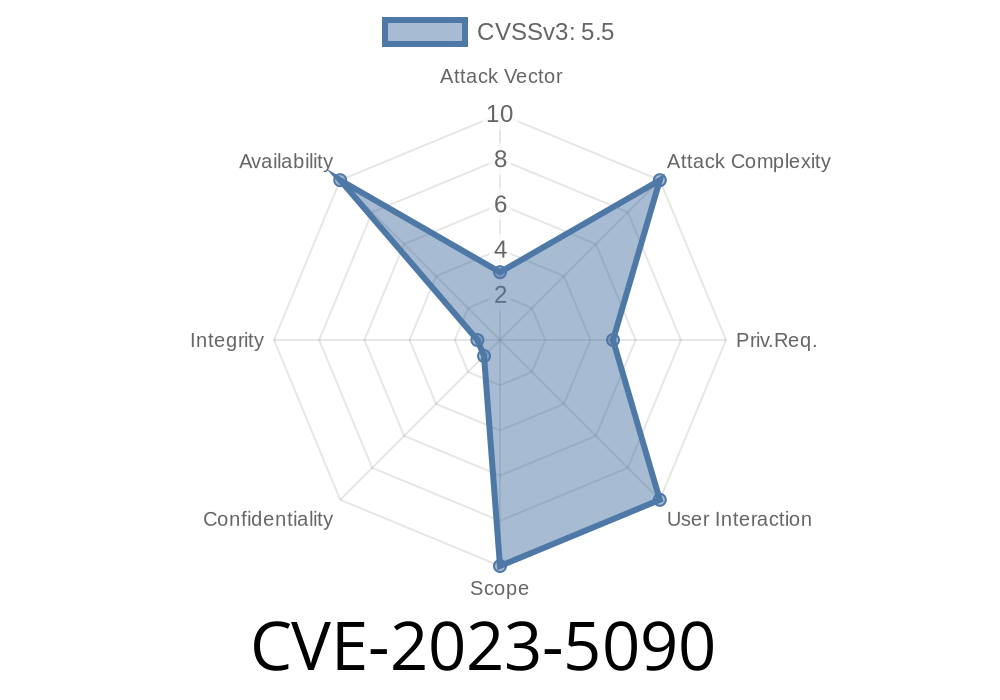
A recently discovered vulnerability (CVE-2023-5090) within the Kernel-based Virtual Machine (KVM) has been determined to allow direct access to host x2apic msrs when a guest resets its APIC. This flaw, which resides in an improper check in the svm_set_x2apic_msr_interception() function, can potentially lead to a denial of service (DoS) condition. In this article, we will delve deeper into the details of this vulnerability, discussing its potential ramifications, examining the code involved, and highlighting critical information about available patches.
Background
KVM is an open-source hypervisor for Linux-based systems, enabling users to run multiple virtual machines (VMs) on a single host machine. It is worth noting that KVM is widely used in a variety of environments, making this vulnerability especially concerning.
Exploit Details
The core of this vulnerability is the improper check found in the svm_set_x2apic_msr_interception() function, which can grant direct access to host x2apic msrs when the guest system resets its APIC. The direct access could potentially lead to a DoS condition, which can have significant ramifications on the target system.
Here is a code snippet for a better understanding of the flaw
static void svm_set_x2apic_msr_interception(struct vcpu_svm *svm)
{
struct kvm_msr_entry *msr;
...
msr = find_msr_entry(svm->apic->vapic_indirect, SVM_REGISTERS);
if (msr) {
...
} else {
msr = kzalloc(sizeof(struct kvm_msr_entry), GFP_KERNEL);
...
}
msr->index = SVM_REGISTERS;
msr->data = ;
}
As shown in the code snippet, the function does not properly handle an improper check, which allows direct access to host x2apic msrs when the guest system resets its APIC.
Original References
The original report about this vulnerability, along with a detailed analysis and commit history, can be found at two key sources: The Official Linux Kernel Mailing List (LKML) and the National Institute of Standards and Technology's National Vulnerability Database (NVD).
- LKML Source
- NVD Source
Patch Information
A patch addressing this vulnerability is already available and has been incorporated into the mainline Linux kernel, starting from version 5.14.rc1. It is highly recommended that affected users update their KVM software to the latest version as soon as possible, ensuring the necessary patches have been applied.
Patch commit: https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=755d067f32a2af562aecf2555e718d623ffee6c2
Conclusion
CVE-2023-5090 is a critical vulnerability in KVM, with the potential to lead to DoS conditions. Security professionals and system administrators should prioritize addressing this issue through the application of necessary patches. As always, it is essential to keep software up-to-date and maintain vigilance for potential exploits.
Timeline
Published on: 11/06/2023 11:15:09 UTC
Last modified on: 11/14/2023 17:01:37 UTC