Apple takes user privacy very seriously, but no system is perfect. In early 2023, a new security issue was discovered that could let websites track sensitive user information. This vulnerability, known as CVE-2023-27954, allowed websites to collect origin information in unintended ways, making it easier for trackers to spy on users across the internet. In this long-read, we’ll explain what happened, why it mattered, look at a code example, see how Apple fixed it, and point you to references for more details.
What Is CVE-2023-27954?
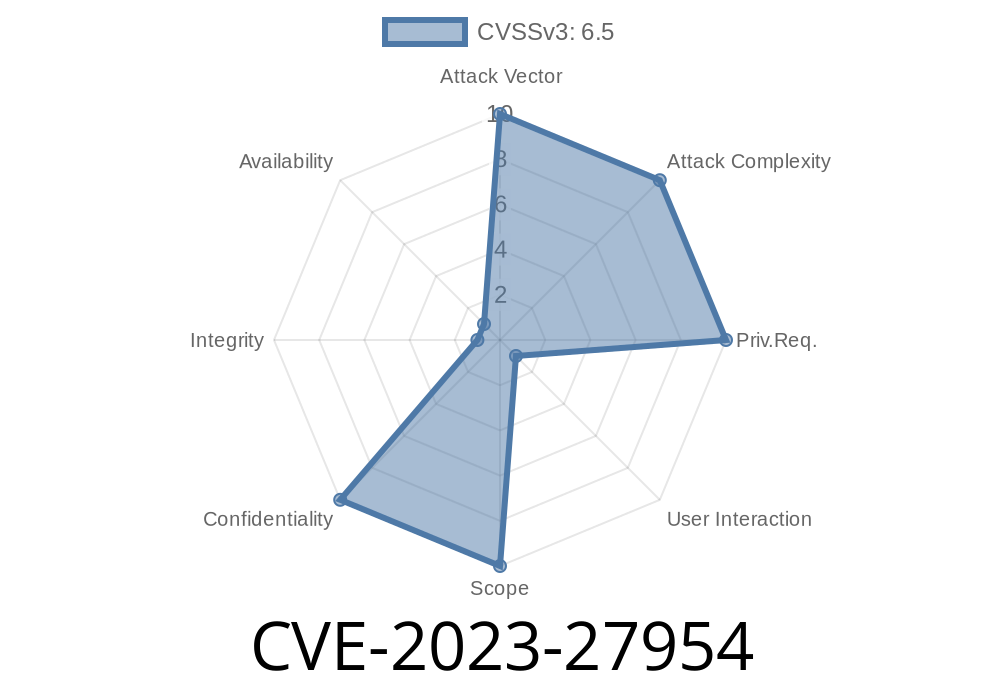
CVE-2023-27954 is a security vulnerability found in Apple’s WebKit rendering engine (which powers Safari and web views on Apple devices). It was possible, under certain circumstances, for a website to obtain information about the origin (i.e., where a request is coming from), allowing them to *track sensitive user information without the user’s knowledge or consent.*
iOS and iPadOS 16.4
If your device is running an older version, you might still be at risk.
How Did This Vulnerability Work?
To understand the root of the issue, let’s look at how websites usually identify where a request comes from. Normally, browsers include an Origin header that says something like:
Origin: https://example.com
WebKit, Safari’s engine, sometimes exposed more origin details than necessary when loading certain resources (like images or scripts). This information could leak cross-site, meaning a malicious website could learn more about your browsing habits and sensitive data.
Imagine you’re logged in to a private website, and then you visit a malicious site. That site could make a request to the private website and use the leaked Origin information to infer that *you* were browsing there. This is a simple form of cross-site tracking.
Let’s see a simplified JavaScript example of how a malicious website might exploit this
// Attacker's site code
fetch('https://target-victim.com/private-data';, {
method: 'GET',
credentials: 'include'
}).then(response => {
// Examine response headers or content
console.log(response.headers.get('origin'));
response.text().then(text => {
// Try to infer sensitive info from the response
if (text.includes('user-logged-in')) {
alert("User is logged in to target-victim.com!");
}
});
});
In vulnerable versions of WebKit/Safari, the attacker’s page could get unintended origin info about the request, which it should not have. This defeats privacy boundaries set by browsers.
Apple’s Solution: Remove Origin Information
To fix CVE-2023-27954, Apple removed the origin information from these cross-site requests when it could pose a privacy risk. By doing this, even if a malicious site tries the above trick, they won’t learn anything new—they’ll just see empty or generic origin values.
If you want to see Apple’s official notes
- Apple Security Update: macOS Ventura 13.3
- Apple Security Update: iOS 16.4 and iPadOS 16.4
- WebKit Releases and Changelog
iOS 16.4 and iPadOS 16.4
If you’re using an older Safari or OS version:
Immediately update your devices to one of these secure versions. Newer versions are safer by default.
Why Does This Matter For You?
Modern web tracking is sneaky, and attackers are always looking for new tricks. Something as simple as leaking origin information can let advertisers or malicious hackers build a profile of your online activity. Even if you think “I have nothing to hide,” you deserve privacy.
Key takeaway: Always keep your devices and apps updated, especially those that browse the web.
References & Further Reading
- Apple Security Updates List
- WebKit Bug Tracker
- CVE-2023-27954 on NIST
Conclusion
CVE-2023-27954 is a classic example of web privacy on the edge: what looks like a small leak can have big implications. Thanks to fast action by Apple and WebKit teams, this hole is closed for all users who update.
Stay safe out there—and always update your Apple devices!
Timeline
Published on: 05/08/2023 20:15:00 UTC
Last modified on: 05/12/2023 18:55:00 UTC