This can be leveraged to obtain administrator-level access, install malicious software, modify host system settings and so on.
This issue affects ESXi 5.0, 6.0, and 6.5, ESX v5.0, v5.1, v5.5, v6.0, v6.5, and v7.0. It does NOT affect ESXi 5.1, 6.0, or 6.5 nor ESX v5.0, v5.1, v5.5, v6.0, v6.5, or v7.0. For all supported versions, VMware recommends updating to the latest software as soon as possible.
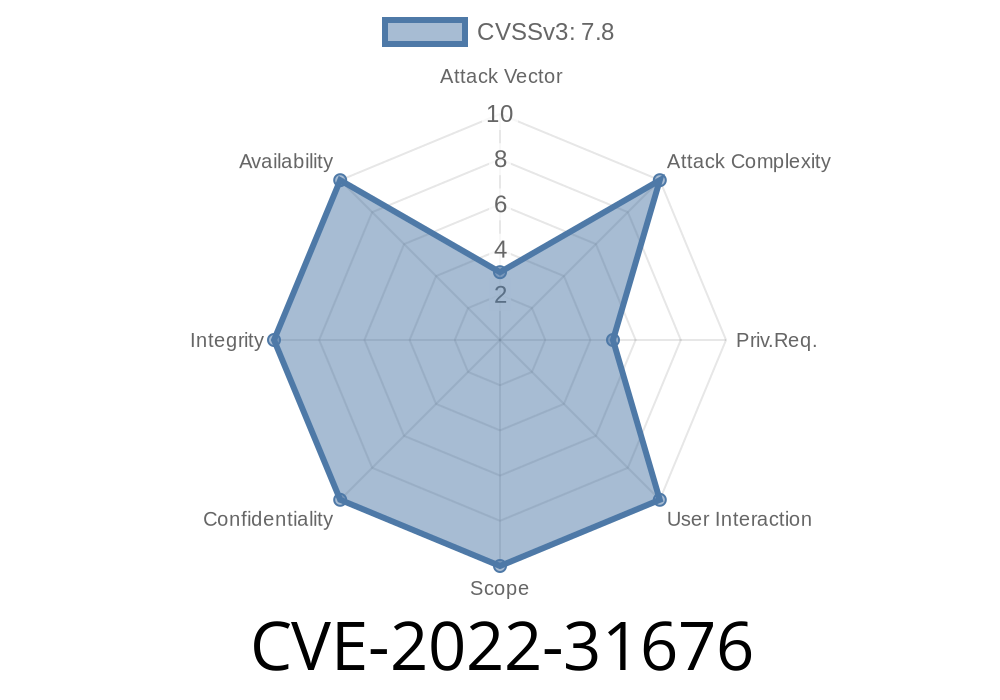
Vulnerability Details
CVE-2022-31676 is a local privilege escalation vulnerability in the ESXi host manager on the VMware ESXi 5.0, 6.0, and 6.5 platforms that can be leveraged to obtain administrator-level access, install malicious software, modify host system settings and so on.
This issue affects ESXi 5.0, 6.0, and 6.5, ESX v5.0, v5.1, v5.5, v6.0, v6.5, and v7.0. It does NOT affect ESXi 5.1, 6.0, or 6.5 nor ESX v5.0, v5.1, v5.5, v6.0, v6.5 or v7.0
VCP-Cloud Based Security Standard for ESXi and vCenter
VMware has released a vCenter Server virtual appliance which supplies vSphere with the security benefits of its own cloud-based platform, called VCP-Cloud.
The new standard for securing VMware's two products is designed to provide protection against the latest in cyber-attacks. As part of this new standard, VMware has introduced its own cloud-based solution for monitoring and managing the security of their software. This solution is known as vCenter Protect. It offers a suite of tools that monitor and manage software from a central location via an API or agent. It can also provide remote system re-imaging in case of compromise and enables organizations to create custom reporting dashboards that show threats, events, compliance violations, and other important information.
VMWare Recommendation: Stay up-to-date
VMware recommends that customers stay up-to-date with the latest patches for their respective products. Updating to the latest patch is an important step in maintaining security and stability. VMware provides a convenient update function in vSphere Client, but this method is not always reliable. The easiest way to stay up-to-date is by ensuring that you are running the latest version of your products.
VMWare Update Instructions:
1. Download and install VMware ESXi/ESX Update 10 or later.
2. Click here to download the update package from VMware.
3. Unzip the downloaded update package onto your host machine and run the installer file in the directory that you have unzipped it to, accept all default settings during installation (this will automatically upgrade your current version of ESXi/ESX).
Vulnerability Overview
A vulnerability affecting VMware products has been identified. Vulnerable software versions include ESXi 5.0, 6.0, and 6.5, ESX v5.0, v5.1, v5.5, v6.0, v6.5, and v7.0
The issue is caused by an invalid input validation in the NetFlow monitor which allows for remote code execution to occur on the host system without authentication or authorization (CVE-2022-31676).
Timeline
Published on: 08/23/2022 20:15:00 UTC
Last modified on: 08/29/2022 17:52:00 UTC