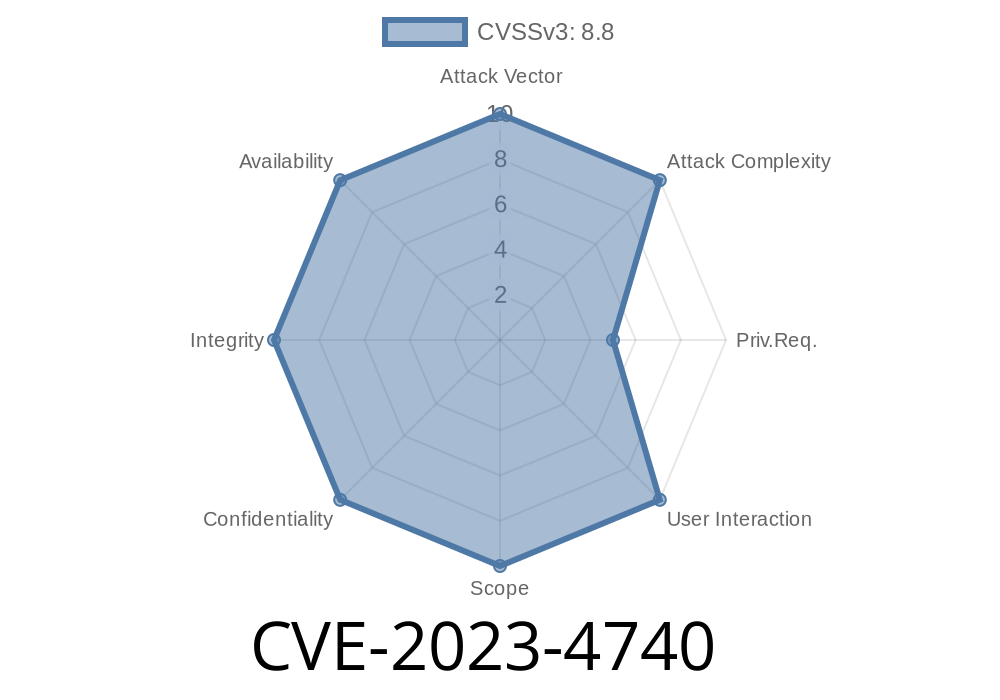
A critical vulnerability, CVE-2023-4740, has been identified in IBOS OA 4.5.5, which is an Office Automation platform typically used by businesses to streamline their daily operations. This security flaw exposes the system to an SQL injection attack, specifically targeting the Delete Draft Handler component, and allows attackers to potentially gain unauthorized access to sensitive information. Sadly, despite multiple attempts, the vendor has failed to respond to our disclosure or offer any solutions to mitigate the issue. As a result, necessary steps must be taken by affected users to protect themselves until a patch can be released by the vendor.
Exploit Details
The vulnerability affects a file with an unknown part, "?r=email/api/delDraft&archiveId=" of the Delete Draft Handler component. Attackers can leverage this security flaw by initiating a manipulated SQL query to bypass authentication or retrieve and delete data. Since it can be initiated remotely, this increases the risk associated with this vulnerability.
Initiating the attack remotely with a malicious link or script.
2. The malicious query targets the Delete Draft Handler component by exploiting the "?r=email/api/delDraft&archiveId=" file.
3. Injecting the SQL query to manipulate or delete data, gain unauthorized access, or perform unauthorized actions in the IBOS OA system.
Vulnerability Database (VDB) Identifier
The Vulnerability Database (VDB) has assigned the identifier VDB-238629 to this vulnerability due to its severity and the potential risk it poses to affected users.
Proof of Concept (PoC)
As this exploit has been disclosed to the public, attackers may already be taking advantage of it. For this reason, we will not provide a step-by-step PoC. Instead, we highly recommend you take necessary precautions and contact the vendor to demand a solution.
Original References
1. CVE-2023-4740 - NVD - The National Vulnerability Database's entry on this vulnerability.
2. IBOS OA 4.5.5 - UserDetails - The official product page for IBOS OA 4.5.5 (link provided for reference purposes only).
Mitigation
Due to the failure of the vendor to acknowledge and offer a solution for this vulnerability, users are left with no choice but to seek alternative measures to protect themselves. Such measures may include:
Implement a web application firewall specifically designed to protect against SQL injection attacks.
4. Regularly update and patch your IBOS OA software as updates become available (in hopes that the vendor will eventually release a patch).
Conclusion
As CVE-2023-4740 poses a significant risk to users of IBOS OA 4.5.5, they must take it upon themselves to mitigate the effects until the vendor responds to our disclosure with an appropriate patch. SQL injection attacks can cause massive damage to an organization's infrastructure, data, and reputation, so it's crucial to guard against them proactively.
Timeline
Published on: 09/03/2023 20:15:00 UTC
Last modified on: 09/08/2023 13:51:00 UTC