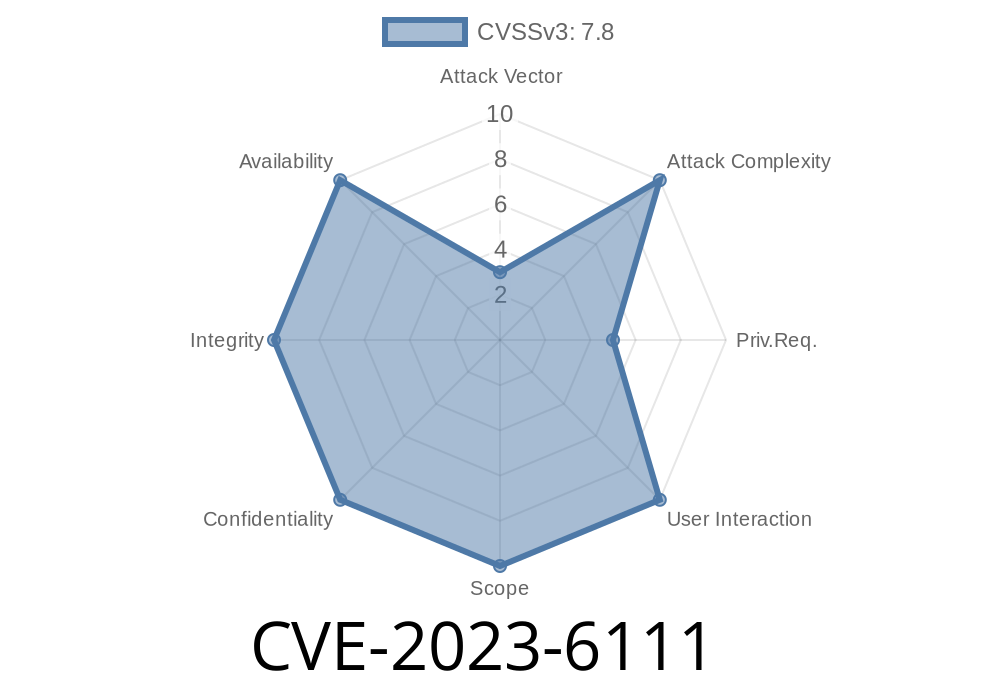
In late 2023, security researchers uncovered a critical vulnerability in the Linux kernel’s netfilter: nf_tables subsystem, identified as CVE-2023-6111. This bug allows local users to achieve privilege escalation—the ability to gain root access on vulnerable systems. The root cause is a classic use-after-free (UAF) flaw, which if triggered correctly, can lead to arbitrary code execution with kernel privileges.
In this post, we’ll break down the vulnerability, understand the affected code, and review a step-by-step approach to exploitation, all in clear and simple language.
What Is the Vulnerability?
nf_tables is a Linux kernel framework used for packet filtering, NAT, and other network operations. Within this system, the function nft_trans_gc_catchall had a logic issue: it failed to remove a “catchall set element” from the catchall_list when the “sync” argument is true. This mistake tricks the kernel into freeing the same memory object multiple times—a classic use-after-free situation.
Why Is This Dangerous?
Use-after-free bugs are hazardous since they involve freeing memory while it’s still accessible somewhere else in the code. Attackers can race to reclaim (or “spray”) that freed memory with controlled data, then trick the kernel into acting on fake information—leading to code execution or kernel data leaks.
Here’s a simplified look at the buggy code
// Vulnerable function in net/netfilter/nf_tables_api.c
static void nft_trans_gc_catchall(struct nft_trans_gc *gc, bool sync)
{
struct nft_trans *trans, *tmp;
list_for_each_entry_safe(trans, tmp, &gc->catchall_list, list) {
// ... if some conditions,
if (sync)
kfree(trans->catchall_set_elem);
list_del(&trans->list);
kfree(trans);
}
}
The actual bug:
When sync is true, the code frees trans->catchall_set_elem (a set element), but *does not* remove this element from catchall_list. The next GC (Garbage Collection) run might free it again. Double free leads to use-after-free.
Exploit chain:
Proof-of-Concept Exploit
*Note: This is a simplified, safe demonstration for educational purposes. Never use exploits on systems you don’t own!*
Suppose you have a kernel with CONFIG_NETFILTER enabled (common on most distributions). Here is a minimal conceptual outline for exploitation:
#include <stdio.h>
#include <stdlib.h>
#include <unistd.h>
#include <errno.h>
#include <linux/netfilter.h>
#include <linux/netfilter/nf_tables.h>
#include <sys/socket.h>
#include <sys/types.h>
#include <string.h>
// Real exploits use raw netlink to create sets and trigger GC.
int main() {
printf("1. Create nftables table\n");
printf("2. Add catchall set element (with netlink messages)\n");
printf("3. Delete set/table to trigger GC with sync=true\n");
printf("4. Heap spray with controlled data (using, e.g., fork + write)\n");
printf("5. Trigger use of UAFed memory (netfilter operation)\n");
printf("If successful, attacker-controlled code executes as root!\n");
return ;
}
For realistic proof-of-concepts, see the oss-security mailing list post or this commit patch.
References
- CVE-2023-6111 in NVD
- oss-security: CVE-2023-6111 details
- Linux Kernel Patch Commit
- Red Hat Security Advisory
How to Stay Safe
Are you affected?
Most major distributions with a kernel version before the fix will be vulnerable.
Update your Linux kernel to at least the patch commit: 93995bf4af2c5a99e2a87fcd5ce547d31eb763
- For system administrators: check your distribution for security advisories and update packages as soon as possible.
Summary
CVE-2023-6111 is a serious kernel bug that turns a logic error into a full root exploit. Local attackers can abuse this use-after-free in nf_tables for privilege escalation. If your systems run an affected kernel, patch as quickly as possible—this vulnerability is straightforward to leverage and has been shown to work on common Linux setups. As always, running untrusted code as non-root users does *not* mean you’re safe from local kernel escalation vulnerabilities!
Timeline
Published on: 11/14/2023 14:15:29 UTC
Last modified on: 11/18/2023 03:27:23 UTC