This vulnerability does not affect most users, only those who create new accounts on the target site. This could be significant for a site with a high number of administrator accounts, such as a corporate intranet. Users with high level accounts such as “manager” or “admin” can grant themselves admin privileges by simply entering their login name. An attacker only needs to send a single link in an email or social media message to exploit this vulnerability. Regardless of the user’s level, it is recommended that administrators create a new, high-level account and disable “login name” as a login option.
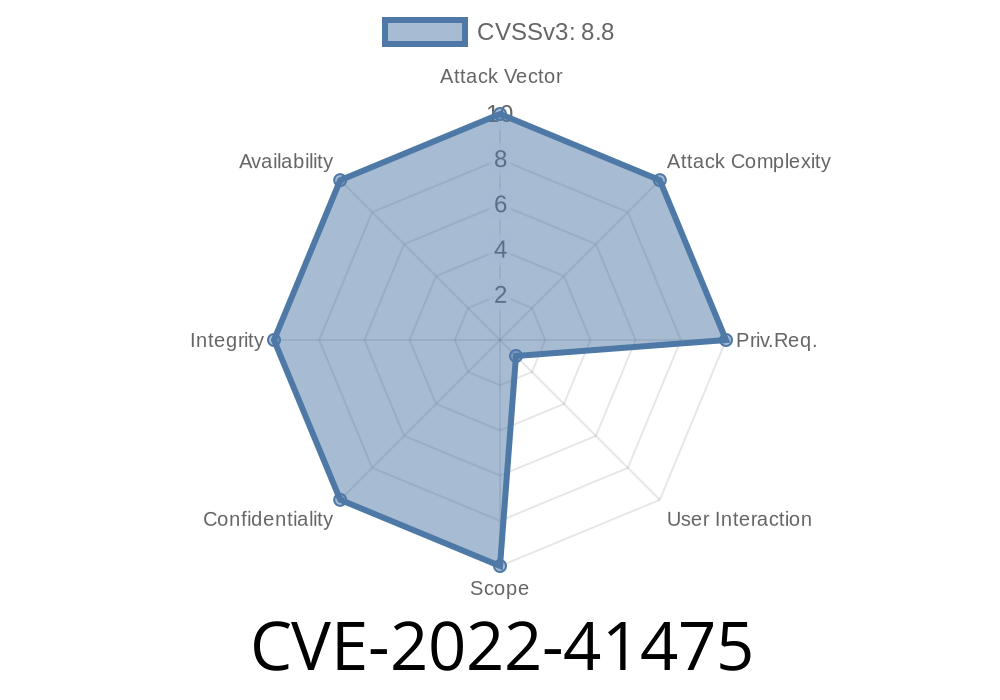
Summary of CVE-2022 -41475
This vulnerability allows an attacker to gain administrator access over a target site by sending a link in an email or social media message. The risk is not significant enough that it should be considered a major concern, but administrators should create a new, high-level account and disable “login name” as a login option.
IDS Detection and Mitigation
This vulnerability is not detected by most user-installed security software. If you use an antivirus product, it may be able to provide some mitigation, but the best defense against this vulnerability is creating a new account on the target site with a high level of privileges that an attacker cannot access.
The “Login Name” Vulnerability
This vulnerability allows a user to gain admin privileges on the target site. This is significant because it doesn’t require an attacker to have any special access. All that the attacker needs is a link in a message or email. What’s more, the attacker could be anyone, from a low-level account such as “user” up to and including administrator accounts.
CVE-2022-41546
This vulnerability is not related to the failure of two-factor authentication on Gmail. Instead, it is related to how Google handles the “invalid password” error message. The vulnerability exists in the way that user accounts are deleted when an invalid password is entered. Although this vulnerability does not function as a login bypass, it could still be used to recover accounts and gain elevated privileges.
An attacker only needs to send a single link in an email or social media message to exploit this vulnerability. Regardless of the user’s level, it is recommended that administrators create a new, high-level account and disable “login name” as a login option.
Vulnerability details and suggested fixes
The vulnerability allows users to bypass the login name field, which can be exploited by attackers. If a user creates a new account on the target site, they can grant themselves admin privileges by logging in with their email address and password. This is an easy exploit for a low-privileged user to perform, as it requires no special knowledge or skills. The vulnerability also allows users to create arbitrary administrator accounts in order to access sensitive information on the target site.
This vulnerability is not widely known and has not been publicly disclosed yet. It was discovered internally as part of our ongoing penetration testing efforts and reported through responsible disclosure channels.
Timeline
Published on: 10/13/2022 14:15:00 UTC
Last modified on: 10/14/2022 14:35:00 UTC