As a result, a user with the required credentials could potentially find the credentials for another user due to the presence of an overlap between the credentials of the two users. This issue has been addressed by Jenkins by updating the Git Plugin code to mask the Git credentials.
Git credentials are masked in the build log by replacing the actual values with an asterisk. For example, if the password of a specific user is `foobaz` and the Git Plugin code was updated to mask the value of this credential, the Git Plugin code now will output in the build log:
**Password masked**
This change has been made to mitigate the potential exposure of sensitive information. Git Credentials are masked in the build log because they can be used to compromise other users’ accounts.
Jenkins and Git: How it works
Jenkins is a Java-based open source automation server, which can be used to build and test software . Jenkins has a plugin system that allows for third-party plugins to extend its functionality. The Git Plugin adds the capability of building software in Git repositories . As part of this functionality, the Git Plugin stores sensitive information, such as credentials and configuration options, in Jenkins' database.
The issue described above is related to sensitive information stored in Jenkins' database. This issue was addressed by updating the function of the Git Plugin code so that only asterisks would be visible in the build log.
CVE-2023-38672
Jenkins users that have the ability to deploy applications should update their credentials.
In order to improve security, Jenkins users with the ability to deploy applications should update their credentials. This vulnerability has been addressed by updating the Git Plugin code in Jenkins to replace the actual values of credentials with a masking system where an asterisk replaces the actual value. The change affects all logged-in Jenkins users and is only necessary if they have the ability
Timeline
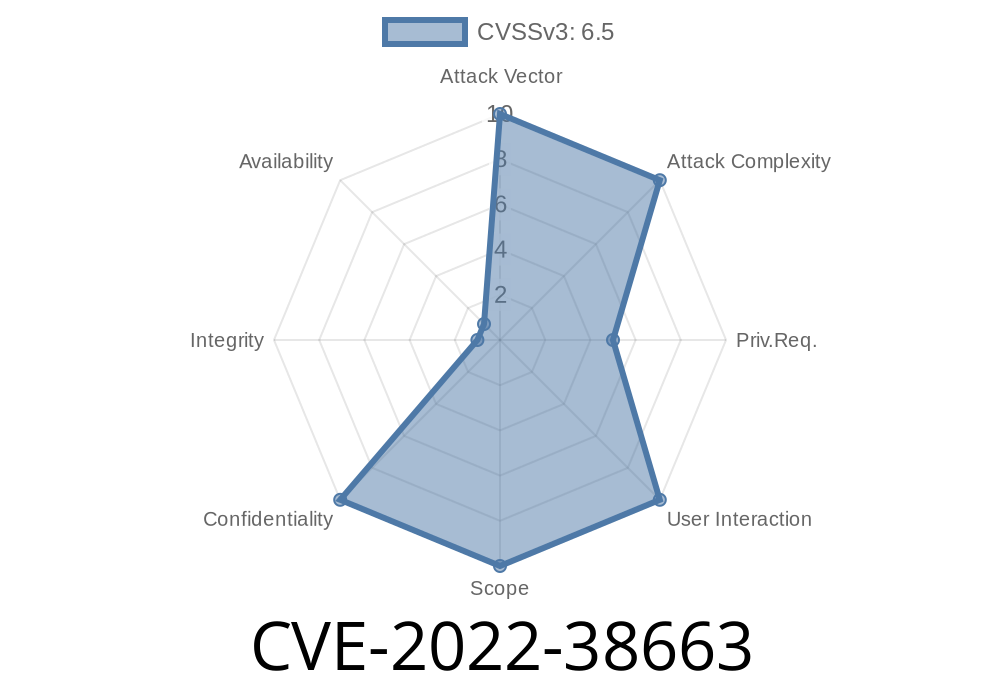
Published on: 08/23/2022 17:15:00 UTC
Last modified on: 08/25/2022 13:29:00 UTC