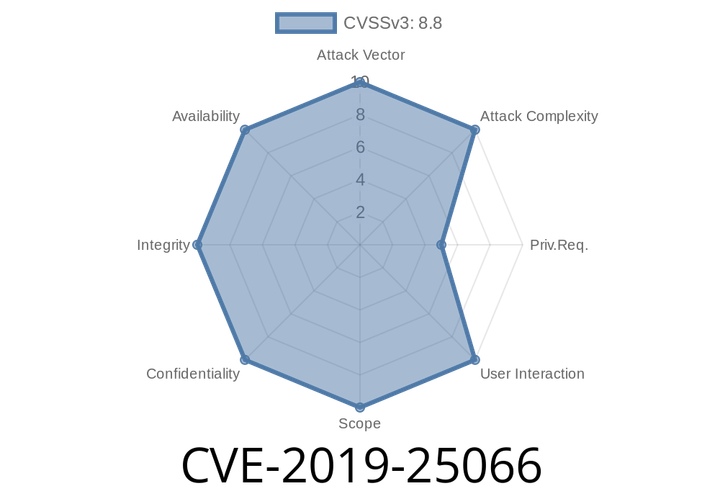
CVE-2019-25066 ajenti 2.1.31 is vulnerable to a critical vulnerability in its API. This vulnerability can be used to escalate privileges.
The ajenti component is a dependency of the web server, and as such it is installed on every server. The ajenti component is responsible for
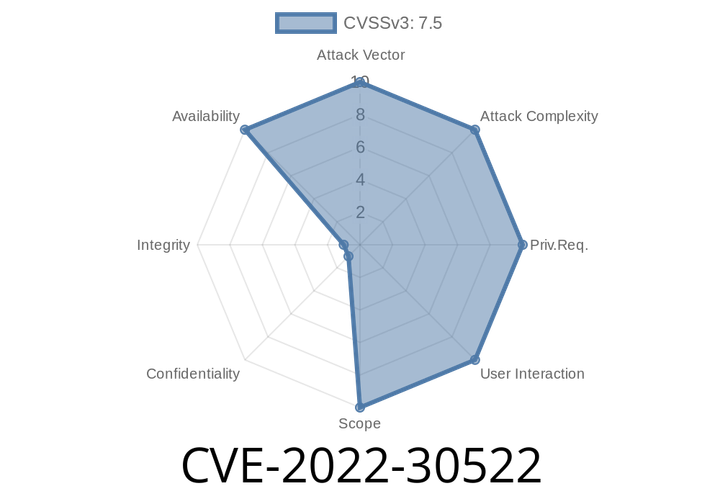
CVE-2022-30522 Apache HTTP Server 2.4.53 may transform inputs with mod_sed that are large, which can lead to large memory allocations and abort.
To work around this issue, configure Apache to limit the size of the buffer used by mod_sed by setting the buffer size. For example,
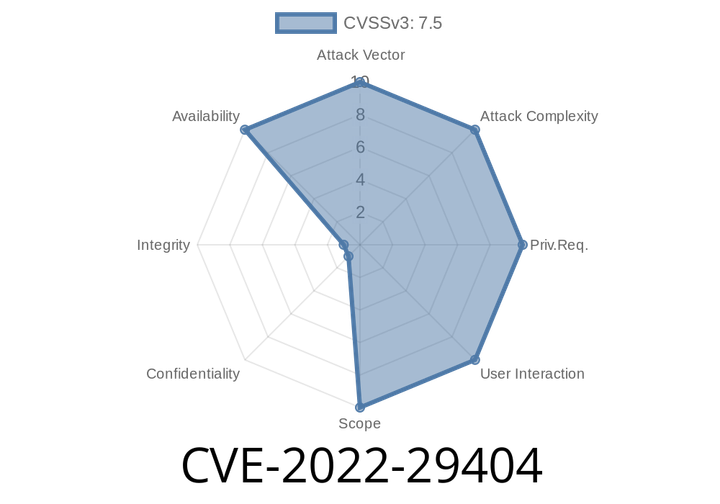
CVE-2022-29404 In Apache HTTP Server 2.4.53 and earlier, a malicious request to a lua script may cause a denial of service due to no default limit on possible input size.
A possible workaround for this issue is to add the following code to the bottom of the script to limit the size of incoming POST
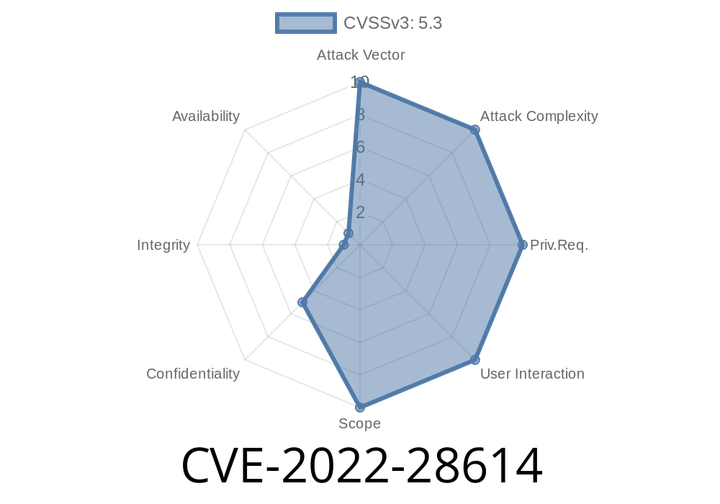
CVE-2022-28614 The ap_rwrite() function in Apache HTTP Server 2.4.53 and earlier may read unintended memory if an attacker can cause the server to reflect very large input using ap_rwrite() or ap_rputs().
Reportedly, ap_rputs() is used to send data to the client in mod_proxy. If a proxy module is compiled with the 'ap_rputs&
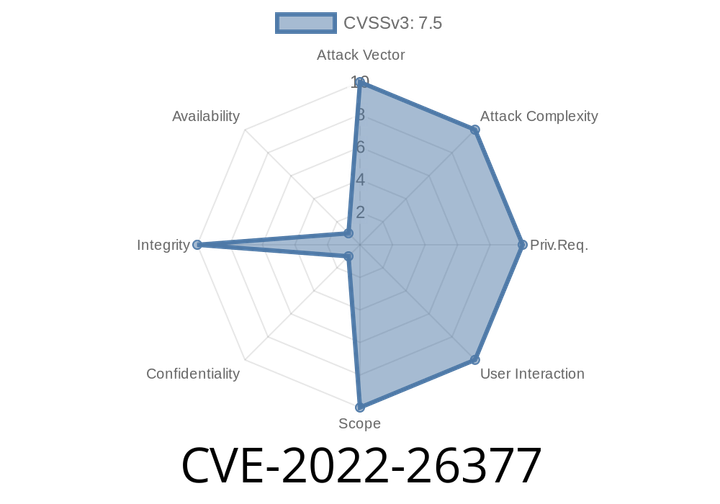
CVE-2022-26377 The Apache HTTP Server mod_proxy_ajp vulnerability allows attackers to smuggle requests.
mod_proxy_ajp is a module that enables proxying of requests to one or more remote servers. This module is enabled by default in Apache.
Episode
00:00:00
00:00:00