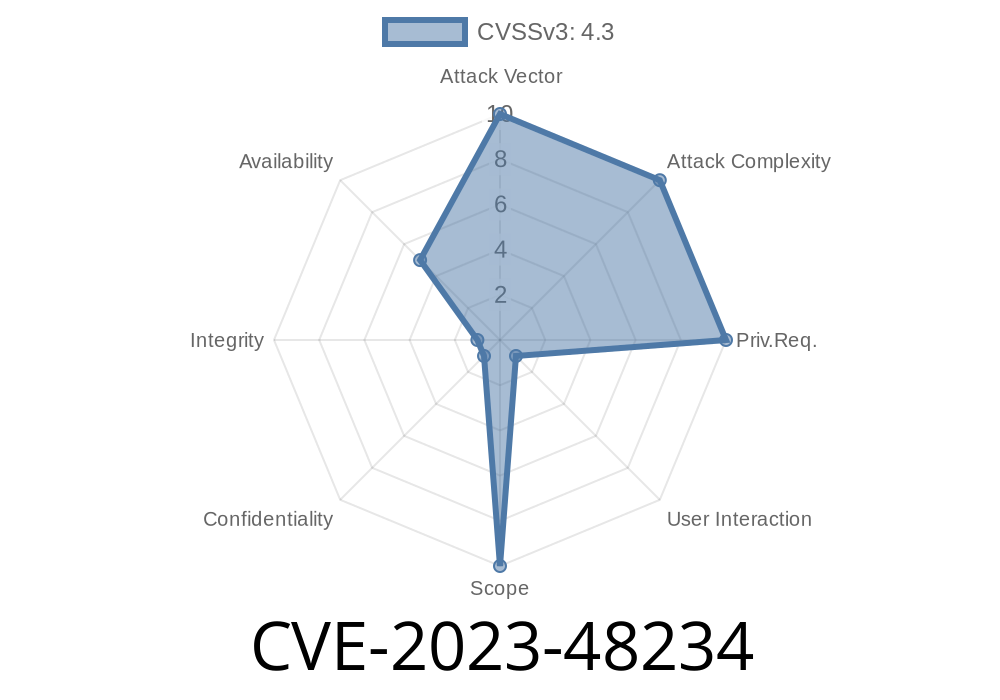
Vim is one of the most popular and powerful command-line text editors used by millions of developers and system administrators. But even mature tools like Vim sometimes have bugs. One such issue, tracked as CVE-2023-48234, was discovered and fixed in late 2023. Let’s dive in and understand what this vulnerability is all about.
What is CVE-2023-48234?
CVE-2023-48234 is a security issue in Vim related to how it handles large counts in the normal mode z command. Normally, the z command in Vim lets you scroll lines or reposition your view inside a file. You can prefix it with a number (the “count”) to control how much to move. But if you give it an extremely large count, Vim could overflow its internal value.
The bottom line:
This overflow could crash Vim or behave in unexpected ways, though the impact is low and needs user interaction—typically a user entering a massive count for a z command.
The Vulnerable Code
Here’s a simplified version of what went wrong (not the exact Vim source, but enough to get the idea):
// Sketch of vulnerable code
void do_z_command(int count)
{
// count comes from user input, like "9999999999z<CR>"
int lines_to_scroll = count;
// ... do something with lines_to_scroll ...
}
If someone runs a command like
9999999999z<Enter>
That’s more than int can handle on many systems, causing an integer overflow.
Exploiting the Bug
Realistically, this isn't a big risk for end users. An attacker would have to trick *you* into typing a huge number before the z command (something like 9999999999z<Enter>). In most cases, this will just crash Vim or do nothing at all. But it's still a bug that deserves fixing.
Here's an example you can test out (not recommended, unless you’re just experimenting with a safe, up-to-date Vim):
:9999999999z
On a vulnerable Vim version, this *might* crash the editor, or simply be ignored, depending on your setup.
Fix and Solution
Bram Moolenaar (Vim’s creator) and the Vim team fixed this in commit 58f9befca1:
> "Prevent potential overflow when getting the count for a normal mode z command."
Released in
The fix is included in release Vim 9..2109.
Recommendations
Upgrade immediately:
If you use Vim frequently, update to version 9..2109 or later. Most package managers will get you there with a normal system update.
- If you build from source, get the latest code.
`sh
sudo apt update && sudo apt upgrade vim # Debian/Ubuntu
sudo dnf upgrade vim # Fedora
brew upgrade vim # macOS/Homebrew
`
No workaround:
There is no workaround for this bug. The only way to be safe is to update.
---
## References
- GitHub – Vim commit fixing overflow
- Vim 9..2109 Release Notes
- CVE-2023-48234 in MITRE database
---
## The Takeaway
CVE-2023-48234 is a textbook example of how even simple overflow bugs can sneak into trusted tools. While this one is low risk and unlikely to be exploited “in the wild,” it’s still important to keep your text editor up to date—especially with security in mind. Don’t wait, upgrade your Vim now!
Timeline
Published on: 11/16/2023 23:15:09 UTC
Last modified on: 01/25/2024 21:33:46 UTC