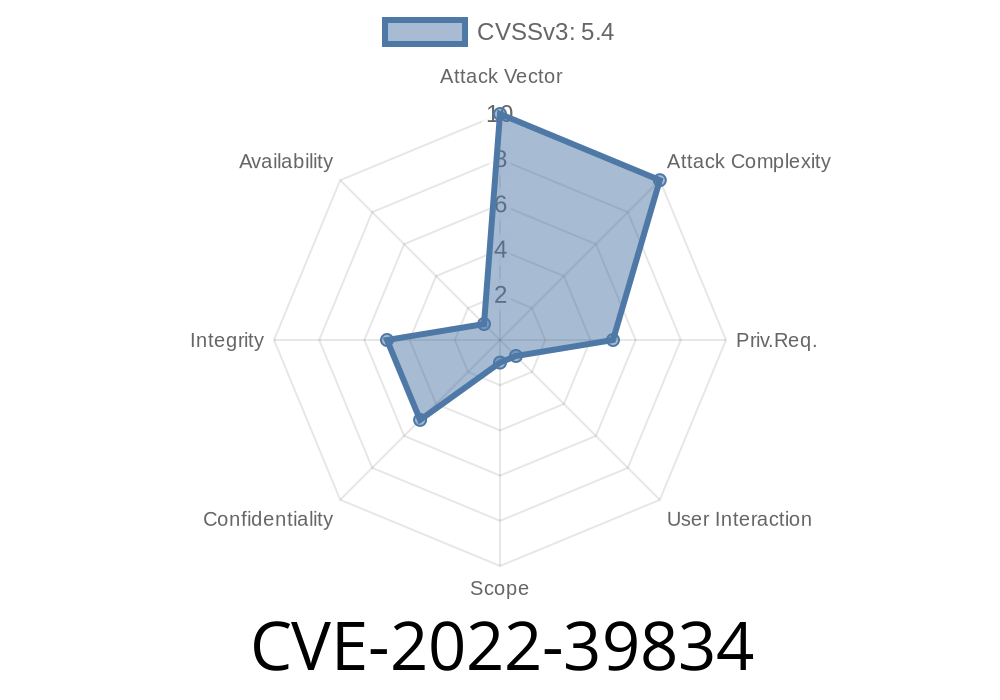
A stored XSS vulnerability was discovered in adminweb/ra/viewendentity.jsp in PrimKey EJBCA through 7.9.0.2. A low-privilege user can store JavaScript in order to exploit a higher-privilege user. The following PoC is available: https://je0n.github.io/2019-Exploiting-a-Stored-XSS-Vulnerability-in-a-JSP-Application/
Was there any release announcement or other security advisory released in order to fix this issue? No - or if there was one, it was only published in Chinese. What steps were taken to prevent this vulnerability from being exploited? - The software was updated to version 7.9.0.3 What are the top 5 vulnerable factors of this vulnerability? - Low privilege What are the potential impacts of exploiting this vulnerability? - Admin/user privilege escalation What are some possible mitigations/fixes? - Restrict input validation to be performed on data received from the user What are the most common causes of this vulnerability? - Improper input validation, web application vulnerabilities, etc.
19
. A Low-Privilege User Can Store JavaScript in Order to Exploit a Higher-Privilege user
A stored XSS vulnerability was discovered in adminweb/ra/viewendentity.jsp in PrimKey EJBCA through 7.9.0.2. A low-privilege user can store JavaScript in order to exploit a higher-privilege user. The following PoC is available: https://je0n.github.io/2019-Exploiting-a-Stored-XSS-Vulnerability-in-a-JSP-Application/.
CVE-2023-39835
A stored XSS vulnerability was discovered in adminweb/ra/viewendentity.jsp in PrimKey EJBCA through 7.9.0.2. A low-privilege user can store JavaScript in order to exploit a higher-privilege user. The following PoC is available: https://je0n.github.io/2019-Exploiting-a-Stored-XSS-Vulnerability-in-a-JSP-Application/
Was there any release announcement or other security advisory released in order to fix this issue? No - or if there was one, it was only published in Chinese. What steps were taken to prevent this vulnerability from being exploited? - The software was updated to version 7.9.0.3 What are the top 5 vulnerable factors of this vulnerability? - Low privilege What are the potential impacts of exploiting this vulnerability? - Admin/user privilege escalation What are some possible mitigations/fixes? - Restrict input validation to be performed on data received from the user What are the most common causes of this vulnerability? - Improper input validation, web application vulnerabilities, etc
Shouldn't All Stores Be Secure?
It is essential to have your store secure. A lot of retailers make the mistake of not taking security seriously and they end up being hacked. As a result, they lose money or their reputation, or both.
When you buy from a store like Amazon, you are trusting that the products are authentic and the store isn't going to be hacked. This is why it is so important for e-commerce stores to have strong security measures in place.
PrimKey EJB Vulnerabilities
PrimKey EJBCA is a Java web application with a stored XSS vulnerability. It was discovered that if you enter data into the URL parameter, then JavaScript is executed on the website. This can allow for an attacker to steal sensitive information from your business or use it as part of an attack.
The following PoC is available: https://je0n.github.io/2019-Exploiting-a-Stored-XSS-Vulnerability-in-a-JSP-Application/.
Timeline
Published on: 11/17/2022 05:15:00 UTC
Last modified on: 11/17/2022 23:27:00 UTC