CVE-2025-22428 - Critical Android User Permission Escalation Explained (with Code Example & Exploit Details)
---
Android’s user profile system is essential for privacy and security, but a recently discovered vulnerability—CVE-2025-22428—exposes a pathway for apps to gain
CVE-2025-55177 - How WhatsApp’s Device Sync Flaw Exposed iOS and Mac Users to Remote Attacks
In June 2025, security researchers and WhatsApp themselves revealed a significant flaw affecting WhatsApp for iOS, WhatsApp Business for iOS, and WhatsApp for Mac. Tracked
CVE-2025-57819 - Exploiting Unauthenticated Admin Access in FreePBX (Endpoint 15, 16, 17) – Details & Practical Attack Scenarios
FreePBX is a popular open-source VoIP system, widely used for managing voice communications in organizations. It offers a web-based interface for administering PBX functionality. But
CVE-2024-47081 - Critical Credential Leak in Python Requests Library – How to Protect Yourself
Summary:
A severe vulnerability—CVE-2024-47081—affecting the popular Python Requests HTTP library has been discovered. Anyone using Requests versions *before* 2.32.4 could unknowingly
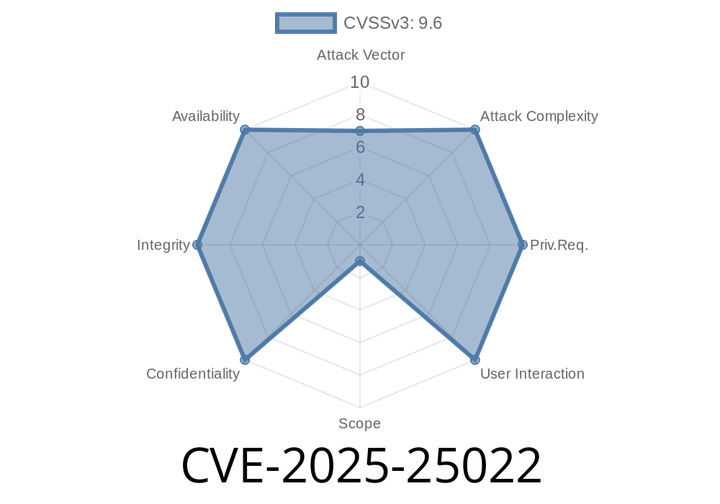
CVE-2025-25022 - Info Leak in IBM QRadar Suite & Cloud Pak for Security – Exploit & Analysis
A new critical vulnerability, CVE-2025-25022, has shaken the cybersecurity world. This flaw affects IBM QRadar Suite Software versions 1.10.12. through 1.11.2.
Episode
00:00:00
00:00:00