The security issue can be demonstrated by the following example: An attacker has access to a music service instance and sends an email with a malicious attachment to a customer. The customer opens the email, downloads the attached document and then opens the document in the customer’s email client. The customer does not notice the installation of a malicious document as the document is signed with a valid certificate. When the customer clicks on the document, the customer’s email client connects to the music service instance and executes the malicious code. The customer’s email client has no access to the customer’s email account and has no access to the customer’s social media account. The customer is at risk of being attacked.
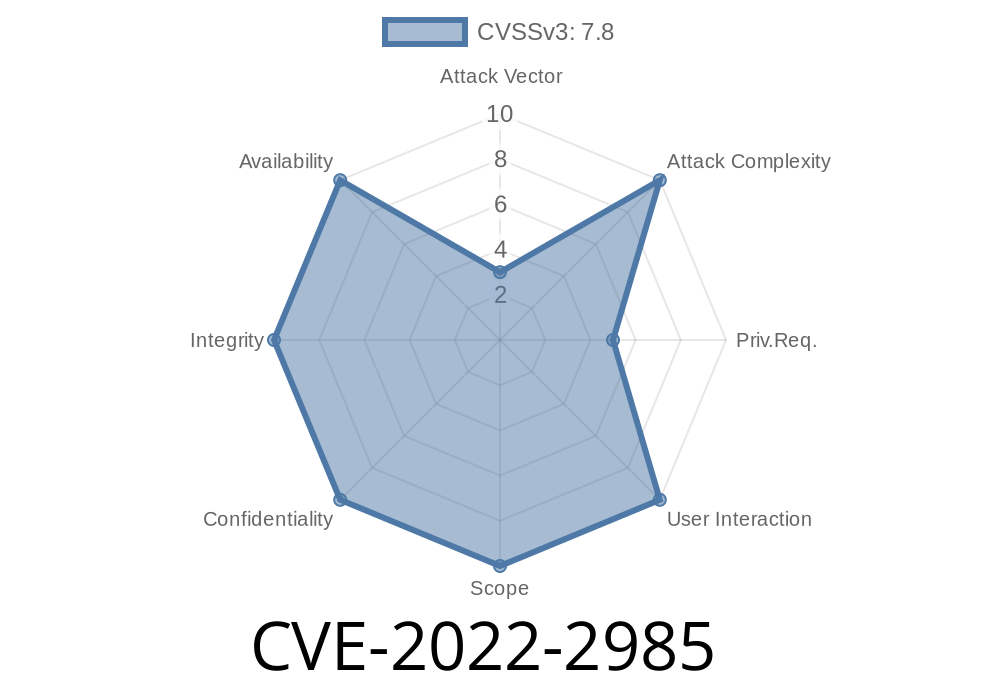
Vulnerability summary
The security issue described here is related to the TLS certificates. The vulnerability allows an attacker to create a malicious document that has a valid certificate, which means the victim will trust it as if it was signed by the service provider.
This vulnerability affects all major email clients, including Microsoft Outlook, Apple Mail and Mozilla Thunderbird.
Recommendations:
- Designers should implement signature validation.
- Designers should also be mindful of certificates that they use to sign their documents, as they may not be valid or trusted by the customer’s email client.
- Email clients will need to consider how to prevent malicious attachments from being uploaded.
- The customer's email account will need to have a two-factor authentication option implemented in order to prevent malicious attachments from being uploaded.
Mitigation for this issue
To mitigate this risk, the music service should be configured to use certificates that cannot be abused. Additionally, the music service should be configured to restrict file content from being able to download and execute. Lastly, the customer’s email client should not be permitted to connect to the music service instance.
Timeline
Published on: 10/14/2022 19:15:00 UTC
Last modified on: 10/18/2022 19:33:00 UTC