---
Security vulnerabilities in Windows don't just affect individual machines—they can risk entire networks or businesses. The CVE-2023-38159 highlights how the Windows Graphics Component, a part of the system that manages displaying visuals, can be exploited for elevation of privilege (EoP). In this exclusive, simple-language deep dive, we’ll break down this vulnerability, see how a bad actor might exploit it, check out sample code, and point you to official sources.
What Is CVE-2023-38159?
CVE-2023-38159 is a vulnerability in the Windows Graphics Component. When exploited, an attacker already with local access can gain higher privileges—possibly even SYSTEM rights on the target machine. That means malware or an attacker could move from a regular user to full administrative control.
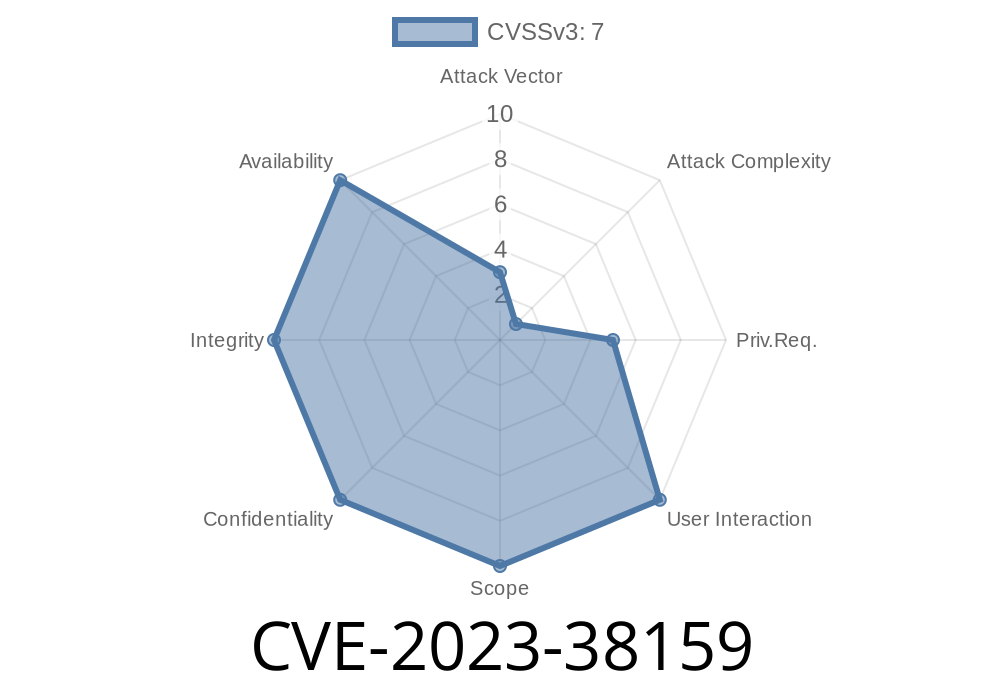
Severity: Important
CVSS Score: 7.8 (High)
Patched: Yes, in Microsoft’s August 2023 Update
Technical Breakdown
Simply put, the vulnerability exists because the Windows Graphics Component doesn't handle memory properly. Normally, programs must manage how they read from and write to memory; sloppy handling can lead to “memory corruption.”
Here, if an attacker creates a special request to the graphics system (using, for example, a malicious app or code snippet), they can trigger Windows to run arbitrary code at higher privilege.
Exploit Details: How Would This Work?
Let’s say Alice’s Windows computer is up and running. If Eve (the attacker) can run some code as Alice (maybe via a phishing email or a malicious installer), she can exploit this flaw to *jump* to admin rights—even if Alice’s account is “standard.”
The following is a conceptual code snippet (not a ready exploit, but demonstrates the issue)
// This is NOT a working exploit, only a demonstration!
#include <Windows.h>
#include <wingdi.h>
#include <stdio.h>
int main() {
HDC hdc = GetDC(NULL);
// This might not trigger the vulnerability directly,
// but in the real exploit, a specially crafted bitmap
// could corrupt memory in the Graphics component.
BITMAPINFO bmi;
ZeroMemory(&bmi, sizeof(bmi));
bmi.bmiHeader.biSize = sizeof(BITMAPINFOHEADER);
bmi.bmiHeader.biWidth = 1;
bmi.bmiHeader.biHeight = 1;
bmi.bmiHeader.biPlanes = 1;
bmi.bmiHeader.biBitCount = 32;
bmi.bmiHeader.biCompression = BI_RGB;
// This part would be fuzzed or crafted by the attacker
void* pvBits = NULL;
HBITMAP hBitmap = CreateDIBSection(hdc, &bmi, DIB_RGB_COLORS, &pvBits, NULL, );
if (hBitmap) {
printf("Bitmap created.\n");
} else {
printf("Failed to create bitmap.\n");
}
// The attacker would now attempt to trigger the vulnerability by
// passing malformed data here, aiming for memory corruption.
ReleaseDC(NULL, hdc);
return ;
}
Disclaimer: This code does NOT exploit the vulnerability as-is. Exploit developers often use “fuzzing” tools to find the exact inputs needed.
Proof of Concept (PoC) and Availability
As of now, there’s no public exploit PoC released, but similar flaws in the Graphics component typically become popular among malware authors after patches are released and reverse engineered.
All supported versions of Windows before the August 2023 patches.
- Especially dangerous in shared computers, enterprise devices, or where attackers can run untrusted code.
How Can You Fix It?
Patch Your Systems.
Microsoft’s update in August 2023 fixes this problem. Update via Windows Update or enterprise patching tools.
Official References
- Microsoft Security Guide for CVE-2023-38159
- NIST National Vulnerability Database Entry
Final Thoughts
CVE-2023-38159 is a classic case of a low-level bug with high-impact consequences. Because local privilege escalation vulnerabilities often become “catch-all” tools for malware, anyone who manages Windows machines should ensure they’re patched.
Remember:
Stay updated. Run only trusted software. Watch for future security advisories.
If you want to nerd out more, check out the Microsoft and NIST links above. Stay secure!
Timeline
Published on: 10/10/2023 18:15:17 UTC
Last modified on: 10/12/2023 22:19:27 UTC