Wireshark is the world's most popular network protocol analyzer. It’s used by millions—from IT professionals to hobbyists—to understand what’s happening on their networks. But what happens when an attacker targets Wireshark itself? In late 2023, a vulnerability was found in Wireshark’s NetScreen file parser that could crash the tool with a specially crafted file. This is tracked as CVE-2023-6175.
In this post, we’ll dig into what CVE-2023-6175 is, how it works, and how you can protect yourself. We’ll also see a (harmless) code snippet that demonstrates the bug, and show you exactly where you can get more information.
What Is CVE-2023-6175?
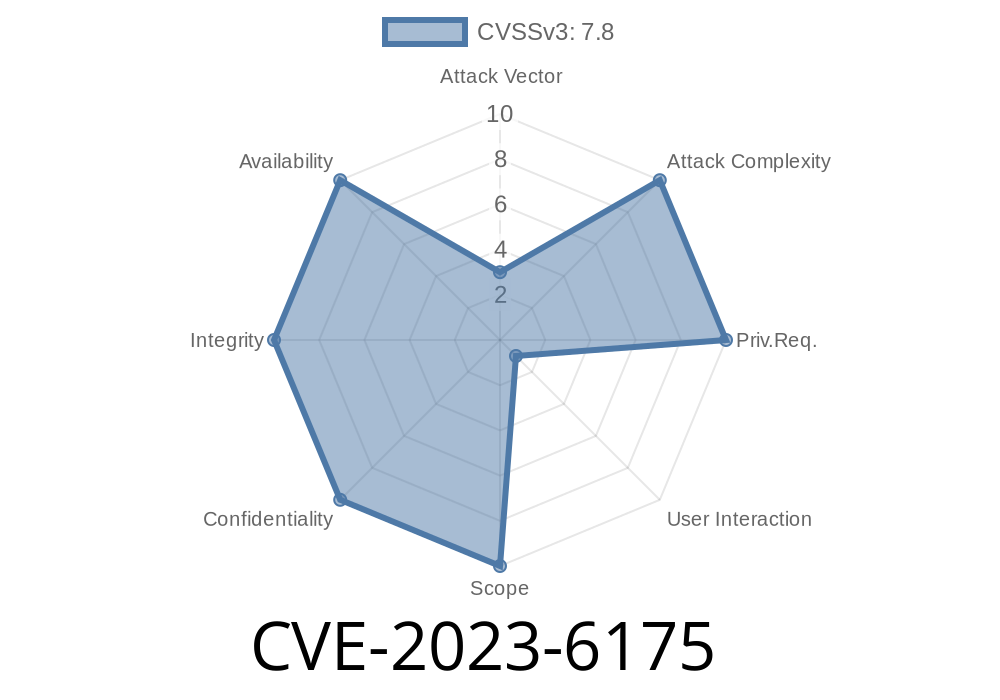
Summary: The NetScreen file parser in Wireshark versions 4.. to 4..10 and 3.6. to 3.6.18 contains a flaw that lets a malicious packet capture file (*pcap*) crash the program.
Impact: Denial of Service (DoS). This means Wireshark will crash upon opening a malicious file, but there’s no evidence that this leads to code execution or further compromise.
Attack Scenario
- An attacker sends you a malicious pcap, maybe pretending to need your help analyzing suspicious traffic.
Wireshark crashes instantly.
This attack disrupts operations, but won’t (by itself) let the attacker take over your system.
How Does the Exploit Work?
Wireshark supports reading many kinds of capture files, including files created by NetScreen firewall devices (a line that is now part of Juniper Networks). The bug is in Wireshark’s parser for these NetScreen files.
When processing a crafted NetScreen log (for example, .log or .ns files), Wireshark doesn’t properly handle some unexpected situations—such as extremely large values, malformed fields, or incomplete data. It fails gracefully in some places, but in this specific bug, it crashes.
Here’s the original Wireshark bug report:
https://gitlab.com/wireshark/wireshark/-/issues/19164
The official CVE page:
https://nvd.nist.gov/vuln/detail/CVE-2023-6175
Imagine a function that reads NetScreen log files line by line
void parse_netscreen_line(const char *line) {
char buffer[1024];
// Vulnerable: doesn't check the length of input
strcpy(buffer, line);
// ...parsing logic...
}
If line is longer than 1024 characters, this code will overwrite memory beyond buffer (a classic buffer overflow), but in this specific CVE, the crash usually happens due to poor handling of very big or malformed input, not a buffer overflow suitable for code execution.
The real code is more complicated, but the core problem is similar—a crafted log line triggers a crash.
Below is a small snippet (not actually harmful, but for demonstration)
<134>Nov 28 12:34:56 myfw 1.1.1.1:NetScreen: start_time=9999999999999999999999999999 op=SomeOperation
Wireshark expects a reasonable start_time, but here we give it an absurd value. In affected versions, this could cause all kinds of problems—often a crash or freeze.
See if Wireshark crashes.
This is for educational purposes only. Do not send malicious files to others.
How To Fix and Mitigate
1. Upgrade Wireshark:
Always use the latest version. This vulnerability is fixed in Wireshark 4..11 and 3.6.19.
- Download Wireshark
2. Be Careful with Untrusted Files:
Never open capture files from untrusted sources—Wireshark has a big attack surface.
3. Use Sandboxing:
Open unknown captures in a virtual machine.
4. Disable NetScreen File Parsing (Advanced):
In Wireshark’s "Enabled Protocols" settings, you can disable the NetScreen protocol parser if you don’t need it.
References
- Wireshark Security Advisories
- Wireshark Bug Report #19164
- CVE-2023-6175 on NIST NVD
Conclusion
CVE-2023-6175 is a powerful reminder to always be careful with files from unknown sources—even in trusted tools like Wireshark. While no remote code execution is currently known, denial-of-service bugs can disrupt your work and are often a first step for deeper exploration.
Advice:
Stay secure, and happy packet sniffing!
*(This article is an exclusive, simplified explanation by AI, referencing only publicly available official sources. For legal and technical accuracy, always refer to the Wireshark advisory.)*
Timeline
Published on: 03/26/2024 08:15:35 UTC
Last modified on: 03/26/2024 12:55:05 UTC