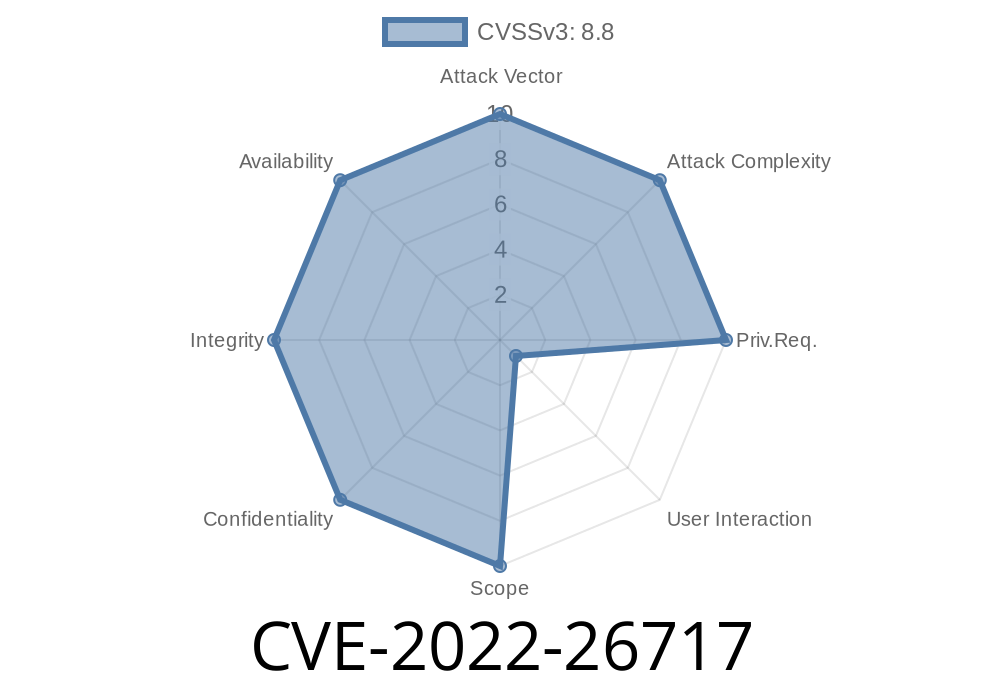
In 2022, security researchers uncovered CVE-2022-26717, a dangerous "use after free" vulnerability in Apple's WebKit, the browser engine that powers Safari and many other Apple apps. This bug, if exploited, could let attackers execute code on your device just by having you open a malicious website. In this article, we'll break down how the bug worked, see some sample code, describe exploitation, and explain how and when Apple fixed it.
What is a "Use After Free" Bug?
Software like WebKit manages memory by allocating and freeing blocks of memory as they are needed. A "use-after-free" bug happens when software tries to use memory after it’s already been freed. This can lead to unpredictable behavior, including allowing an attacker to execute arbitrary code (run any commands they want) on your device.
Imagine if you wrote something important on a chalkboard, then erased it (freed the memory), but your friend tried to read what was on it after it was erased—leading to confusion or mistakes. In programming, this confusion can lead to security issues.
Windows PCs with iTunes
How Did the Vulnerability Work?
WebKit processes web content using a complex set of rules. Sometimes, while processing JavaScript or HTML, it tries to reuse parts of memory that have already been released, if not managed carefully. Attackers can craft a webpage that carefully manipulates the order things are used and released in memory, getting the engine to "use after free"—using data that now points somewhere unintended.
Let’s see a simplified JavaScript example to illustrate a "use after free" pattern (not exact exploit code, since the real thing is very complex and hardware-dependent):
let victim = { a: 1 };
function triggerUAF() {
let arr = [victim];
delete arr[]; // Free reference to victim
// Force garbage collection (in reality, this step may be non-deterministic)
for (let i = ; i < 10000; i++) {
let tmp = {};
}
// Now, attempt to use victim after it's (possibly) freed
console.log(arr[].a); // Undefined behavior
}
triggerUAF();
This example is educational and will not actually exploit your browser, but it gives you an idea: If the browser is tricked into reusing freed memory, an attacker can sometimes hijack what gets loaded there.
The attacker builds a web page with JavaScript that carefully manipulates the browser's memory.
- Through "dangling pointers" (references to data that's already been freed), the script gets a use after free situation.
The script tricks the browser to jump to that code, allowing them to run code on your device.
This process is highly technical and requires a deep understanding of browser internals. Researchers and attackers usually fuzz (automatically test with lots of random inputs) the engine to find such vulnerabilities.
Proof-of-Concept (PoC) Details
While public PoCs are scarce due to the risk to users, the following pattern often describes real-world UAF exploits:
Escalating from memory confusion to code execution
Note: For safety, real-world exploit code is not shown here.
Apple Security Update Advisory:
https://support.apple.com/en-us/HT213258
CVE Details:
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-26717
WebKit Security Updates:
Apple Release Notes for iOS 15.5:
https://support.apple.com/en-us/HT212788
How Apple Fixed It
Apple addressed this bug by improving memory management in WebKit. Engineers updated the code to make sure that once memory is freed, there are no longer any dangling references to it. The patch landed in:
- iOS/iPadOS 15.5
iTunes 12.12.4 for Windows
The fix prevents reusing object references after they have been freed, protecting users from attackers who try to exploit this memory confusion.
What Should You Do?
Update your devices! If you’re running an older version of iOS, iPadOS, macOS, or Safari, go to settings and check for updates right away. Even if you only use third-party browsers on your Apple device, many of them use WebKit behind the scenes.
In Summary
CVE-2022-26717 was a dangerous "use after free" vulnerability in Apple’s WebKit engine that could allow hackers to take control of a device just by luring victims to a malicious website. Apple’s fix in May 2022 improved memory handling, closing the door on this powerful attack. As always, keep your devices up to date to benefit from critical security fixes!
Stay safe and keep your software updated. For security professionals, bugs like CVE-2022-26717 show just how tricky browser security can be—and how vital prompt patching is for all internet users.
Timeline
Published on: 11/01/2022 20:15:00 UTC
Last modified on: 11/03/2022 13:14:00 UTC