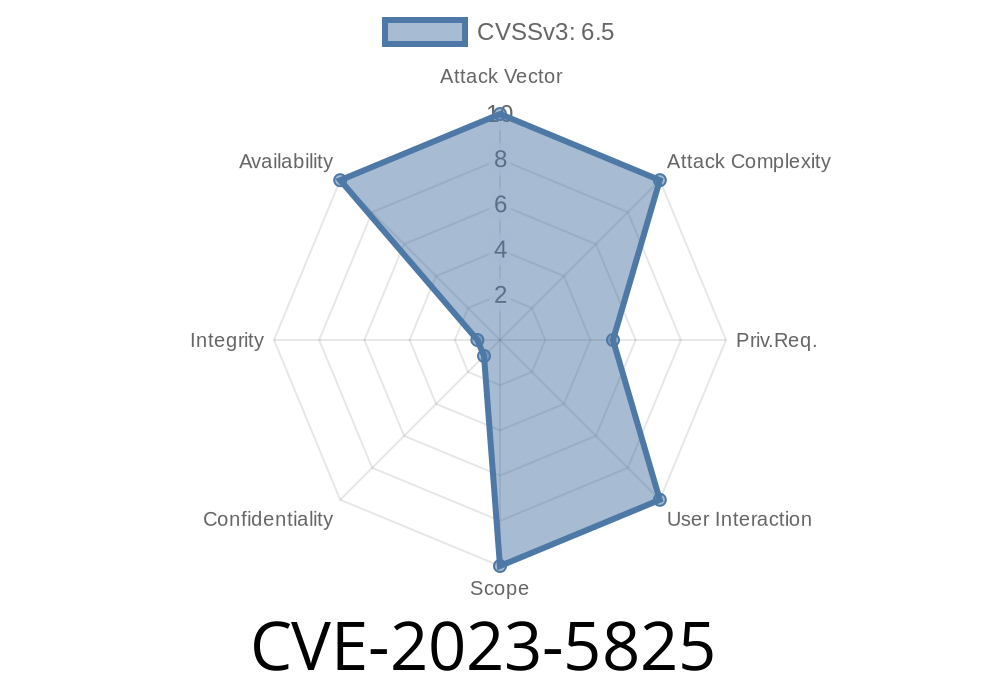
In late 2023, a critical security flaw was discovered in the GitLab Community Edition (CE) and Enterprise Edition (EE). Tracked as CVE-2023-5825, this issue can let a low-privileged user trigger a Denial of Service (DoS) by abusing the way GitLab’s CI/CD pipeline handles certain component definitions. In this article, I’ll walk you through what the bug is, how it’s exploited, which versions are affected, some example code, and offer tips for staying protected.
What is CVE-2023-5825?
CVE-2023-5825 is a Denial of Service vulnerability in GitLab’s CI/CD system. A low-privileged user (someone with restricted access, not a GitLab admin) can make the server run out of available memory. How? By setting a component in a CI/CD file (like .gitlab-ci.yml) to point at an incorrect or malicious path. This causes the server to enter an “infinite loop,” eating up all its RAM and making it unavailable for everyone.
How Does the Exploit Work?
To understand the exploit, let’s briefly look at how GitLab manages CI/CD pipelines. When you define a pipeline, you can pull in components with the include keyword like this:
include:
- project: 'my-group/my-components'
file: '/ci-templates/deploy.yml'
Suppose an attacker changes the file path to something invalid or loops back to the file itself. In vulnerable versions, GitLab tries to repeatedly resolve the include, which never succeeds, and keeps trying — forever, or until memory runs out.
Here’s how an attacker might abuse the bug. They simply tweak their .gitlab-ci.yml like this
# .gitlab-ci.yml
include:
- project: 'my-group/my-components'
file: '/ci-templates/this-file-points-back.yml'
Then, in this-file-points-back.yml, put
include:
- project: 'my-group/my-components'
file: '/ci-templates/this-file-points-back.yml' # Points to itself!
Dive Into the Patch
The GitLab team fixed this by adding extra checks to make sure CI/CD component includes don’t end up in a recursive resolution loop. Basically, they keep track of which files are already loaded, and if they see the same include path, they stop processing and throw an error instead.
If you want to review the patch, check
- GitLab MR for 16.3.6
- GitLab 16.4.2 Release Notes
- Official CVE Tracker
A Real Exploit Scenario
Let’s say Bob is a developer with basic write access to a project. He commits a malicious .gitlab-ci.yml. When the pipeline runs, the GitLab instance starts eating RAM. Eventually, the server may be killed by its own operating system (usually via the out-of-memory, or OOM, killer). Other users cannot push, pull, or access the web UI. If this is a public-facing instance, any attacker with write access to _any_ project can take down your whole GitLab server.
Upgrade to at least 16.3.6, 16.4.2, or 16.5.1 (or newer)
Audit Who Has Write Access
- Remove unnecessary CI/CD write or maintainer access, especially for public/self-service projects.
Monitor Server Health
- Watch for spikes in CPU/MEM that could point to a DoS attack.
References
- GitLab Security Release: 16.3.6, 16.4.2, 16.5.1
- National Vulnerability Database: CVE-2023-5825
- GitLab Update Guide
- GitLab CI/CD Includes Documentation
Conclusion
CVE-2023-5825 is a classic example of how complex dependency and include mechanisms can backfire if not handled carefully. If you run GitLab, make updating a priority. Don’t wait to become a victim—Denial of Service bugs are easy to exploit and impact everyone. Secure your instance, audit your pipeline access, and always keep your software current!
If you need help, check the official GitLab documentation or contact your vendor for support.
Timeline
Published on: 11/06/2023 11:15:09 UTC
Last modified on: 11/14/2023 17:00:25 UTC