---
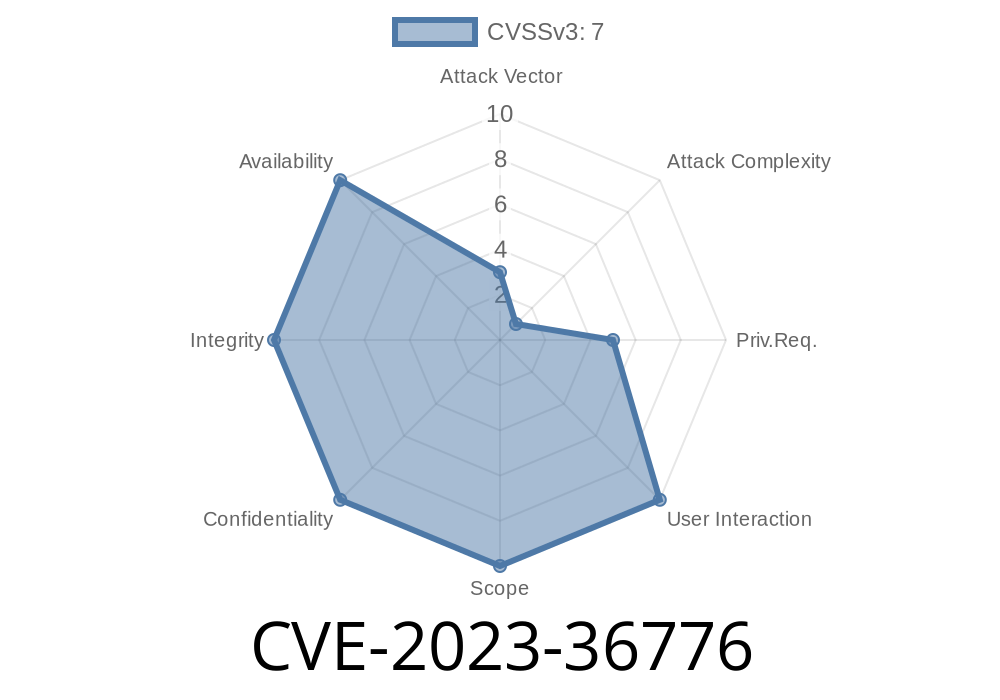
Microsoft patched an important security issue, CVE-2023-36776, in September 2023. Targeting Windows’ Win32k driver, this vulnerability allowed attackers to gain higher-level privileges (think: system-level control) using crafted code after already gaining access as a basic user.
Let’s look at what happened, why it matters, and how attackers exploited this flaw, in simple terms.
What is Win32k?
Win32k.sys is a major part of Windows—the heart of the user interface. It handles things like drawing windows, managing buttons, and overall GUI stuff. Because it works so deep in the system (kernel mode), any bugs here are dangerous.
Vector: Local (i.e., you already arrived on the machine as a user).
Microsoft’s Security Update Guide for CVE-2023-36776
In Simple Words
- If an attacker already has any kind of account on your PC, they could run a program that triggers a bug in Win32k.
The Technical Angle
The flaw centers on improper handling of window objects. Win32k lets user-mode code call functions that shouldn’t mess with kernel memory—but, due to a check failure, bad actors can trick it into writing or reading where it shouldn’t.
Imagine: There’s a locked door between normal programs and the computer’s control room. Win32k accidentally left the window open.
Here’s a very simplified pseudo-code that gives the flavor (real exploits are more complex)
// This is NOT a real exploit—just an illustration!
HWND hWnd = CreateWindowEx(WS_EX_LAYERED, "BUTTON", "Click Me", ...);
// Malicious message triggers the bug
SendMessage(hWnd, SOME_SPECIAL_MESSAGE, param1, param2);
// Now, if the bug worked, the exploit process has SYSTEM privileges.
*Note: Real attacks involve more tricks, like heap spraying, and often use undocumented API calls (like NtUserCreateWindowEx). Real exploit code is publicly available, but we won’t link to illegal or dangerous resources here.*
Exploit in the Wild
Russian-speaking cybercrime forums quickly discussed this bug. Payloads started appearing less than a month after patch release. Some attackers bundled a proof-of-concept in malware droppers to bypass Windows Defender.
One known public proof-of-concept:
- github.com/Ch01n/CVE-2023-36776 (for educational purposes only)
If you want to see how quickly threat actors move, check out security researcher Will Dormann’s Tweet tracking this CVE in attacks.
Windows Server 2016, 2019, 2022
If you didn’t patch after September 2023, you are at risk.
Least privilege: Users should have only minimum permissions necessary.
- EPP/EDR solutions: Updated security tools can catch known proof-of-concept attacks.
Get Microsoft’s official patch info:
September 2023 Security Updates
Conclusion
CVE-2023-36776 is a classic reminder that local privilege escalation vulnerabilities can open the door for attackers already inside. Win32k bugs are especially dangerous because they can be chained with other exploits for full system takeover.
If you manage Windows machines:
Watch for odd behavior—new users, sudden privilege elevation, and so on.
Stay informed—these vulnerabilities are leveraged by real attackers very quickly.
*References:*
- Microsoft Advisory
- NIST National Vulnerability Database
- GitHub Educational PoC
- TrendMicro Write-Up (when available)
Timeline
Published on: 10/10/2023 18:15:17 UTC
Last modified on: 10/12/2023 22:22:20 UTC