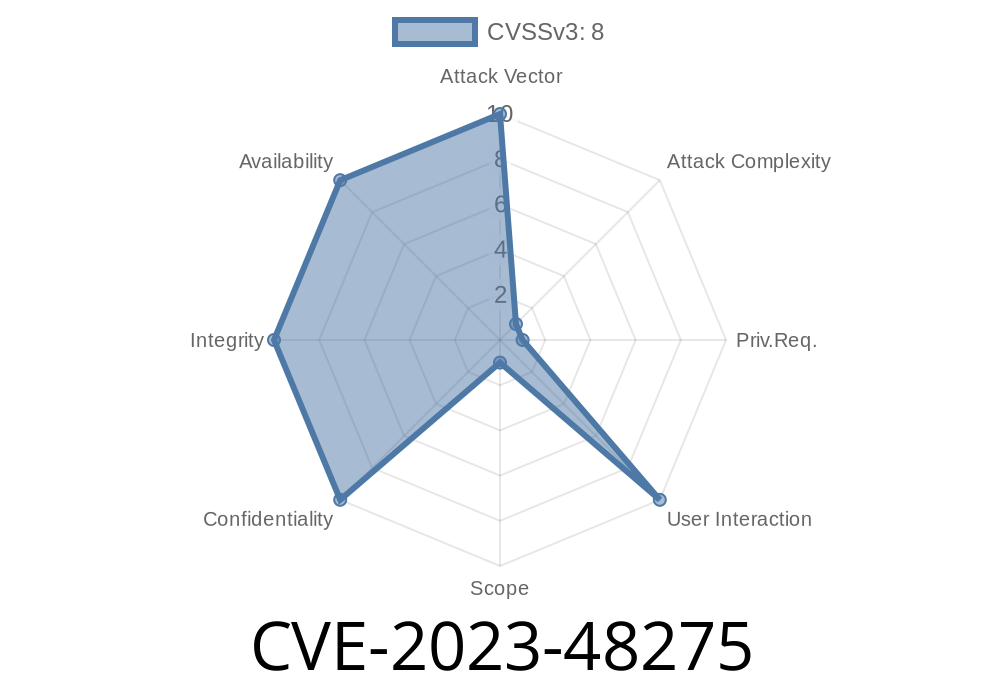
If you use Google Reviews on your website through the Trustindex.io Widgets for Google Reviews plugin, pay close attention. There’s a serious vulnerability—CVE-2023-48275—that could let hackers upload dangerous files to your server, putting your whole website and visitors at major risk.
This post breaks down what this vulnerability means, how an attack works, includes code snippets for better understanding, and what you should do right away.
What Is CVE-2023-48275?
CVE-2023-48275 is a type of security flaw known as “Unrestricted Upload of File with Dangerous Type.” Specifically, in versions up to 11..2 of the Trustindex.io “Widgets for Google Reviews” WordPress plugin, the software does not properly check files that are uploaded through its widget interface. Instead of making sure the uploaded files are safe images or documents, it just moves along and lets almost any file type get uploaded—including files that could hurt your server.
How Does the Attack Work?
Attackers can exploit this vulnerability by uploading a malicious file (like a PHP script) that the server then saves somewhere accessible online. Once there, the script could:
The Typical Exploit Scenario
1. Find an Upload Endpoint: The plugin provides a place to upload files (like for avatars or logos).
2. Upload a Malicious File: Instead of an image, the attacker uploads something dangerous likehack.php.
3. Access the File: Because the plugin doesn’t properly restrict access, the attacker goes to https://your-site.com/wp-content/uploads/hack.php and now controls code on your server.
The plugin's file upload code might look something like this
if (isset($_FILES['file'])) {
$upload_dir = '/var/www/html/wp-content/uploads/';
$file_name = $_FILES['file']['name'];
// Vulnerable: No type or extension check
move_uploaded_file($_FILES['file']['tmp_name'], $upload_dir . $file_name);
echo "Upload successful!";
}
What's wrong? There’s NO check to make sure the file is really an image or a safe file! Hackers could upload evil.php or shell.exe.
Here’s how an attacker could upload a PHP backdoor
curl -F "file=@shell.php" https://victim-site.com/wp-admin/admin-ajax.php?action=trustindex_upload
Once uploaded, the attacker just visits
https://victim-site.com/wp-content/uploads/shell.php
Defense: How To Fix or Protect Yourself
1. Update the Plugin
Check for any newer versions of Widgets for Google Reviews at WordPress.org or Trustindex.io’s website and apply updates immediately.
2. Disable or Remove the Plugin
If you can’t update, disable or uninstall the plugin until a fix is available.
3. Restrict Upload Types (Example Patch)
If you know what you’re doing, you can try patching the plugin
$allowed = ['jpg', 'jpeg', 'png', 'gif'];
$ext = strtolower(pathinfo($_FILES['file']['name'], PATHINFO_EXTENSION));
if (in_array($ext, $allowed)) {
move_uploaded_file($_FILES['file']['tmp_name'], $upload_dir . $file_name);
} else {
echo "Invalid file type!";
}
4. Monitor Your Uploads Directory
Keep an eye on new files in your uploads folder. Remove any unexpected PHP or executable files.
References
- CVE-2023-48275 in NVD
- Trustindex.io Plugin page
- Wordfence advisory about file upload vulnerabilities
Don’t Wait: Act Now
Vulnerabilities like CVE-2023-48275 are prime targets for attackers—they are often exploited in real hacks. Protect your site, customers, and reputation by patching immediately. If you need more info or help, consult with your web developer or hosting provider.
If you found this post helpful, share it with others who might be at risk! Stay safe online!
Timeline
Published on: 03/26/2024 21:15:52 UTC
Last modified on: 03/27/2024 12:29:30 UTC