XSS has been reported in the following plugins:
Concrete Email
Concrete Media
Concrete Polls
Concrete Tabs There has also been a case of XSS in the registration form of a Concrete CMS installation. The following proof-of-concept highlights this vulnerability. img> img> The above XSS is triggered when a user visits the “login” page, types their password and submits the form. This can be used as a vector for an attacker to execute arbitrary commands. This issue has been reported to Concrete and is under investigation. XSS has also been reported in the following plugins: XSS has been reported in the following plugins: There has also been a case of XSS in the registration form of a Concrete CMS installation. The following proof-of-concept highlights this vulnerability.
Concrete Email
Concrete Email is a popular email plugin. When the plugin gets installed, it creates a login page where users can input their credentials to log in to their website. There has been a report of XSS in the login form of this plugin and this vulnerability is under investigation.
Timeline
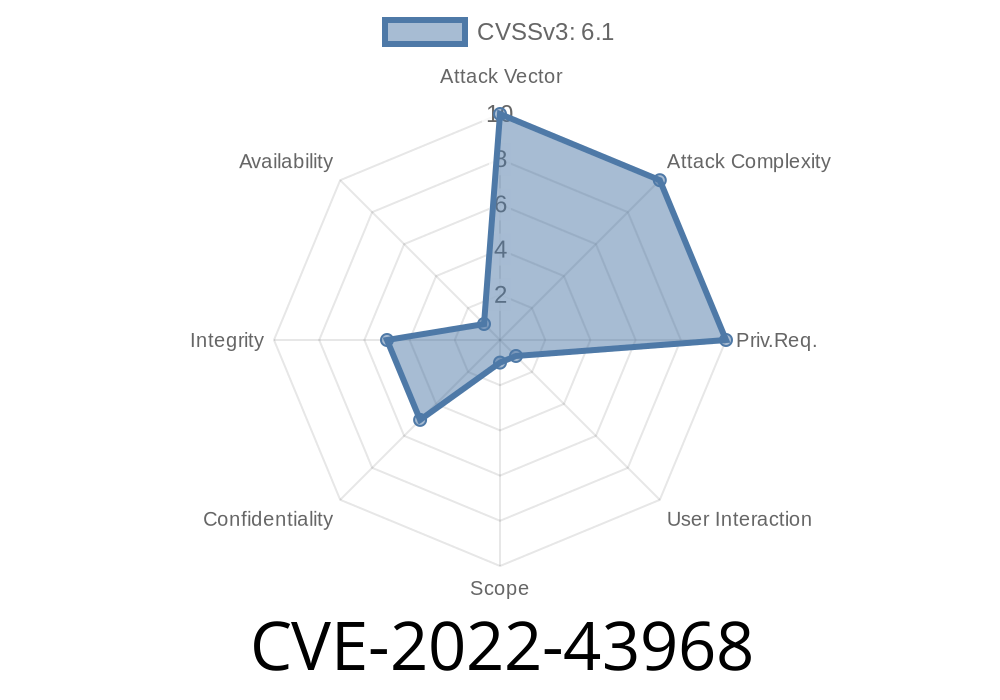
Published on: 11/14/2022 22:15:00 UTC
Last modified on: 11/17/2022 22:01:00 UTC
References
- https://github.com/concretecms/concretecms/releases/8.5.10
- https://documentation.concretecms.org/developers/introduction/version-history/913-release-notes
- https://documentation.concretecms.org/developers/introduction/version-history/8510-release-notes
- https://www.concretecms.org/about/project-news/security/concrete-cms-security-advisory-2022-10-31
- https://github.com/concretecms/concretecms/releases/9.1.3
- https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2022-43968