Discovered vulnerability: Stored Cross-Site Scripting (XSS) in ChatBot for WordPress
Affected versions: 4.8.6 to 4.9.6
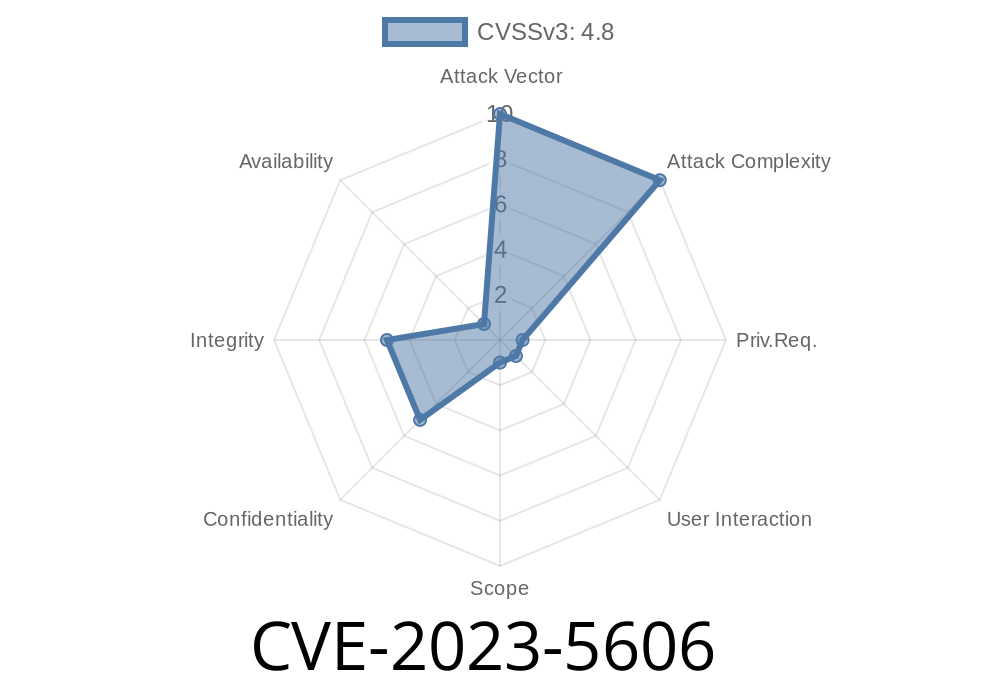
CVE: CVE-2023-5606
Impact: Authenticated administrators may inject malicious scripts into FAQ Builder.
Special conditions: Only impacts WordPress MultiSite or installs where unfiltered_html is _disabled_.
Background
In early 2024, a critical vulnerability was discovered in the popular ChatBot for WordPress plugin through its FAQ Builder feature. Wordfence and the National Vulnerability Database (NVD) documented this as a “Stored Cross-Site Scripting” (XSS) risk. Although only users with administrator-level permissions could exploit it, this could have severe consequences, especially in environments where super administrators delegate some site admin rights on MultiSite setups or restrict unfiltered_html in standard installs.
> Note: This flaw is a re-introduction of CVE-2023-4253. Always keep plugins updated!
How the Vulnerability Works
Stored XSS happens when user-supplied HTML or JavaScript code is saved to the database and later rendered in the web interface without proper filtering or escaping. In this case, the ChatBot FAQ Builder did not sanitize input fields properly or escape output, allowing admins to inject code.
`html
The FAQ saves this input without filtering.
4. Any user visiting the FAQ page executes the injected script, potentially exposing cookies, session data, or providing a vector to redirect users, deface content, or perform further attacks.
Save the entry.
5. Visit the FAQ page from any browser/account (even as another admin or user).
(b) On a MultiSite install, admin accounts may be delegated, increasing the attack surface.
- (c) Sites with unfiltered_html disabled intend to *limit* XSS risk, but this bug reintroduces it.
Technical Walkthrough
The vulnerable code did not call sanitize_text_field(), wp_kses(), or compatible output escaping functions when rendering FAQ fields. This meant that code like:
echo $faq_question; // Not escaped!
… would allow script tags to output directly to the browser.
References
- Original Plugin in WordPress.org
- NVD Entry for CVE-2023-5606
- Wordfence Advisory 3dce523c-6ac3-46d6-8c88-0367ce47175c
- XSS in WordPress Plugins – OWASP Guide
Update to ChatBot for WordPress 4.9.7 or later.
2. Run regular security scans with Wordfence or WPScan.
Summary
CVE-2023-5606 shows even site admins can be a risk, especially in big teams or managed WordPress multisite environments. Careless input or a single compromised account can open doors for further attacks. Always keep plugins up to date, validate user inputs, and escape outputs—don’t assume your admin area is immune to malicious code!
Timeline
Published on: 11/02/2023 09:15:08 UTC
Last modified on: 11/09/2023 17:47:16 UTC