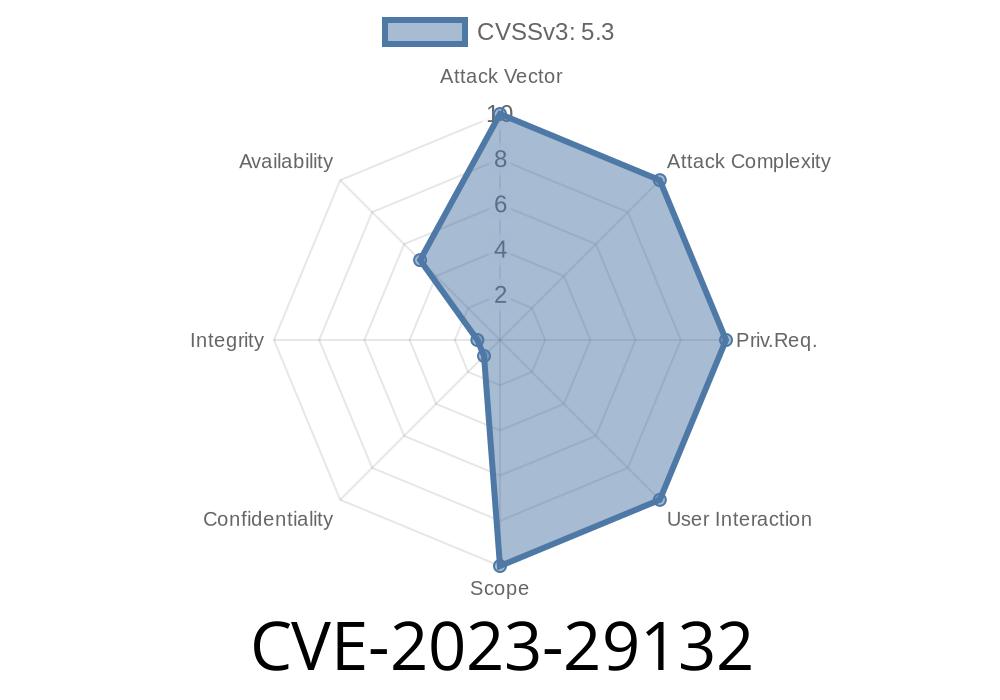
In May 2023, a severe vulnerability was disclosed in Irssi, one of the most popular terminal-based IRC clients for Unix systems. Assigned CVE-2023-29132, this bug allows for a “use-after-free” memory error, paving the way for accidental crashes and, under certain circumstances, even potential remote code execution. In this post, we’ll break down what this bug is, how it works, and how attackers might use it, all in simple and clear language. We'll also share links to the original references and give code snippets illustrating the flaw.
What is Irssi?
Irssi is a widely used Internet Relay Chat (IRC) client, known for its scriptability and extension support. Millions rely on it for real-time communication from UNIX terminals.
Technical Summary
In Irssi versions 1.3.x and 1.4.x before 1.4.4, a use-after-free bug exists in the way Irssi prints lines. The problem is triggered when printing a non-formatted line happens concurrently with printing a formatted line. Internally, Irssi uses “special collectors” to manage output lines, and a stale (already-freed) collector reference can get reused, causing unpredictable, unsafe behavior.
Layman’s Terms
Think of “use-after-free” like using a phone number after someone else has taken the number over. You think you’re calling your friend, but you might accidentally call a stranger. In this case, Irssi tries to use memory that it already gave up, so an attacker with precise timing and knowledge can potentially make Irssi use their data instead.
Crashes: The most common outcome is a client crash—annoying but not necessarily lethal.
- Remote Code Execution: With enough control, a crafty attacker could potentially run their code on your machine, especially if you’re running untrusted scripts or plugins.
The Vulnerable Code (Illustrative Snippet)
Here’s a simplified pseudo-C code snippet based on the logic described in Irssi’s patch announcement:
void print_lines(Collector *collector, line, formatted) {
if (formatted) {
/* Formatting printing uses the collector */
use_special_collector(collector);
} else {
/* Unformatted line printing */
use_normal_collector(collector);
}
/* Later, the collector may be freed ... */
free(collector);
/* ...but another print operation might try to use collector again! */
use_special_collector(collector); // Use-after-free happens here
}
What Actually Happened?
When a print operation for a formatted line and for a non-formatted line occurred at the same time (multi-threaded or from scripts), the special collector could be freed by one and immediately misused by another.
Manual Trigger
You can trigger this scenario by causing lots of formatted and non-formatted lines to be printed at once.
For instance, scripts or plugins that log or format messages could set up this race. With careful message sending (possibly even via another IRC-user), you could tip the timing to cause the bug.
PoC (Proof of Concept) — Simulated
Although a concrete remote exploit is hard due to unpredictable memory allocation, here is a pseudo-PoC (for research and learning only!):
# Simulate flooding formatted and unformatted prints via Irssi scripting
Irssi::signal_add("print text", sub {
print_formatted("This is formatted");
print_unformatted("This is not formatted");
});
# If done repeatedly and at high speed, you *might* trip the use-after-free.
You’d monitor Irssi for crashes or abnormal behavior (segmentation fault).
Real-World Exploitability
- Attackers can flood a channel with messages designed to trigger both “formatted” and “unformatted” outputs.
- Especially dangerous for users who run third-party Irssi scripts that manipulate outputs, or on shared multi-user systems.
- The most likely outcome is a crash, but with advanced heap spray and “memory grooming,” it could pivot to code execution in some edge cases.
How to Protect Yourself
Upgrade immediately to Irssi 1.4.4 or later. Vulnerable versions:
1.4. to 1.4.3
Get latest Irssi here: irssi.org/download
References:
- Official advisory: Irssi security advisory 2023/05/20
- CVE details: cve.mitre.org - CVE-2023-29132
- Patch code: GitHub PR #1479
Final Thoughts
CVE-2023-29132 is a real example of how subtle concurrency bugs can turn ordinary code into software with serious vulnerabilities. If you use Irssi (especially via scripts), update now and share this knowledge with your friends. Stay safe!
If you want more technical detail or have questions on memory issues like use-after-frees, leave a comment below!
Timeline
Published on: 04/14/2023 01:15:00 UTC
Last modified on: 04/24/2023 13:24:00 UTC