If a WordPress site is using the miniOrange plugin to generate one-time password codes, then there is a risk of a remote code entry attack. The attacker can eavesdrop the user's password when she logs into the plugin’s settings page and copy it. Then, the attacker can go to the plugin’s Google Authenticator page and enter the stolen password to log in. After logging in, the attacker can change the login password to any value and then log in again with the changed password to retrieve the access code.
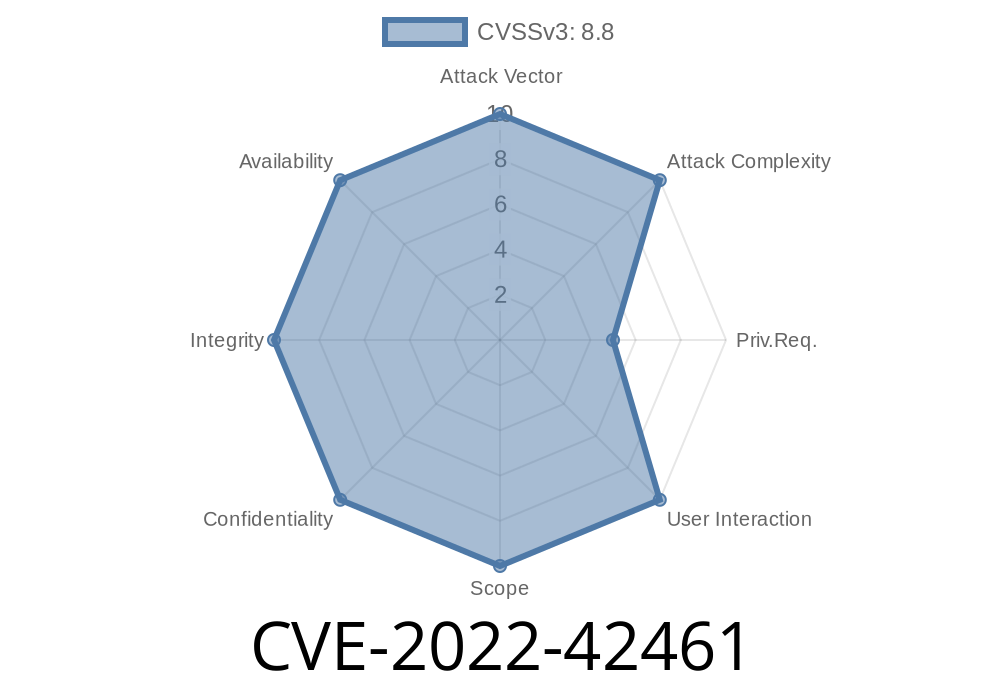
Google Authenticator is a two-factor authentication system that generates codes on the device and sends it to an app on the user’s mobile phone. The Google Authenticator app is usually installed on the user’s mobile phone. When the user wants to log into the website, she must enter the code generated on the mobile device app. Broken Access Control vulnerability in miniOrange's Google Authenticator plugin 5.6.1 or earlier.
To fix this issue, update the plugin to version 5.6.2 or later. If you cannot update the plugin, then disable access to the Google Authenticator plugin settings page from the WordPress backend.
Google Authenticator and broken access control vulnerability
The Google Authenticator plugin generates one-time password codes that are sent to the user’s mobile device. When the user logs into a website, she must enter this code to authenticate herself.
If you are using miniOrange’s WordPress plugin to generate one-time password codes and you are using Google Authenticator as your two-factor authentication system, then there is a risk of a remote code entry attack. The attacker can eavesdrop the user's password when she logs into the plugin’s settings page and copy it. Then, the attacker can go to the plugin’s Google Authenticator page and enter the stolen password to log in with the copied password. After logging in, the attacker can change the login password to any value and then log in again with that changed password to retrieve access codes from Google Authenticator.
To fix this issue, update your plugin version or disable access to the settings page from your WordPress backend in order to avoid this vulnerability.
Google Authenticator (FA)
This is a two-factor authentication system that generates codes on the device and sends it to an app on the user’s mobile phone. The Google Authenticator app is usually installed on the user’s mobile phone. When the user wants to log into a website, she must enter the code generated on the mobile device app.
Installing the plugin
Download the latest version of the plugin from the WordPress.org repository. Log in to the "Dashboard (Admin)" page of your WordPress site and navigate to Plugins > Add New. Search for "miniOrange" in the search tool and click on "Install Now". After installation, activate the plugin.
Timeline
Published on: 11/18/2022 20:15:00 UTC
Last modified on: 11/21/2022 17:05:00 UTC