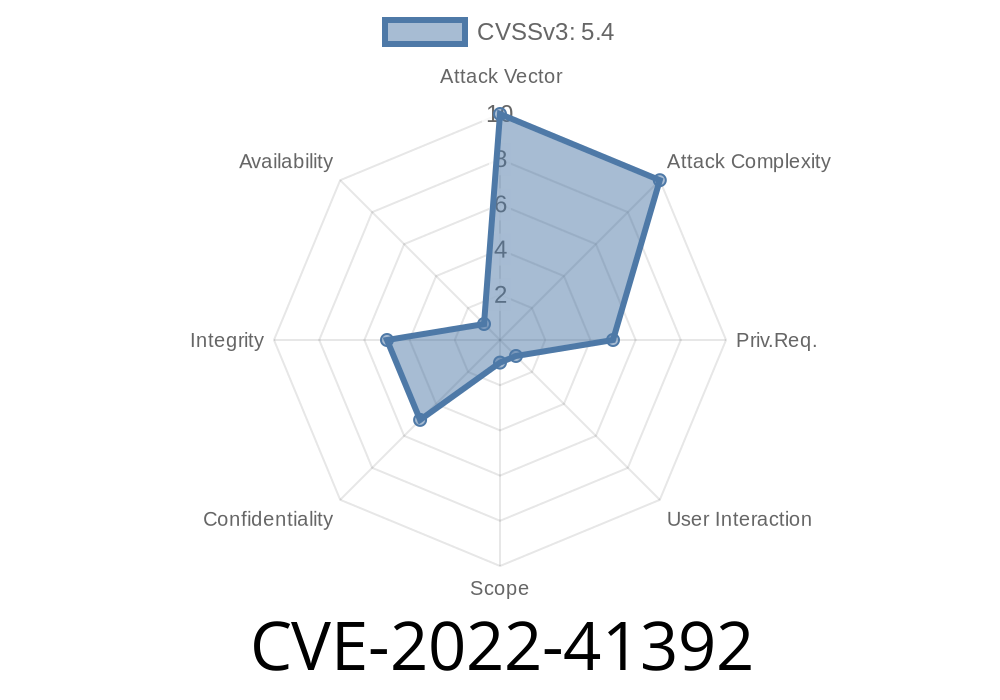
XSS vulnerabilities can be exploited by visitors without any authentication requirements. An attacker can inject script code or HTML into a web page and make requests using TotalJS to target systems that have this plugin installed. TotalJS does not have any filtering or sanitization mechanisms for such requests, allowing for injection of arbitrary scripts in the context of the site administrator's WordPress installation. This can lead to various attacks, such as data leakage, session hijacking, etc. Detection of XSS vulnerabilities requires an active monitoring process and action taken immediately in order to prevent any exposure of the website to malicious visitors.
The plugin version at the time of this writing is 3.6.9.1. The latest version is available here. If you are using an older version, it's recommended to update to a more recent version. REQUIREMENTS TotalJS plugin must be installed on the site to be protected.
WordPress version 4.9 or above.
Browsers that support HTML5.
Site Monitoring
The monitoring process for TotalJS is as follows:
TotalJS installation alerting must be enabled.
Monitoring must start immediately.
Monitoring must be done on a regular basis (at least monthly).
Action must be taken immediately in order to prevent any exposure of the website to malicious visitors.
Protecting against XSS attacks with plugin version 3.6.9.1
If you are using the plugin version that is available at the time of this writing (3.6.9.1), in order to protect your website from XSS attacks, you need to do the following:
- Ensure that your WordPress installation is at least 4.9 or above and has TotalJS plugin installed on it. If you're not sure if your WordPress installation has the plugin installed or not, you can run a quick check here: https://wordpress.org/plugins/totaljs/check/.
- Update your version of the TotalJS plugin to at least 3.6.9.1, which is available here: https://wordpress.org/plugins/totaljs/.
Timeline
Published on: 10/07/2022 19:15:00 UTC
Last modified on: 11/04/2022 19:21:00 UTC