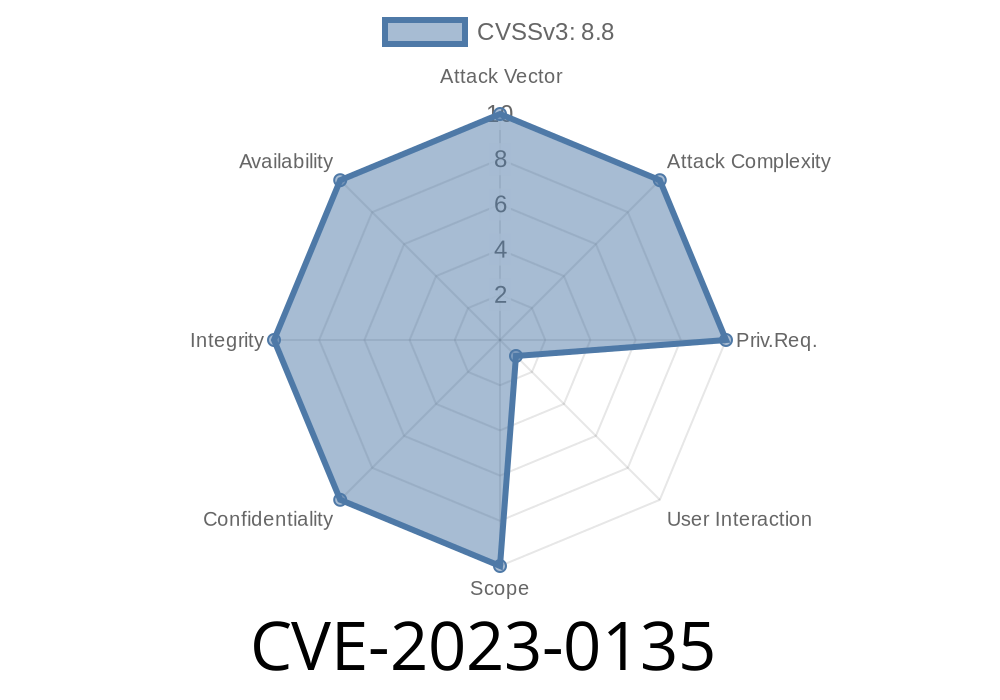
Early 2023 saw Google patching a notable security vulnerability: CVE-2023-0135, which impacts the “Cart” feature in Google Chrome before version 109..5414.74. This flaw, categorized as a use-after-free bug, could allow attackers to remotely corrupt the browser’s memory, potentially leading to code execution or data leaks.
This article gives you a hands-on breakdown of the vulnerability, a simple example of how it works, how an attacker could exploit it, and links to original references. All in simple, clear English.
What is CVE-2023-0135?
The bug revolves around how Chrome’s “Cart” system manages its memory. Specifically, it’s a *use-after-free* vulnerability. In simple terms, this happens when a part of the program frees up memory but then tries to use it again later. At that point, the memory may have been taken over or changed, which can be dangerous.
Severity: Medium (Chromium security rating)
Affected versions: Google Chrome before 109..5414.74
Attack vector: The attacker needs to convince a user to install a malicious Chrome extension. Once installed, the extension can interact with a crafted HTML page to trigger the vulnerability.
Technical Details: Where’s the Bug?
The core of the bug lies in how the Cart code manages database objects. If the memory assigned to a certain object (like a “cart” entry) is freed and then accessed again without proper checks, an attacker might manipulate that memory. This could result in:
Database corruption: Malicious data could overwrite or disrupt Chrome’s local cart data.
- Browser crash or arbitrary code execution: In some cases, a determined attacker could run code of their choice through careful crafting.
Here’s a simplified code snippet showing how a use-after-free might look in C++ (the language Chrome is built with):
CartEntry* entry = new CartEntry();
// ... some operations ...
delete entry; // Memory is freed here
// ...
entry->Update(); // Use-after-free: entry's memory may now be invalid!
In Chrome, this type of bug could be triggered if a malicious extension deleted a cart object while the rest of Chrome was still using it due to a crafted series of database and DOM operations.
Here’s a step-by-step game plan for a Chrome exploit based on CVE-2023-0135
1. Create a malicious extension. This extension can interact with Chrome’s “cart” feature and run custom JavaScript.
Convince a victim to install it. This could be through phishing, ads, or a drive-by download.
3. Serve a crafted HTML page. The page performs actions that trigger memory deallocation of a cart object (for example, by emptying the cart or tricking Chrome into deleting cart database entries).
4. Extension triggers race condition. The extension, through rapid operations or direct manipulation, causes Chrome to access the freed memory (use-after-free).
5. Heap is corrupted. The attacker can now overwrite key areas of memory, potentially leading to code execution, data leaks, or browser crashes.
Simple exploitation snippet (JavaScript, conceptual)
// Assume extension context:
chrome.extension.onMessage.addListener(function(message) {
if(message === "trigger") {
// Craft special cart operations
let cartDB = window.indexedDB.open("cart-db");
cartDB.onsuccess = function(e) {
let db = e.target.result;
db.transaction("carts", "readwrite").objectStore("carts").delete("target-cart");
// At this moment, if Chrome's cart code uses the now-deleted object, use-after-free happens
}
}
});
Note: This is a conceptual sample. Dangerous in real-world and should *not* be used for illegal activities.
Why Does It Matter?
- Attackers gain new power: Combined with social engineering, attackers could run code with user permissions.
Fixes and How to Stay Safe
Google fixed this bug in Chrome 109..5414.74. Updating Chrome is the simplest, best fix.
References and Further Reading
- Chromium Issue Tracker (#1398258)
- Google Chrome Release Notes (CVE-2023-0135 listed)
- NVD CVE Detail
- How use-after-free bugs work (Project Zero)
Summary
CVE-2023-0135 is a classic case of a use-after-free vulnerability with a modern twist: requiring a malicious extension and a crafted web page. Chrome quickly fixed it, but it’s a reminder of how even everyday browser features can become security landmines. Always stay patched, and be cautious with browser extensions!
If you found this breakdown useful or want more deep-dives into browser flaws, let me know in the comments!
Timeline
Published on: 01/10/2023 20:15:00 UTC
Last modified on: 01/13/2023 14:06:00 UTC