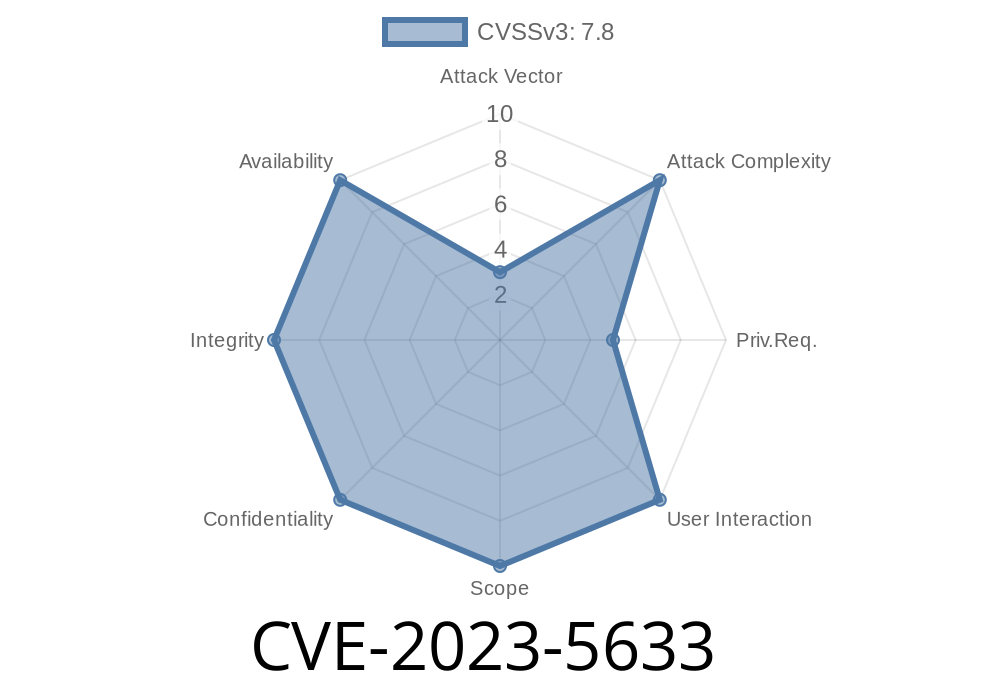
In late 2023, a new security vulnerability named CVE-2023-5633 was discovered in systems running VMware's 3D acceleration. This bug is dangerous because it could let a regular user inside the VMware guest gain higher privileges—possibly even root access—by exploiting a flaw in how memory objects are handled.
This post will break down what CVE-2023-5633 is, why it happened, how attackers might exploit it, and how you can protect your systems. We’ll use simple language and show code snippets for a better understanding.
What is CVE-2023-5633?
CVE-2023-5633 is a use-after-free vulnerability. This means the program frees up ("deletes") a chunk of memory but still tries to use it later on. If the attacker is sneaky enough, they can take over this chunk of memory and trick the program into doing harmful things.
The bug appeared after fixing two earlier issues: CVE-2023-33951 and CVE-2023-33952. The changes made to fix those exposed the new flaw.
Affected systems:
How Did This Happen?
The root problem is how VMware’s virtual graphics driver (often called "vmwgfx" in Linux) manages memory objects used for rendering 3D surfaces. When a surface is created, the driver stores the surface info inside a memory object. A "reference count" (called "refcount") is supposed to track how many users are using this memory.
Fixes for the older vulnerabilities changed how the refcount was managed, but accidentally left a state where the memory object could be freed (deleted) while still being used. When the system tried to use the now-freed memory, it could be hijacked—potentially by a low-level attacker.
Here’s a very simplified C-style pseudocode to help visualize the issue
struct memory_object {
int refcount;
void *data;
};
void release_memory(struct memory_object *obj) {
obj->refcount--;
if (obj->refcount == ) {
free(obj->data);
free(obj); // Problem starts here if someone still has a pointer to obj!
}
}
void use_object(struct memory_object *obj) {
// SAFE if object exists, DANGEROUS if it was just freed!
do_something(obj->data);
}
If release_memory() is called twice (due to logic mistakes after those earlier patches), obj gets freed while maybe another function still tries to use obj, leading to use-after-free.
Real Exploit Scenario
Imagine you’re an ordinary user in a Linux guest VM on VMware, with 3D acceleration enabled. You don’t need any special access.
Step-by-step exploit (conceptually)
1. Trigger the bug: Create and destroy surfaces quickly, trying to hit the use-after-free condition.
2. Heap spray: Quickly allocate your own crafted data hoping it will land where the old surface object was.
3. Privilege escalation: When the driver uses what it thinks is the old object, it’s actually running code you’ve supplied, possibly leading to kernel code execution.
Potential impact:
Here’s an outline—not an actual working exploit
void spray() {
// Allocate many fake objects in user memory to replace freed memory.
for (int i = ; i < 10000; i++) {
struct memory_object *fake = malloc(sizeof(struct memory_object));
fake->data = some_controlled_payload;
}
}
int main() {
struct memory_object *surf = create_surface();
release_memory(surf); // First free
spray(); // Heap spray to try and get our object in the same place
use_object(surf); // Will now (hopefully) use attacker-controlled memory!
return ;
}
Note: The real exploit would be much more complex and require understanding kernel structures, but this illustrates the approach.
References
- CVE-2023-5633 on NIST NVD
- CVE-2023-33951 NVD Record
- CVE-2023-33952 NVD Record
- VMware 3D acceleration security advisories (search for related terms)
- Red Hat Security Blog: use-after-free vulnerabilities
How to Protect Your Systems
- Patch your VM guests and hosts: If you use VMware with 3D acceleration, make sure you apply the latest patches from your OS or VMware vendor.
- Disable 3D acceleration for risky guests: If you don’t need hardware graphics, turn off 3D acceleration in the VM settings.
Conclusion
CVE-2023-5633 reminds us how old problems can come back when fixing others. A change to handle reference counts led to a much more dangerous use-after-free bug—one that could let regular users hijack privileges inside a VMware guest.
Always patch quickly, monitor your usage of advanced features like 3D acceleration, and stay alert for newly disclosed vulnerabilities in the tools you use.
Timeline
Published on: 10/23/2023 22:15:09 UTC
Last modified on: 01/10/2024 15:15:10 UTC