The available paths to remote attackers depend on the backup task used and the data source. Veeam recommends choosing paths that do not allow access to sensitive data. In addition to improper path selection, improper use of URIs in the backup task can also be a source of high-risk. For example, instead of using the following syntax to specify a backup repository: https://company>.veeam.net/backup/repo1/ URIs can also be used to access internal API functions. Therefore, if a user receives an email with an attachment that uses a URI like the following, she can be at risk of code execution: https://company>.veeam.net/backup/into/ filename> For example, a user receives an email with the following URI: https://company>.veeam.net/backup/into/filename> The user then clicks on the email, downloads the attachment, and opens it. An attacker can also abuse the use of URIs to access internal API functions. For example, the following URI can be used to access a function that allows an attacker to upload an executable code file: https://company>.veeam.net/backup/api/upload/filename>
Other possibilities
If the user chooses an improper path, the backup task can produce a large amount of high-risk data. For example, a high-risk data source could be copied to a public folder on the file share, which would make it easy for malicious users to find and retrieve this data.
In some cases, attackers may also use access to Veeam APIs or other resources to execute actions that are not related to backups, such as uploading or downloading files from a company server.
The following is an example of where an attacker might use an inappropriate URI: https://company>.veeam.net/backup/api/logging/filename>
The attacker then uses this information to log into the system and take control of it remotely.
Veeam Backup and Replication: High-risk factors
Veeam Backup and Replication users must be careful not to run into high-risk factors. The following are some of the risks associated with Veeam backup tasks:
1) Using improper paths in the backup task
2) Using URIs in place of path names, instead of using https://company>.veeam.net/backup/repo1/
3) Running a backup task over the internet
4) Running a backup task on a shared network connection
Veeam Backup Service Suite
Veeam Backup & Replication helps IT organizations create and deliver a virtual backup infrastructure that ensures data availability. The Veeam® Virtualization-as-a-Service (VaaS) platform delivers the full set of virtualization infrastructure services, including cloud management and orchestration, application migration, and data protection.
The Veeam Backup Service Suite enables organizations to securely back up their critical data at any scale across on-premises, in public clouds and on third-party clouds with ease. With the Veeam Backup Service Suite, companies can enjoy easy access to virtual machines hosted in private or public clouds with native backup services that enable rapid recovery and eliminate complex service management tasks.
Veeam Backup and Replication Tasks
Veeam Backup and Replication includes a number of tasks to perform backups. In addition, there are two types of backup for Veeam: full and incremental.
Full backups provide a complete copy of all data within the specified data source whereas incremental backups only contain the changes from one or more previous backups.
There are four tasks that can be used to back up the data source:
-Backup job task
-Schedule backup job task
-File-based backup task (Local File)
-File-based backup task (Network File)
The available paths to remote attackers depend on the backup task used and the data source. Veeam recommends choosing paths that do not allow access to sensitive data. In addition to improper path selection, improper use of URIs in the backup task can also be a source of high-risk. For example, instead of using the following syntax to specify a backup repository: https://company>.veeam.net/backup/repo1/ URIs can also be used to access internal API functions. Therefore, if a user receives an email with an attachment that uses a URI like the following, she can be at risk of code execution: https://company>.veeam.net/backup/into/ filename> For example, a user receives an email with the following URI: https://company>.veeam.net/backup/into/filename> The user then clicks on the email
Timeline
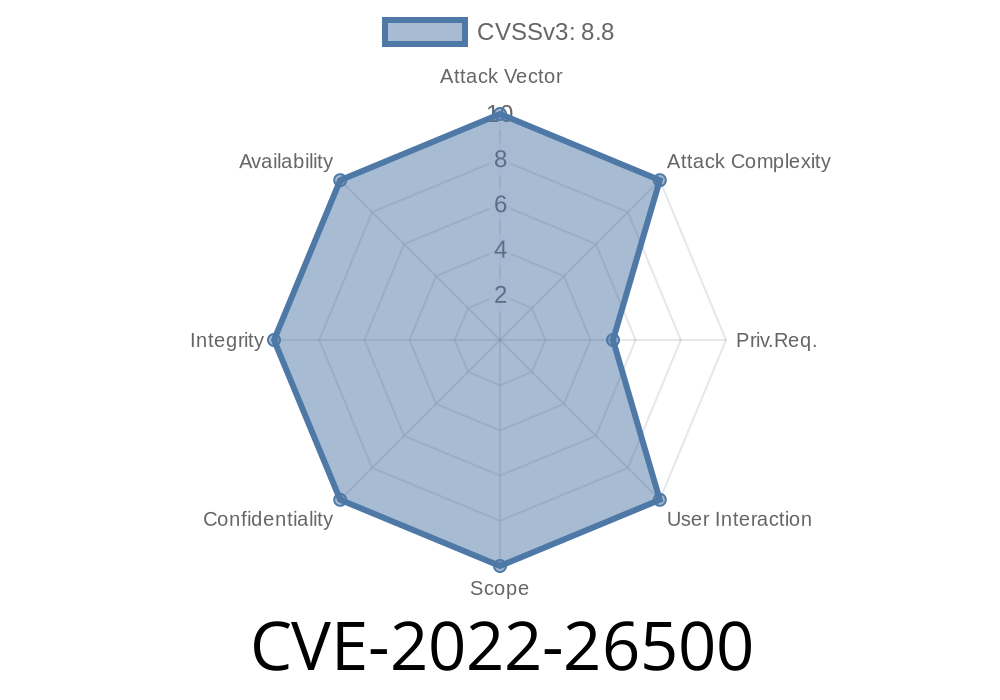
Published on: 03/17/2022 21:15:00 UTC
Last modified on: 03/24/2022 13:26:00 UTC