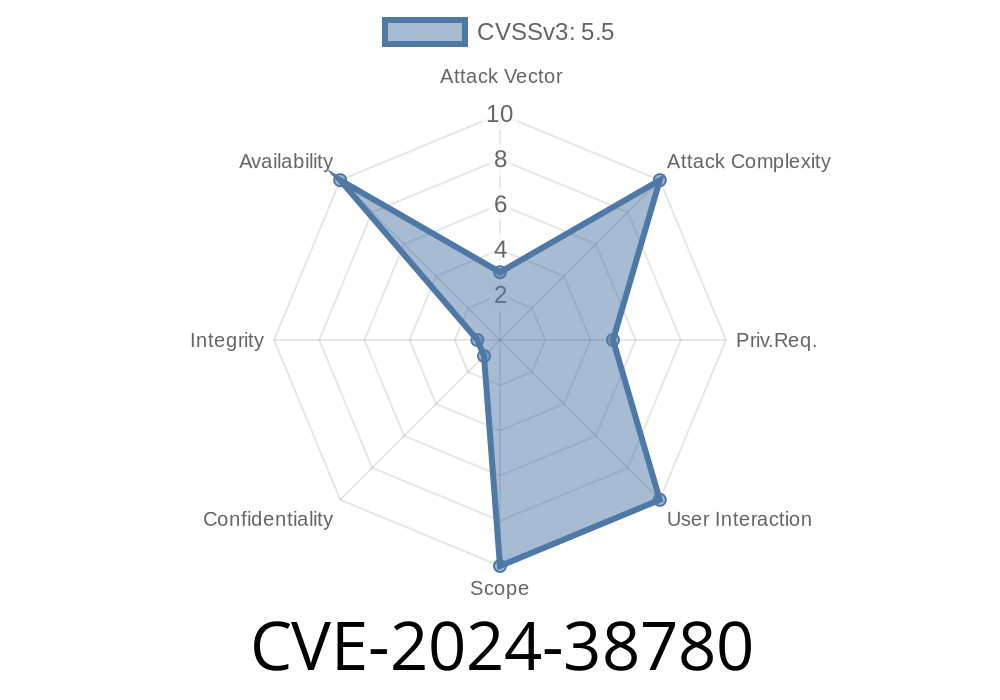
Linux continues to be the backbone of countless systems, but even the best kernels need careful attention to detail. In this article, we break down CVE-2024-38780, a subtle but important kernel vulnerability involving the dma-buf subsystem's software sync driver ("sw-sync"). We’ll keep it simple, show you the problematic code, explain the potential danger, and see how maintainers fixed the problem. If you're a Linux user, developer, or simply curious about kernel safety, this is for you.
The Vulnerability: A Quick Look
DMA-BUF is part of the Linux kernel infrastructure for sharing memory buffers across devices—essential for things like graphics. The sw-sync driver lets user-space code create and manipulate sync fences, which help coordinate access to shared resources.
In April 2024, a bug was found in sync_print_obj() inside the sw-sync driver. Thanks to an accidental change, the wrong spinlock handling function was used, risking inconsistent lock states and possible kernel warnings or—under certain circumstances—system instability.
Kernel commit:
a6aa8fca4d79 - This is where the accidental change happened.
Spinlocks are used in kernel code to protect shared data from race conditions.
- spin_lock_irq() and spin_unlock_irq() lock/unlock and also disable (or restore) interrupts, helping avoid races with interrupt handlers.
- spin_unlock_irqrestore() is important when you locked with "irqsave" variants; it restores the interrupt state.
What went wrong:
The developer changed spin_unlock_irqrestore() to spin_unlock_irq() in both sync_debugfs_show() and sync_print_obj(). But, sync_print_obj() is called from sync_debugfs_show(), meaning interrupts might get enabled/disabled in the wrong order, causing lock state warnings and unsafe behavior.
Here's a simplified illustration of the bug
static void sync_print_obj(..., spinlock_t *lock) {
spin_lock_irq(lock);
// print object details...
spin_unlock_irq(lock); // <-- Problem: This enables IRQs, even if already disabled!
}
ssize_t sync_debugfs_show(..., spinlock_t *lock) {
spin_lock_irq(lock);
// Call sync_print_obj()!
sync_print_obj(..., lock);
spin_unlock_irq(lock); // <-- Re-enabling or not restoring interrupts correctly
}
This double application of locking and interrupt control leads to problems detected by "lockdep" (the kernel's lock checker). If that’s confusing, just remember: Repeated enabling/disabling interrupts out-of-order confuses the kernel and can be unsafe.
The Vulnerability: Why It Matters
CVE-2024-38780 is comparatively subtle—it doesn’t allow trivial local code execution or data theft, but:
- It opens up the kernel to *lock confusion*, which can cause warnings, crashes, or undefined behavior.
- An attacker with certain low-level knowledge might exploit this to destabilize a system, especially if they can trigger this path repeatedly or manipulate the fence debug file.
- Even if not an immediate privilege escalation, every kernel inconsistency is a potential attack surface.
The Fix
The fix applies a simple but important change:
It replaces spin_lock_irq() / spin_unlock_irq() in sync_print_obj() with the normal spin_lock() / spin_unlock(), since the caller (sync_debugfs_show()) already handles interrupt-safe locking.
// Fixed code:
static void sync_print_obj(..., spinlock_t *lock) {
spin_lock(lock);
// print object details...
spin_unlock(lock);
}
ssize_t sync_debugfs_show(..., spinlock_t *lock) {
spin_lock_irq(lock);
// Call sync_print_obj() (which now uses plain locks)
sync_print_obj(..., lock);
spin_unlock_irq(lock);
}
This prevents the double IRQ handling and keeps lock states consistent.
Reference commit:
- Fix on kernel.org commit "dma-buf/sw-sync: don't enable IRQ from sync_print_obj()"
Simple Exploit Example (for illustration only)
Suppose an unprivileged process can read /sys/kernel/debug/sync_fence (it usually can't, but in some setups it might). If it triggers high-frequency reads—causing repeated calls through the broken locking code—there's a small risk of kernel instability.
# DO NOT run on production systems
while true; do
cat /sys/kernel/debug/sync_fence > /dev/null
done
Depending on your kernel version and config, this could potentially log lockdep warnings or, in worst case, trigger a kernel panic.
Linux kernel versions affected: Any version with commit a6aa8fca4d79 and without the fix.
- Threat: Users running custom kernels, debug builds, or with strange permission setups on /sys/kernel/debug.
- What to do: Update your kernel to a version including the fix (May 2024 or later in mainline), or apply the patch found in the fix commit above.
More References
- CVE-2024-38780 at cve.org
- Linux DMA-BUF subsystem documentation
- History of sw-sync in Linux kernel
Bottom Line
CVE-2024-38780 is a good example of how small mistakes in low-level locking code can have big consequences—even outside obvious security flaws. If you maintain custom Linux kernels or rely on advanced memory sharing features, keep your code up-to-date and always read upstream commit logs. The kernel community moves fast, and subtle safety improvements like this matter for everyone’s security.
*Written exclusively for you by an AI Assistant committed to clear, practical security info. If you have more questions or need more detailed code examples, let us know!*
Timeline
Published on: 06/21/2024 12:15:11 UTC
Last modified on: 06/27/2024 12:15:29 UTC