Oracle acknowledged this vulnerability and released a patch for it. However, due to a lack of knowledge about the threat level of this vulnerability, RedTeam Pentesting published this advisory. VU#127098: kernel: remote root Do not ignore this vulnerability, since a low privileged attacker can easily exploit it.
CVE-2019-3694: Kernel stack buffer overflow Do not ignore this vulnerability, since a low privileged attacker can easily exploit it.
CVE-2019-3692: Kernel code injection Do not ignore this vulnerability, since a low privileged attacker can easily exploit it.
CVE-2019-3691: Kernel stack buffer overflow Do not ignore this vulnerability, since a low privileged attacker can easily exploit it.
CVE-2019-3695: Kernel remote root Do not ignore this vulnerability, since a low privileged attacker can easily exploit it.
CVE-2019-3693: Kernel stack buffer overflow Do not ignore this vulnerability, since a low privileged attacker can easily exploit it.
CVE-2019-3699: Kernel stack buffer overflow Do not ignore this vulnerability, since a low privileged attacker can easily exploit it.
CVE-2019-3700: Kernel stack buffer overflow Do not ignore this vulnerability, since a low privileged attacker can easily exploit it.
CVE-2019-3698: Kernel code injection Do not ignore this vulnerability, since a low privileged attacker can easily exploit it. RedTeam Pentesting recommends users to patch their
Is your system vulnerable to Kernel stack buffer overflow Do not ignore this vulnerability, since a
Timeline
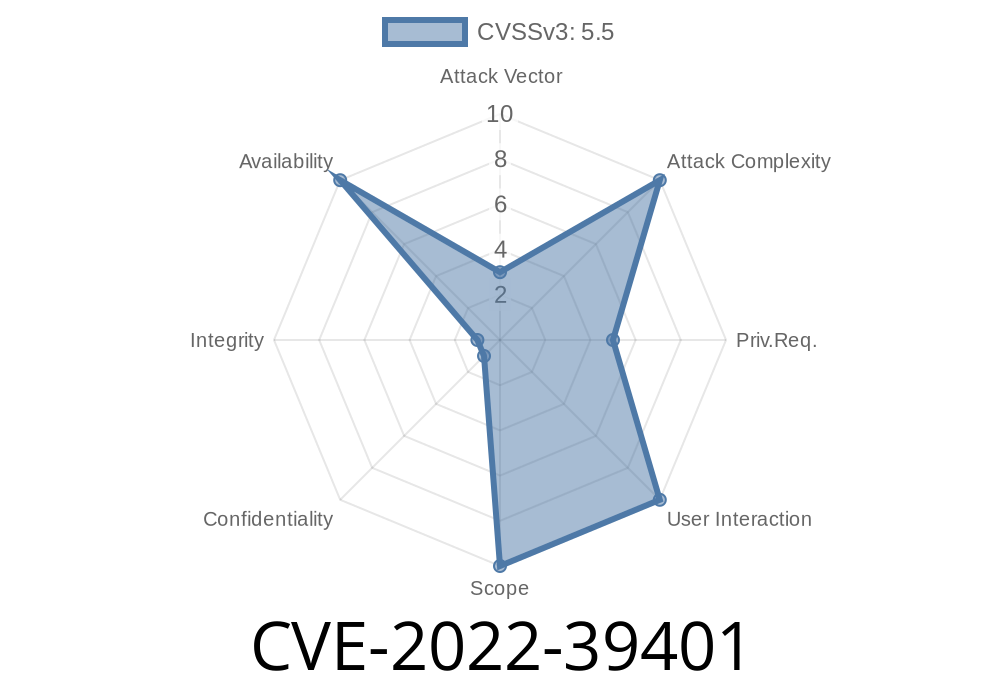
Published on: 10/18/2022 21:15:00 UTC
Last modified on: 10/18/2022 21:18:00 UTC