the email, potentially resulting in a crash of the Slack server.
Timeline
Published on: 07/14/2022 18:15:00 UTC
Last modified on: 07/25/2022 18:08:00 UTC