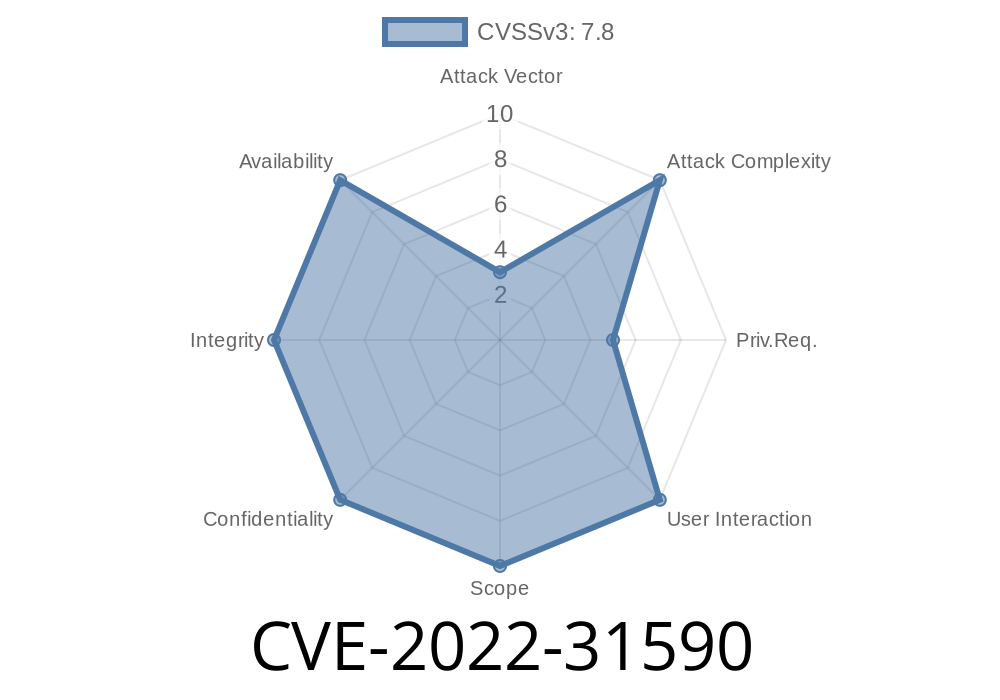
SAP PowerDesigner Proxy - version 16.7 has XSS via pathname in proxy settings via specially crafted URL. An attacker with low privileges and has local access, could trick a user into visiting a specially crafted URL, which could then inject arbitrary JavaScript code into the context of the front-end application. This JavaScript code could then be executed with elevated privileges of the application during application start up or reboot, potentially compromising Confidentiality, Integrity and Availability of the system. SAP PowerDesigner Proxy - version 16.7 has XSS via pathname in proxy settings via specially crafted URL. An attacker with low privileges and has local access, could trick a user into visiting a specially crafted URL, which could then inject arbitrary JavaScript code into the context of the front-end application. This JavaScript code could then be executed with elevated privileges of the application during application start up or reboot, potentially compromising Confidentiality, Integrity and Availability of the system. CVE-2018-16861 has been discovered in SAP PowerDesigner Proxy - version 16.7. This vulnerability is due to the lack of proper validation of user-supplied input
SAP PowerDesigner Proxy - version 16.7 Assignee Information
SAP PowerDesigner Proxy - version 16.7 has XSS via pathname in proxy settings via specially crafted URL. An attacker with low privileges and has local access, could trick a user into visiting a specially crafted URL, which could then inject arbitrary JavaScript code into the context of the front-end application. This JavaScript code could then be executed with elevated privileges of the application during application start up or reboot, potentially compromising Confidentiality, Integrity and Availability of the system.
Timeline
Published on: 06/14/2022 19:15:00 UTC
Last modified on: 06/24/2022 17:05:00 UTC