From Microsoft’s Security Advisory: A security feature in Windows Vista, Windows 7, and Windows Server 2008 allows local privilege elevation only in response to a specific, predefined condition. This restriction helps to protect against Denial of Service attacks and other security threats. Unfortunately, this restriction also prevents certain legitimate operations from being performed, such as changing the system time or installing an update. This issue does not allow for the elevation of privilege when it is not required. If an attacker can trigger an operation that requires privileged access, but the privileged operation can be accomplished without elevated access, the attacker will be able to perform the operation without having to request an elevated access token. An example of this issue is a user running an application that requires the ability to install an application, but the ability to install an application depends on having a specific group of permissions, and those permissions cannot be granted without having to run under elevated privileges. An example of this issue is a user running an application that requires the ability to install an application, but the ability to install an application depends on having a specific group of permissions, and those permissions cannot be granted without having to run under elevated privileges. This issue is addressed in Windows by restricting the conditions under which local privilege elevation can be enabled.
Overview of Local Privilege Elevation in Windows Vista, 7 and 2008
Local privilege elevation allows a process to elevate its privileges in response to a specific, predefined condition. This feature helps to protect against Denial of Service attacks and other security threats. Unfortunately, this restriction also prevents certain legitimate operations from being performed, such as changing the system time or installing an update.
In Windows Vista, Windows 7, and Windows Server 2008 the following conditions will cause local privilege elevation:
-The user is running with LOCAL_PRIVILEGES=1 or LOCAL_MACHINE_SYSTEMTIME=1
-The user is running under Local System account
-The user is running in the context of a service that requires privilege elevation
-An application has been installed that requires privilege elevation
If any of these conditions are not met then the system will not allow local privilege elevation.
How to Become More Secure
An attacker can exploit this vulnerability by crafting a malicious application that, when run, would need to be elevated to local privilege. For example, an app could request the ability to install an update and then use that ability to elevate privileges in order to achieve malicious functionality. This issue is addressed in Windows by restricting the conditions under which local privilege elevation can be enabled.
Overview and Benefits
This security feature prevents certain legitimate operations, such as changing the system time, from being performed. However, it also prevents system-level attacks because privilege escalation can now only be achieved when required. The limitation in this feature is that it allows privilege escalation only in response to a specific, predefined condition. As an example of this issue, a user running an application that requires the ability to install an application but the ability to install an application depends on having a specific group of permissions cannot do so without privileged access.
What is Windows Privilege Elevation?
Windows privilege elevation is a security feature in Windows Vista, Windows 7, and Windows Server 2008 that allows only specific privileged operations to be performed. The restriction helps protect against Denial of Service attacks and other security threats. Unfortunately, however, this restriction also prevents certain legitimate operations from being performed, such as changing the system time or installing an update. This issue does not allow for the elevation of privilege when it is not required. If an attacker can trigger an operation that requires privileged access, but the privileged operation can be accomplished without elevated access, the attacker will be able to perform the operation without having to request an elevated access token. An example of this issue is a user running an application that requires the ability to install an application, but the ability to install an application depends on having a specific group of permissions, and those permissions cannot be granted without having to run under elevated privileges.
What is Local Privilege Elevation?
Local privilege elevation enables a user to run with the permissions of a higher-privileged account. The process includes requesting an access token from a privileged account, running under that token, and then returning the token back to a lesser-privileged account.
There are two methods for elevating privileges locally:
One is called "System rights" which requires a user to be logged in as an Administrator. Another method is "Local Security Token", which requires the user to apply for elevation and wait for their token to be approved.
Timeline
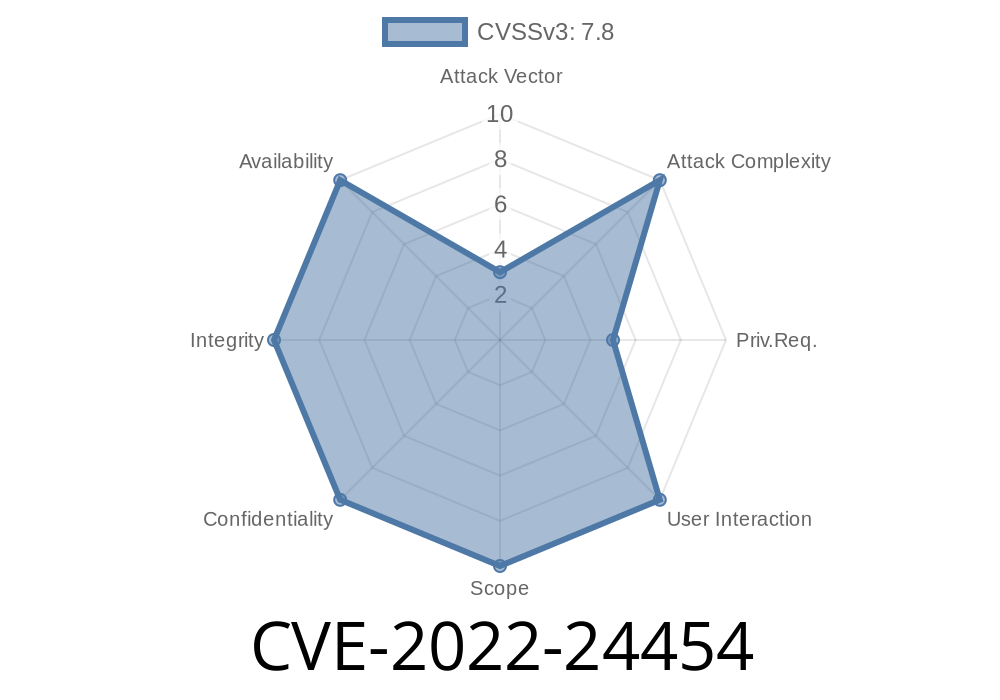
Published on: 03/09/2022 17:15:00 UTC
Last modified on: 05/23/2022 17:29:00 UTC