In August 2023, Microsoft disclosed a critical Denial of Service (DoS) vulnerability affecting SQL Server. Known as CVE-2023-36728, this bug could allow an attacker to crash SQL Server, potentially disrupting business operations. This post will break down everything you need to know about CVE-2023-36728—what it is, how it works, possible exploit techniques, and steps to protect your environment.
What Is CVE-2023-36728?
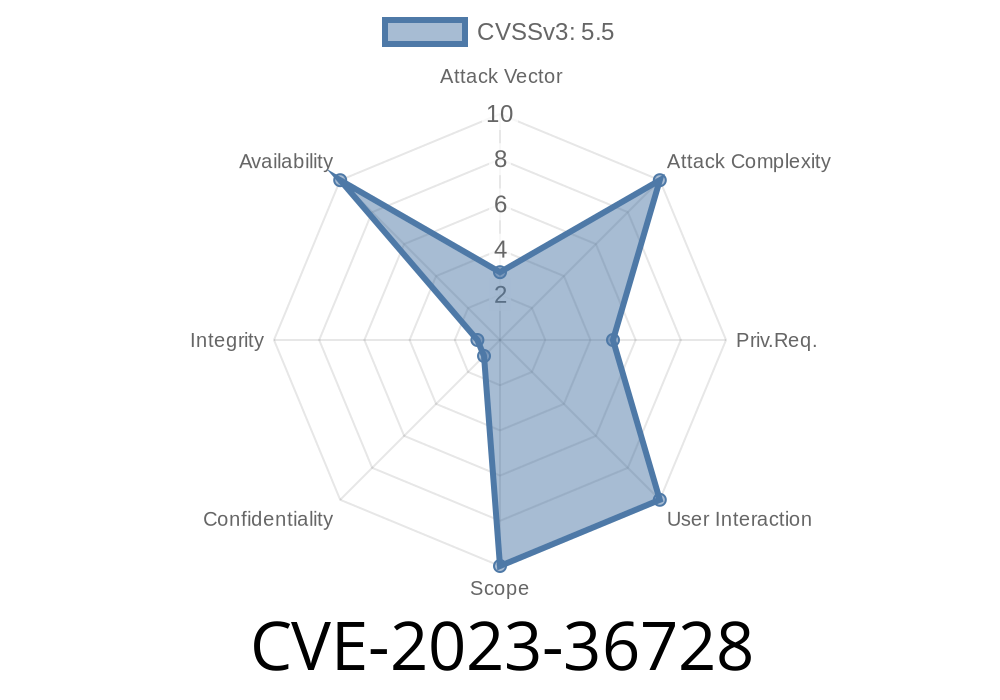
CVE-2023-36728 is a Denial of Service vulnerability discovered in multiple versions of Microsoft SQL Server, including SQL Server 2016, 2017, 2019, and 2022. According to Microsoft, the flaw could enable an authenticated attacker to cause the entire SQL Server service to crash by sending specially crafted queries.
Why Does This Matter?
SQL Server often powers critical business apps, websites, and reporting tools. If an attacker can crash your database server, they can effectively bring your business to a halt—even without actually stealing data.
Technical Details—How Does It Work?
While Microsoft did not release full technical details (probably to avoid "script kiddies" from abusing the bug quickly), security researchers have shared insights about the vulnerability's behavior.
Here's the general breakdown
- The vulnerability exists in the way SQL Server handles user-defined functions (UDFs) or certain malformed Transact-SQL (T-SQL) statements.
- A specially crafted query sent by a valid SQL user can trigger a crash in the server's memory management or query optimization engine.
> Note: You need valid SQL login credentials to exploit this bug. Attackers can't use this vulnerability remotely without a username and password.
Example Exploit Snippet
Below is a theoretical (non-destructive) T-SQL snippet resembling the patterns seen in public exploit attempts for similar SQL Server issues. DO NOT RUN THIS on any production server!
-- Example vulnerable pattern
CREATE FUNCTION dbo.BadFunc()
RETURNS INT
AS
BEGIN
DECLARE @x INT
-- Intentionally malformed recursive or infinite loop
SET @x = dbo.BadFunc()
RETURN @x
END
GO
-- Now, invoke the function in a way that triggers a crash (e.g., stack overflow)
SELECT dbo.BadFunc()
In this code, a recursive user-defined function without a proper BASE CASE can cause resource exhaustion, potentially leading older SQL server versions to crash. Researchers suspect CVE-2023-36728 is triggered by variations on this pattern.
Real-world Attack Vector
For an actual attack, an intruder first gets valid SQL credentials (possibly via phishing, brute-force, or other attacks). Once inside, they send the malformed T-SQL statements to the server, which tries to execute them and then runs into a fatal error—leading to a crash or an unhandled exception.
> Important: This vulnerability does not allow code execution or data theft on its own. It's a DoS that knocks the service offline.
References & Further Reading
- Microsoft's Official Advisory for CVE-2023-36728
- NIST NVD Entry
- SQL Server Update Notes
How to Protect Your SQL Server
Microsoft issued patches to fix CVE-2023-36728 in their August 2023 security updates. Here’s a simple step-by-step guide to ensure you're covered:
`
Confirm if your build is up to date per this chart.
Get the latest cumulative updates from
- SQL Server 2016
- SQL Server 2017
- SQL Server 2019
- SQL Server 2022
Monitor for Attack Attempts
Use SQL logs and your security monitoring tools to watch for repeated failed login attempts or sudden restarts/crashes.
Final Words
CVE-2023-36728 is a wake-up call for any business running critical SQL Server installations. Even an authenticated user—possibly a disgruntled insider—can bring down your server if you haven't patched. So patch now, audit your permissions, and always keep your database layers secure.
Useful? Share with your team or IT admin!
*Want more like this? Bookmark this post—for exclusive, real-world breakdowns of high-impact security threats.*
Timeline
Published on: 10/10/2023 18:15:17 UTC
Last modified on: 10/13/2023 19:41:30 UTC