The issue is exploited when the server has many active connections, which can be achieved by running many threads or using the connection_limit setting. This can be exploited by connecting to the server using a long password. To mitigate the issue, you should limit the number of active connections. Also, setting connection_limit to a very low value will limit the number of connections and will mitigate the issue.
Accepting and processing connections from remote hosts to your server can be dangerous and can lead to a Denial of Service. Accepting connections from untrusted hosts can be dangerous for your server and for your clients. Connection
SSL/TLS Certificates
SSL/TLS certificates are a necessity for your website because they provide encryption to your web traffic. This prevents hackers and other online threats from intercepting your data while it's in transit. You must also make sure that SSL/TLS certificates are installed on any web servers that you have access to, such as VPS or cloud hosting. The main issue with this is that if you're the only one who has access to those servers, then you'll have to manage the SSL/TLS certificate yourself.
Establishing a Connection Limit
To mitigate the issue, you should set a connection limit. If your server has many active connections, it's easy to create an exploit by connecting to the server using a long password. This can be mitigated by setting the connection limit high enough that it is not possible to exploit with a long password.
How to setup NGINX with TLS and disable SSLv3 nginx uses TLS (Transport Layer Security) and SSLv3 by default. If you are using a Linux server, this configuration is as simple as adding the following line to your /etc/nginx/nginx.conf file:
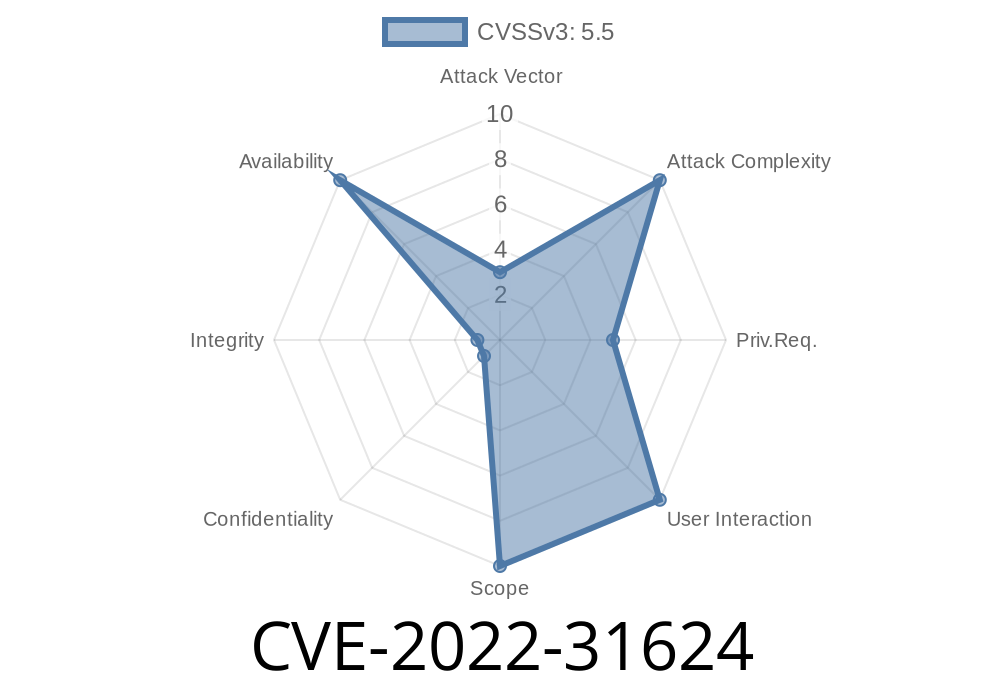
Denial of Service
Denial of Service (DoS) is a type of attack that consumes all available resources on a system or network and prevents legitimate users from using the service. For example, if there are many active connections to a server, it can be exploited by connecting to the server using a long password. This causes your server to become unresponsive, which can delay the response time for all clients.
To mitigate Denial of Service attacks, set connection_limit to a low value and configure other settings on your server accordingly.
Timeline
Published on: 05/25/2022 21:15:00 UTC
Last modified on: 07/07/2022 15:15:00 UTC